A full breakdown of the Drift Protocol exploit on April 1. How compromised admin keys led to a $270M loss and what it means for Solana DeFi security.
Author: Sahil Thakur
On April 1, 2026, attackers drained between $270 million and $285 million from Drift Protocol, the largest perpetual futures exchange on Solana. As a result, the attack became the biggest native Solana dApp exploit on record and one of the worst DeFi hacks of 2026.
At first, the timing caused confusion. Because the exploit happened on April Fools’ Day, some people in the crypto community dismissed the early warnings as a prank. Even so, the situation quickly became impossible to ignore. Drift Protocol released two separate statements stressing that the incident was real and not an April Fools joke. Meanwhile, vault balances fell from $309 million to less than $41 million in about an hour.
At the same time, several security firms and on-chain analysts verified the exploit through visible fund movements on the blockchain. Researchers from PeckShield, Arkham Intelligence, and Lookonchain all confirmed the transfers independently. In addition, major outlets such as Bloomberg, CoinDesk, and The Block reported on the breach and confirmed that it was legitimate. The attack badly damaged confidence in Solana’s DeFi ecosystem and erased about half of Drift’s total value locked.
Before the exploit, Drift Protocol had built a strong position within Solana DeFi. The platform launched in November 2021 as a decentralized, non-custodial derivatives exchange designed specifically for Solana. Founded in Sydney by Cindy Leow, David Lu, and Chris Heaney, Drift offered perpetual futures with leverage of up to 101x across more than 40 markets. It also expanded into spot trading, lending, borrowing, prediction markets through BET, and automated yield vaults.
Technically, the platform combined several systems to improve speed and efficiency. Its architecture used a Dynamic Automated Market Maker tied to Pyth and Switchboard oracle feeds, a decentralized on-chain order book, and a just-in-time liquidity model that let market makers provide liquidity at the moment of execution.
Drift also attracted major investor backing. Across three venture rounds, the protocol raised $52.5 million. That included a $3.8 million seed round led by Multicoin Capital in 2021, a $23.5 million Series A led by Polychain Capital in 2023, and a $25 million Series B led again by Multicoin in September 2024. Other backers included Blockchain Capital, Maelstrom, and Solana co-founders Anatoly Yakovenko and Raj Gokal.
Later, in May 2024, Drift launched its DRIFT token with a maximum supply of 1 billion. The token eventually reached an all-time high of $2.60, although it later fell sharply.
By late March 2026, Drift had become a key part of Solana’s DeFi infrastructure. Its total value locked had climbed to around $550 million, while cumulative trading volume had passed $133 billion. Moreover, the launch of Drift v3 in December 2025 improved execution speed, bringing order fills below half a second and reducing slippage to 0.02%.
Even earlier security issues had not derailed the platform. In May 2022, Drift faced a V1 exploit caused by a PNL accounting bug that left a $14.5 million shortfall. However, the team covered the loss through emergency financing and later retired V1. The V2 codebase had also undergone audits from Trail of Bits and Neodyme, and the protocol maintained a $1 million bug bounty through Immunefi. Even with those safeguards in place, the April 2026 exploit still broke through.
This account is based on information circulating on social media, since Drift has not yet released an official postmortem.
By most appearances, the exploit was planned well in advance. About eight days before the attack, someone created and funded the wallet HkGz4KmoZ7Zmk7HN6ndJ31UJ1qZ2qgwQxgVqQwovpZES through Near Intents, a cross-chain messaging layer that made the source of funds harder to trace. The attacker then sent a small test transaction of about $2.52 from one of Drift’s vaults, which seems to have confirmed access. After that, the wallet went quiet.
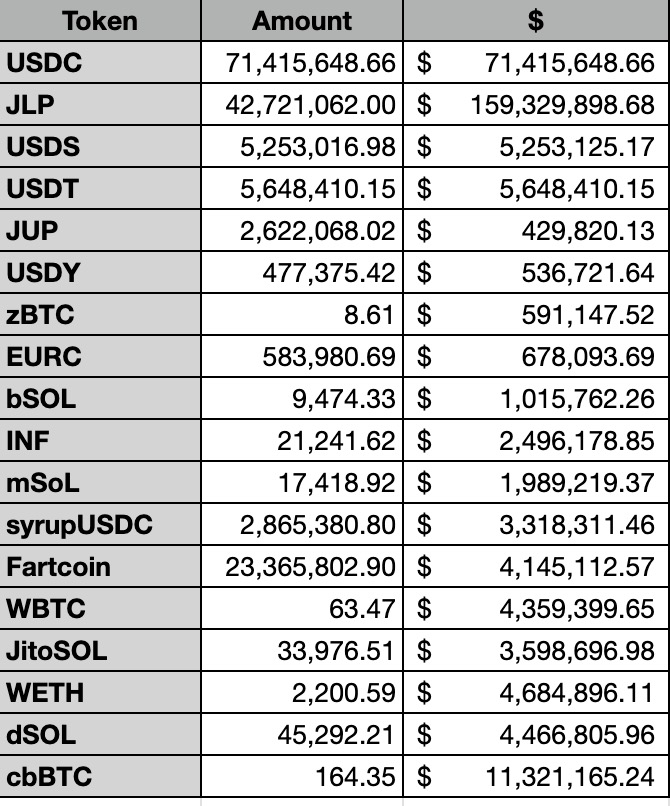
Then, on April 1, 2026, the full drain began at around 4:00 PM UTC, or 1:30 PM Eastern. On-chain monitors such as Lookonchain and PeckShield flagged suspicious outflows almost immediately. From there, the attack moved fast. First, 41.72 million JLP tokens, worth about $155.6 million, left the protocol. Soon after, the attacker drained 51.6 million USDC, 125,000 wrapped SOL worth $10.45 million, 164,349 cbBTC worth $11.29 million, about $5.65 million in USDT, and 23.4 million FARTCOIN worth $4.11 million. They also took smaller amounts of mSOL, BSOL, INF, JitoSOL, dSOL, wETH, and SyrupUSDC. In total, the attacker drained more than 15 token types. Within about an hour, Drift’s vault holdings fell from $309 million to as little as $24 million.
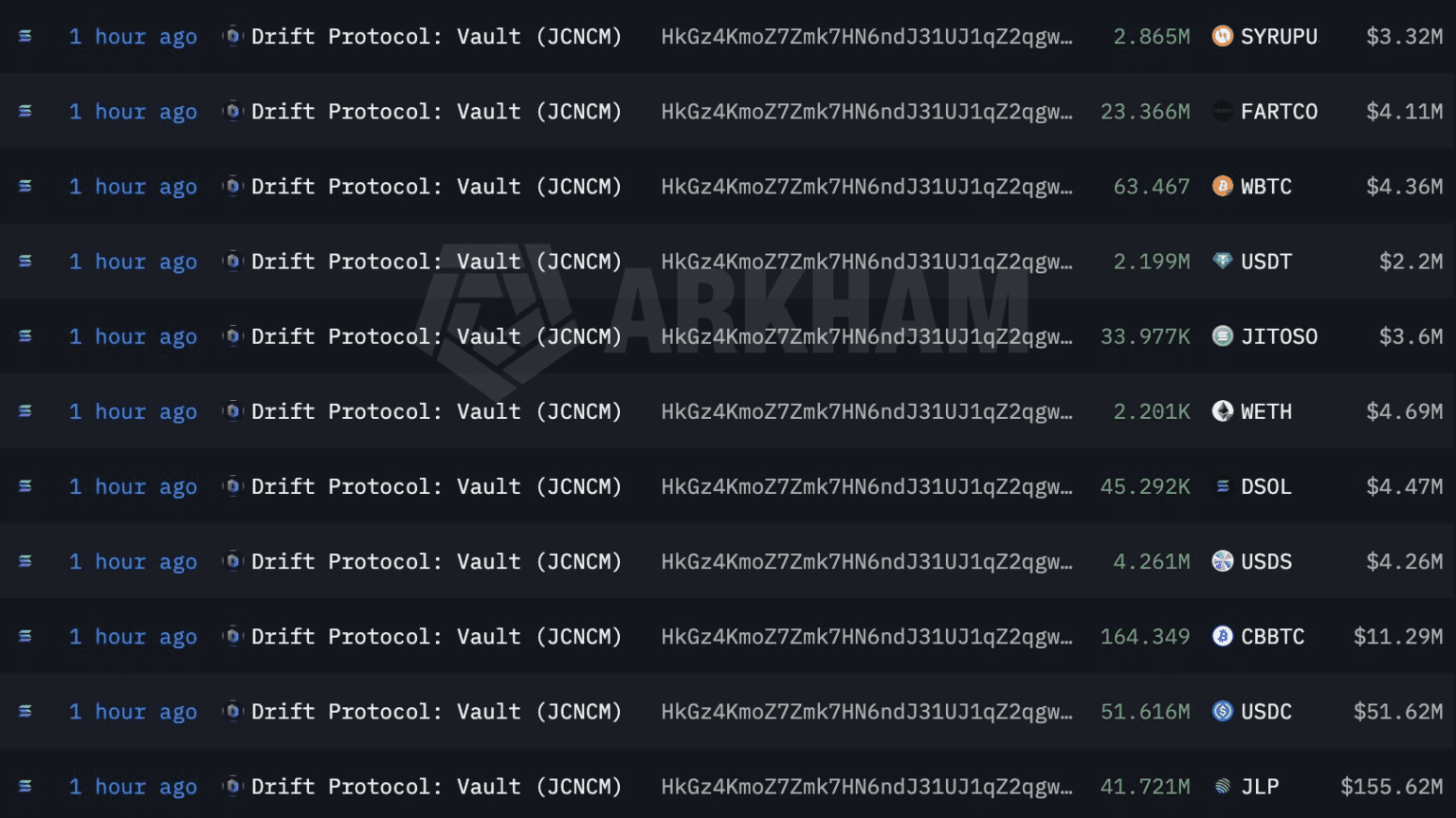
Source: Arkham Intelligence
Just as important, the laundering process showed a high level of sophistication. The attacker swapped stolen assets through Solana-based platforms including Jupiter, Raydium, Orca, and Meteora, then quickly bridged funds to Ethereum. By 6:17 PM UTC, the attacker had bought 38,820 ETH on Ethereum, worth roughly $82.66 million at the time. On top of that, some of the funds moved into Hyperliquid and Binance, while ChainFlip also appears to have played a role in cross-chain transfers. Reports further suggested that the attacker may have used the Phantom wallet app for some swaps. At the same time, some posts claimed the attacker gained admin access, changed admin keys, and locked the Drift team out of critical controls.
So far, the leading theory is that compromised administrator private keys caused the breach, not a flaw in the smart contract itself. PeckShield founder Jiang Xuxian told Decrypt that the admin keys behind Drift were almost certainly leaked or compromised. If that assessment proves correct, the exploit would fall into the same category as the Ronin Bridge and Step Finance incidents. In other words, the failure would stem from operational security, not from a code-level bug.
Source: PeckShieldAlert (X)
Drift Protocol responded in two stages. First, the team posted on X that it had noticed unusual activity on the protocol and was investigating. The message also warned users not to deposit funds and stressed that the situation was not an April Fools joke.
Soon after, the tone became far more urgent. In a second post, published around 2:58 PM Eastern, Drift confirmed that the protocol was under active attack. The team then suspended deposits and withdrawals and said it was working with security firms, bridges, and exchanges to contain the damage. Once again, it had to repeat that the incident was not an April Fools joke.
At the same time, Drift began coordinating with blockchain security and analytics firms, including PeckShield and Chainalysis. The team also contacted Circle in hopes of freezing stolen USDC, while Helius CEO Mert Mumtaz reportedly reached out directly to push for faster action. In parallel, Phantom Wallet warned users who tried to access Drift, and Binance and Coinbase reportedly paused DRIFT trading as a precaution. Even outside the protocol itself, the fallout spread quickly. DeFi Development Corp, a Nasdaq-listed company, issued a formal press release confirming that it had no exposure to Drift.
In the following days, Drift tried to stabilize the situation. On April 3, the team pushed a software patch. Then, on April 5, the co-founders held a live Q&A and admitted that many important details were still unknown. A day later, on April 6, Drift met with DeFi insurance providers to discuss possible compensation. Even so, no clear recovery outcome had emerged by early April 2026.
Meanwhile, social media moved from confusion to panic.
Because the exploit happened on April Fools’ Day, the first warnings did not immediately land with the urgency they deserved. Some people across crypto assumed the reports were part of a prank. That uncertainty spread quickly and made the early response even more chaotic.
One of the most influential warnings came from Helius CEO Mert Mumtaz, who posted that Drift might be getting exploited and urged users to monitor their positions. Since Helius is a major Solana infrastructure provider, his warning helped shift public reaction from skepticism to alarm.
Soon after, other high-profile alerts added to the urgency. Lookonchain posted that Drift appeared to have been exploited and that more than $270 million in assets had been moved to the wallet HkGz4K. At the same time, Arkham Intelligence shared live vault balance tracking that showed the scale of the collapse in real time.
The market reacted immediately. The DRIFT token dropped between 20% and 28%, falling from around $0.072 to as low as $0.045 before recovering slightly to the $0.05 to $0.06 range. Even then, the token was already down about 98% from its November 2024 all-time high. SOL also dipped briefly to $83.82, although it recovered within hours. Meanwhile, DRIFT trading volume surged 198% as panic selling took over.
Across the broader crypto community, the reaction mixed anger with dark humor. A Twitter Spaces session reportedly drew more than 10,000 listeners as people tried to understand what was happening in real time. Before long, the phrase “This is not an April Fools joke” turned into a grim meme. It captured both the seriousness of the attack and the absurd timing. More importantly, the incident exposed a real operational risk. Because the exploit happened on April 1, many people instinctively dismissed the first warnings, and that delay made the crisis harder to contain.
The Drift hack belongs to a long line of DeFi exploits, and the suspected attack vector, compromised private keys, links it to some of the most damaging incidents in crypto history.
On Solana, the closest comparison is the Mango Markets exploit in October 2022. In that case, Avraham Eisenberg manipulated oracle price feeds and drained $110 million from another Solana-based margin trading platform. His method was different, since he relied on oracle manipulation rather than stolen keys. Even so, the end result looked very similar: one attacker systematically emptied a major Solana DeFi protocol. Eisenberg was convicted of wire fraud and commodities manipulation in April 2024, although a federal judge later vacated those convictions on jurisdictional grounds.
Another major comparison is the Wormhole bridge hack from February 2022, which still stands as the largest exploit in the Solana ecosystem at roughly $320 million to $326 million. There, the attacker exploited a smart contract flaw that allowed 120,000 wETH to be minted without collateral. In response, Jump Crypto covered the full loss by depositing replacement ETH. So, while Wormhole and Drift appear in the same broad category of ecosystem-scale failures, the underlying causes seem very different.
More recently, the Cetus Protocol exploit in May 2025 drained $223 million from the largest DEX on Sui. That attack stemmed from an integer overflow bug, not compromised credentials. Still, it offered another example of how quickly a leading DeFi platform can unravel once a core vulnerability gets exposed. In that case, Sui validators took the unusual step of freezing $162 million in attacker-controlled addresses on-chain.
If the private key compromise theory proves correct, then Drift most closely resembles the Ronin Bridge hack from March 2022 and the Bybit hack from February 2025. Ronin lost $625 million after attackers compromised validator keys, while Bybit lost $1.5 billion in a supply chain attack targeting Safe Wallet infrastructure. Authorities and researchers attributed both incidents to North Korea’s Lazarus Group. Together, those cases showed that operational security failures such as social engineering, weak key management, and stale permissions can cause even more damage than smart contract bugs.
By contrast, the Euler Finance hack in March 2023 offers a very different example. That exploit drained $197 million through a flash loan attack, but the attacker returned the full amount within weeks. As a result, Euler remains one of the rare cases in DeFi where a major exploit ended in a complete recovery.
Taken together, these incidents reveal a clear pattern. The technical details may change from one hack to another, but the same core weaknesses keep reappearing. Sometimes the problem is faulty code. Other times it is poor operational security. Either way, the outcome often looks the same: rapid losses, shaken confidence, and a scramble to contain the damage after the fact.
As of early April 2026, the situation is still changing. So far, no one has confirmed any recovery of funds. Meanwhile, the attacker moved quickly across chains and platforms, bridging assets to Ethereum, buying ETH, and depositing funds into centralized exchanges. That pattern closely resembles the laundering strategy seen in the Bybit and Ronin hacks, which suggests recovery will be extremely difficult. On top of that, the use of ChainFlip, Raydium, Orca, Meteora, and possibly mixers such as Tornado Cash makes the trail even harder to follow.
For Drift Protocol, the bigger problem is no longer just technical. The platform may be able to relaunch with patched systems, stronger key management, and tighter controls. Even so, rebuilding more than $270 million in lost user trust is far harder than rebuilding software. The team managed to survive its 2022 V1 incident, which caused a $14.5 million loss, because it fully reimbursed users. This time, however, the scale is entirely different. The current loss is nearly 20 times larger and far exceeds the protocol’s total venture funding of $52.5 million. As a result, it remains unclear whether insurance providers, Solana ecosystem partners, or the Drift Foundation can absorb losses of this size.
More broadly, the exploit underscores some hard truths about Solana DeFi. The ecosystem has now suffered three major nine-figure DeFi exploits: Wormhole at roughly $320 million, Drift at more than $270 million, and Mango Markets at $110 million. Beyond those headline cases, dozens of smaller incidents had already pushed cumulative losses above $530 million across 38 recorded exploits by early 2025. Because so much total value remains concentrated in a handful of protocols, a single key compromise can erase an outsized share of the ecosystem’s value.
For that reason, this attack will likely push Solana DeFi toward stricter security practices. We will probably see faster adoption of multisig governance, hardware security modules, time-locked admin controls, and more decentralized key management. In practice, measures like these might not stop every attack, but they can at least slow an attacker down and create more time to respond.
The Drift Protocol exploit is a harsh reminder that operational security failures can undo even well-audited and well-funded protocols. Early evidence suggests the loss of $270 million to $285 million did not come from an unusually clever code exploit or some novel technical breakthrough. Instead, it appears to trace back to one of the oldest and most preventable failures in crypto: compromised private keys.
The April Fools’ Day timing made the situation even worse. Because the first warnings sounded almost unbelievable on that date, some people dismissed them as jokes. That skepticism seems to have slowed the community’s response at exactly the moment when speed mattered most.
As a result, the hack now stands as the second-largest exploit in Solana ecosystem history after Wormhole, and one of the ten largest DeFi exploits ever recorded. With the stolen funds still moving across chains and no clear recovery in sight, the next chapter for Drift and for Solana DeFi will depend on something larger than one protocol. The real test is whether the ecosystem can finally turn another expensive lesson into lasting security changes that address human weaknesses, not just technical ones
According to the X thread by Drift Protocol, that they posted a few hours after the exploit:
On April 1, 2026, Drift Protocol suffered a highly sophisticated exploit in which a malicious actor gained unauthorized administrative control of the Security Council through a novel attack involving durable nonces on Solana. The attacker secured 2/5 multisig approvals, likely via social engineering or misrepresented transaction approvals and rapidly executed a malicious admin transfer. This allowed them to introduce a rogue asset and remove all pre-set withdrawal limits, resulting in approximately $280 million drained from user deposits in the protocol. Importantly, the incident was not caused by any bug in Drift’s smart contracts or programs, nor by compromised seed phrases.The attack showed clear signs of multi-week preparation.
On March 23, four durable nonce accounts were created – two linked to legitimate Security Council multisig members and two to attacker-controlled wallets.
After a planned multisig migration on March 27 and additional nonce activity on March 30, the attacker struck on April 1, executing two pre-signed durable nonce transactions shortly after Drift completed a legitimate test withdrawal from the insurance fund.All deposits in Drift’s borrow/lend markets, vaults, and trading funds were affected. Assets such as DSOL that were never deposited into the protocol (including those staked to the Drift Validator) and the Insurance Fund remain unaffected, with the latter being withdrawn for safeguarding. In response, Drift has frozen remaining protocol functions, updated the multisig to remove the compromised wallet, and is working with security firms, bridges, exchanges, and law enforcement to trace and freeze the stolen assets. A detailed technical postmortem is expected in the coming days.
Drift says the April 1, 2026 attack was not a quick hit. It now looks like a long, deliberate setup that may have started in Fall 2025. According to the team, the attackers posed as a legitimate trading firm and spent months building trust with Drift contributors. They met people in person at major crypto events, stayed in touch on Telegram, and held detailed conversations about trading strategies and vault integrations. Over time, they looked like a normal counterparty, not a threat.
Drift says that trust-building went even further in late 2025 and early 2026. The group onboarded an Ecosystem Vault, joined working sessions, asked credible product questions, and deposited more than $1 million of their own capital. By the time the exploit happened on April 1, they were familiar to multiple contributors and had been around the ecosystem for nearly six months. That is why Drift now describes the breach as a structured infiltration, not a random exploit.
The team is still investigating the exact attack path, but it believes the compromise may have come through tools and files shared by the group. One possible vector was a code repository sent under the guise of frontend deployment. Another was a TestFlight app presented as a wallet product. Drift is also looking at a possible link to a known VSCode and Cursor vulnerability that could let malicious code run when a file or repository is opened. In response, Drift has frozen remaining protocol functions, removed compromised wallets from the multisig, and flagged attacker wallets with exchanges and bridge operators. Mandiant is now involved in the forensic investigation.

