
Author: Tanishq Bodh
From Hollywood hacks to $6.75 billion in stolen crypto, the Lazarus Group has evolved from a disruptive nuisance into the most dangerous financial predator in digital asset history. Their latest target: Drift Protocol, drained of $286 million in 12 minutes.
The Lazarus Group is a state-sponsored hacking collective operated by North Korea’s Reconnaissance General Bureau, the country’s primary intelligence agency. Also known as Hidden Cobra, APT38, Diamond Sleet, and TraderTraitor, the group has been active since at least 2009 and is believed to be internally designated as the 414 Liaison Office.
Unlike most state-backed hacker groups that focus on espionage, Lazarus exists for one core purpose: generating revenue for the North Korean regime. Isolated from the global financial system by heavy international sanctions, Pyongyang turned to cybercrime as a lifeline. The stolen funds directly finance North Korea’s nuclear weapons and ballistic missile programs, a connection confirmed repeatedly by the FBI, the U.S. Treasury, and United Nations investigators.
North Korean hackers are trained at military and technical universities before being sent to Shenyang, China, where they learn how the internet operates in the free world. They are then deployed as operatives, working in shifts around the clock, continuously refining their techniques across phishing, malware development, social engineering, and blockchain exploitation.
The Lazarus Group didn’t start with cryptocurrency. Their early operations were about disruption, coercion, and proving capability.
2009-2013: Early Operations. The group launched DDoS attacks against South Korean government systems and infrastructure (Operation Flame, Operation Troy). These were crude by later standards but established North Korea as a player in cyberwarfare.
2014: The Sony Pictures Hack. This was the attack that put Lazarus on the global map. Operating under the alias “Guardians of Peace,” the group breached Sony Pictures Entertainment in retaliation for “The Interview,” a satirical film about assassinating Kim Jong-un. Terabytes of data were stolen, unreleased films were leaked, executive emails were exposed, and Sony’s systems were wiped. Recovery costs ran anywhere from $35 million to over $85 million. The FBI publicly attributed the attack to North Korea, marking the first time a state was accused of hacking a private company for political reasons.
2016: The Bangladesh Bank Heist. Lazarus infiltrated the Bangladesh Central Bank and attempted to steal nearly $1 billion through fraudulent SWIFT transfer requests. A typo in one of the transfer instructions flagged the operation, but they still got away with $81 million. This heist proved something critical: North Korea had the patience, sophistication, and ambition to target the traditional financial system at its highest levels.
2017: WannaCry. The group deployed the WannaCry ransomware worm, which infected over 200,000 computers across 150 countries, crippling the UK’s National Health Service, logistics companies, and government agencies worldwide. While the ransomware collected relatively little revenue, the chaos demonstrated Lazarus could operate at global scale.
By 2017, Lazarus had figured out that cryptocurrency offered something the traditional banking system couldn’t: speed, pseudonymity, and transactions that can’t be reversed once confirmed on-chain. A SWIFT wire can be frozen. A Bitcoin transaction can’t.
The pivot was immediate and aggressive.
2017 saw multiple strikes: $7 million stolen from South Korean exchange Bithumb, another South Korean exchange Youbit driven to bankruptcy after losing 17% of its assets, and 4,500 BTC taken from NiceHash in Slovenia. These were warm-up acts, testing techniques that combined phishing, credential theft, and hot wallet exploitation.
2018-2019 brought continued attacks across Asian exchanges, with the group refining its playbook: compromise employee credentials via spear-phishing, move laterally through internal systems, drain hot wallets, and disappear.
2021 was the year things escalated to a different tier. The Poly Network hack (attributed to Lazarus-style actors) and continued targeting of DeFi protocols showed the group had recognized the new opportunity. DeFi protocols held billions in value, many with untested security models and governance structures that could be exploited. Cross-chain bridges, with their enormous TVL and complex multi-chain logic, became prime targets.
This is where Lazarus went from dangerous to existentially threatening for the crypto industry.
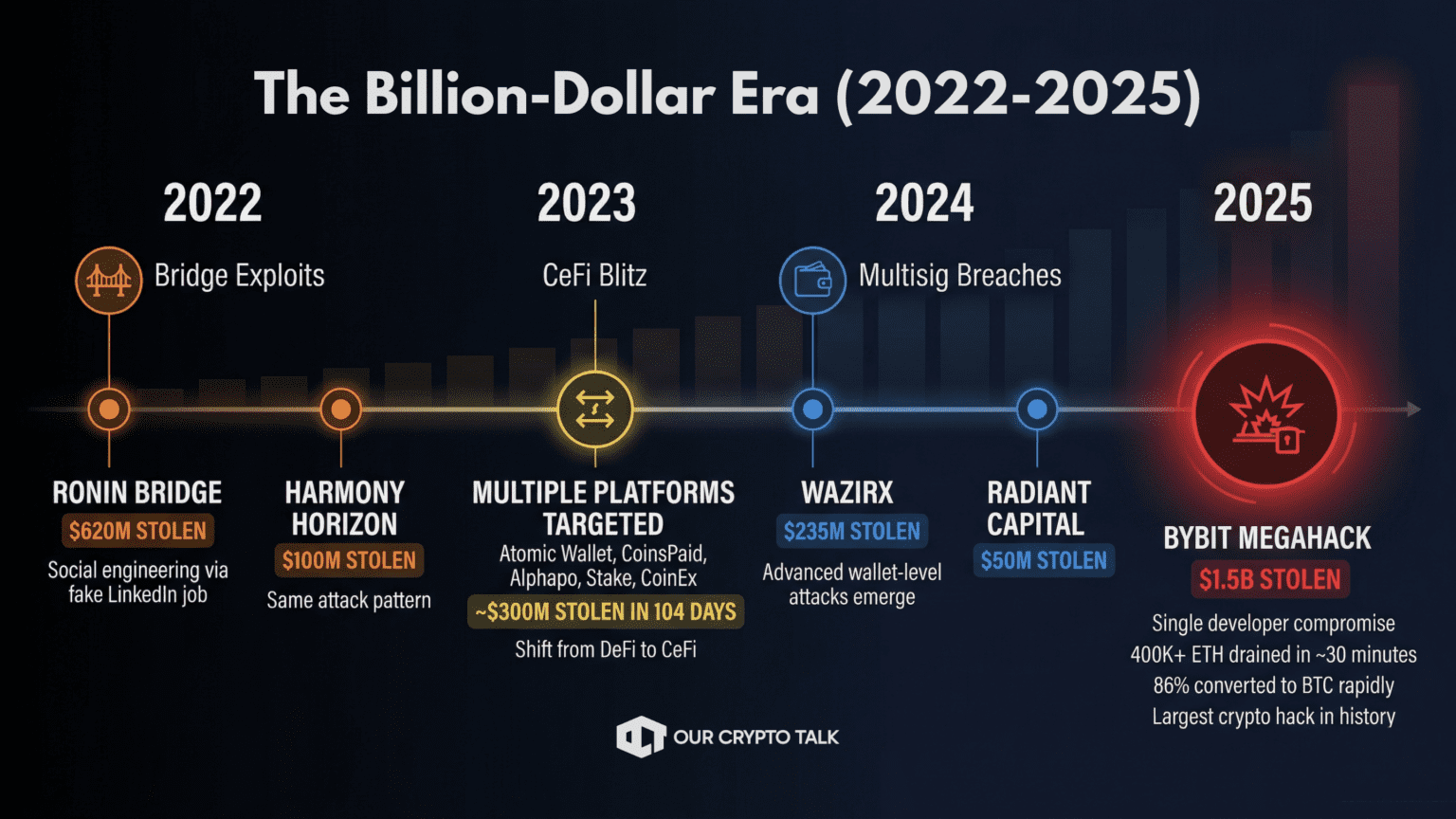
March 2022 – Ronin Bridge ($620 million). The turning point. Lazarus compromised the Ronin Network, the bridge powering Axie Infinity, by targeting a Sky Mavis senior engineer through a fake LinkedIn job offer. Once inside, attackers gained control of enough validator keys to approve a withdrawal of $620 million in ETH and USDC. The FBI confirmed North Korean attribution. This single hack represented a meaningful chunk of North Korea’s annual GDP equivalent. It proved that social engineering, not code exploits, was Lazarus’s real weapon.
June 2022 – Harmony’s Horizon Bridge ($100 million). Same playbook, similar target. The FBI confirmed Lazarus involvement.
Lazarus shifted focus from decentralized protocols to centralized platforms. In a brutal three-month stretch: Atomic Wallet ($100 million), CoinsPaid ($37 million), Alphapo ($60 million), Stake.com ($41 million), and CoinEx ($54 million). The FBI confirmed North Korean attribution for each attack. Nearly $300 million in 104 days.
The Indian exchange WazirX lost $235 million through a multi-signature wallet breach. Radiant Capital was hit for $50 million by UNC4736, the same sub-group later linked to the Drift Protocol attack.
The biggest crypto heist in history. Lazarus compromised a single developer’s laptop at Safe{Wallet}, a third-party wallet provider used by Bybit. They waited weeks, then struck during what appeared to be a routine internal cold wallet transfer. 400,000+ ETH vanished in approximately 30 minutes. The FBI attributed the attack to Lazarus within five days. By March 20, the attackers had already converted 86% of the stolen ETH to Bitcoin through a web of intermediary wallets, DEXs, and cross-chain bridges. The Bybit hack alone was more than North Korea’s entire estimated haul from 2023 and 2024 combined.Same playbook, similar target. The FBI confirmed Lazarus involvement.
2023 – The CeFi Blitz. Lazarus shifted focus from decentralized protocols to centralized platforms. In a brutal three-month stretch: Atomic Wallet ($100 million), CoinsPaid ($37 million), Alphapo ($60 million), Stake.com ($41 million), and CoinEx ($54 million). The FBI confirmed North Korean attribution for each attack. Nearly $300 million in 104 days.

2024 – WazirX ($235 million) and Radiant Capital ($50 million). The Indian exchange WazirX lost $235 million through a multi-signature wallet breach. Radiant Capital was hit for $50 million by UNC4736, the same sub-group later linked to the Drift Protocol attack.
February 2025 – Bybit ($1.5 billion). The biggest crypto heist in history. Lazarus compromised a single developer’s laptop at Safe{Wallet}, a third-party wallet provider used by Bybit. They waited weeks, then struck during what appeared to be a routine internal cold wallet transfer. 400,000+ ETH vanished in approximately 30 minutes. The FBI attributed the attack to Lazarus within five days. By March 20, the attackers had already converted 86% of the stolen ETH to Bitcoin through a web of intermediary wallets, DEXs, and cross-chain bridges. The Bybit hack alone was more than North Korea’s entire estimated haul from 2023 and 2024 combined.
TRM Labs calls this the “industrialization of cryptocurrency theft”: fewer attacks, bigger payoffs, and laundering infrastructure capable of processing hundreds of millions within 48 hours.
North Korea’s obsession with crypto theft isn’t random. It’s a calculated response to a specific geopolitical problem.
Sanctions have cut off traditional revenue. North Korea is one of the most sanctioned nations on Earth. The regime can’t access SWIFT, can’t trade freely on international markets, and can’t borrow from global institutions. Its legitimate exports generate minimal revenue.
Crypto bypasses all of that. On-chain transactions are pseudonymous, fast, and irreversible. There’s no central authority to freeze them in real-time. Cross-chain bridges and mixing services allow rapid obfuscation. And the sheer volume of value flowing through DeFi protocols creates a target-rich environment.
The money funds weapons. The U.S. Treasury, FBI, and UN have all confirmed that stolen crypto directly finances North Korea’s nuclear weapons and ballistic missile programs. A 2023 Wall Street Journal investigation found that digital heists by North Korean hackers funded approximately 50% of the country’s ballistic missile program. This isn’t cybercrime in the traditional sense. It’s state-sponsored financial warfare.
The risk-reward calculus is unbeatable. North Korean operatives face zero risk of prosecution. They operate from a hermit state with no extradition treaties. The potential payoff from a single successful hack can exceed the GDP of some small nations. And unlike traditional bank robbery, the “getaway” happens at the speed of blockchain confirmation.
Lazarus attacks follow a refined methodology that has evolved significantly over the past decade.
Phase 1: Social Engineering. The majority of Lazarus operations begin with human manipulation, not code exploits. The group sends fake job offers via LinkedIn, creates fraudulent recruitment campaigns (codenamed “Contagious Interview” and “DEV#POPPER”), and embeds IT workers inside crypto companies using stolen identities. In 2024 alone, more than a dozen cryptocurrency companies were infiltrated by North Korean operatives posing as remote developers.
Phase 2: Patient Infiltration. Lazarus is willing to spend months, sometimes over six months, building trust and access before striking. They attend conferences in person (using non-Korean intermediaries), establish Telegram groups, deposit real capital, and engage in substantive technical conversations. By the time they attack, they’re not strangers. They’re trusted partners.
Phase 3: Technical Exploitation. Once inside, Lazarus deploys custom malware (MagicRAT, QuiteRAT, AppleJeus), exploits zero-day vulnerabilities, compromises development environments via malicious code repositories or TestFlight applications, and targets the weakest link in the security chain, typically the human one.
Phase 4: Rapid Extraction. When they strike, they move fast. The Drift hack took 12 minutes. The Bybit hack took about 30 minutes. Speed is critical because blockchain analytics firms and exchanges can freeze assets if they detect the theft quickly enough.
Phase 5: Laundering. Stolen funds are immediately split across hundreds of intermediate wallets, bridged across chains (Ethereum to Bitcoin, Bitcoin to stablecoins), run through mixing services like Tornado Cash, and eventually funneled to OTC brokers in China and Southeast Asia who convert crypto to fiat via networks of shell companies and UnionPay cards. The entire cycle from theft to fiat conversion can happen in under 45 days.
On April 1, 2026, Drift Protocol, the largest decentralized perpetual futures exchange on Solana, lost $286 million in approximately 12 minutes. The attack was not an April Fools’ joke.
But the hack didn’t start on April 1. It started six months earlier.
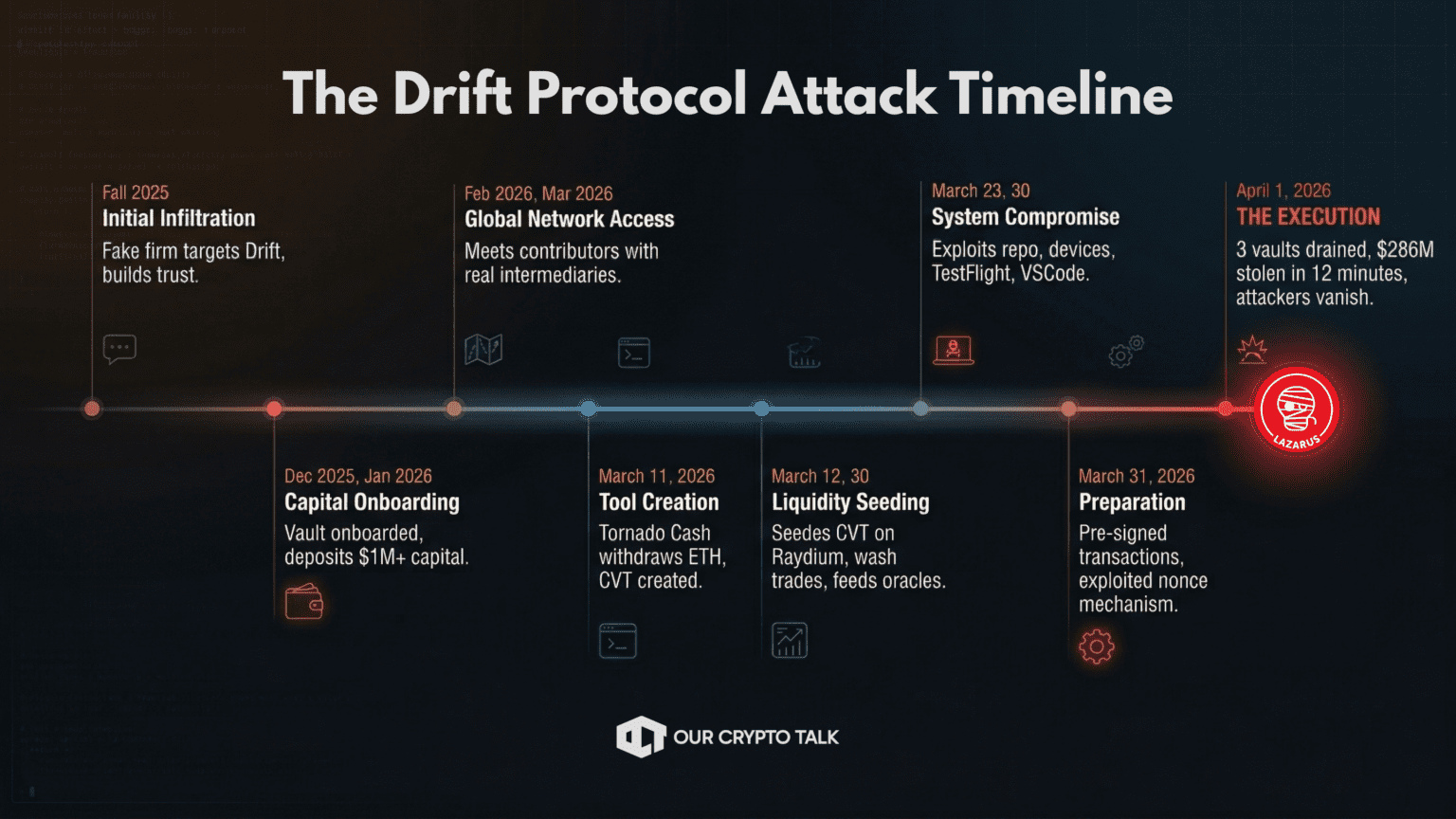
The stolen funds were rapidly swapped to USDC via Jupiter DEX, bridged from Solana to Ethereum through Circle’s CCTP, and dispersed across multiple wallets. Drift’s TVL collapsed from $550 million to under $250 million. The DRIFT token dropped 37-42%, bottoming near $0.04. More than 20 downstream protocols were affected. Circle faced heavy criticism for not freezing the funds despite the attacker holding the USDC for hours before moving it.
Security firm Mandiant and the SEAL911 team attributed the attack with medium-high confidence to UNC4736, a sub-group of the Lazarus ecosystem previously responsible for the Radiant Capital hack, the 3CX supply chain attack, and Chrome zero-day exploitation.
The Drift hack represents an uncomfortable evolution in the threat landscape. This was not a smart contract bug. It was not a flash loan exploit. It was a six-month intelligence operation conducted by a state actor that invested real capital, built real relationships, attended real conferences, and waited patiently until every piece was in position.
The implications are severe:
Multisig is not enough. If attackers are willing to spend six months and a million dollars building trust inside an ecosystem, and can compromise the devices of multisig signers through targeted malware, then multisig governance alone is fundamentally insufficient.
Social engineering is the primary attack vector. The majority of Lazarus’s biggest hacks, Ronin, Bybit, Drift, started with a human being tricked, not a line of code exploited. The industry spends billions on smart contract audits while attackers walk through the front door.
The attackers are getting more patient, not less. The playbook is evolving from weeks of preparation (Bybit) to months of embedded infiltration (Drift). The next attack might involve years of presence inside a protocol’s contributor base.
DeFi needs to treat operational security as seriously as cryptographic security. Device hygiene, contributor vetting, timelocked transactions, hardware-isolated signing environments, and zero-trust architecture are no longer optional. They’re existential requirements.
This is a geopolitical problem, not just a crypto problem. Every successful hack funds weapons that threaten regional and global stability. The intersection of decentralized finance and state-sponsored cybercrime is now a matter of international security.
North Korea’s Lazarus Group has stolen more money from the crypto industry than most countries’ entire annual defense budgets. They’ve evolved from crude DDoS attacks in 2009 to the most sophisticated social engineering and financial theft operation in history. They attend your conferences, join your Telegram groups and they deposit real money in your protocols. And then they drain everything in the time it takes to make a cup of coffee.
The Drift Protocol hack is not an anomaly. It is the new standard. And the uncomfortable question the industry must now confront is not whether Lazarus will strike again, but whether any protocol is truly prepared for adversaries who think in months, invest in millions, and operate with the patience and resources of a nation-state.

