
The KelpDAO LayerZero exploit drained $290M via a forged cross-chain message and a 1-of-1 DVN setup. Here's how the DeFi hack unfolded.
Author: Tanishq Bodh
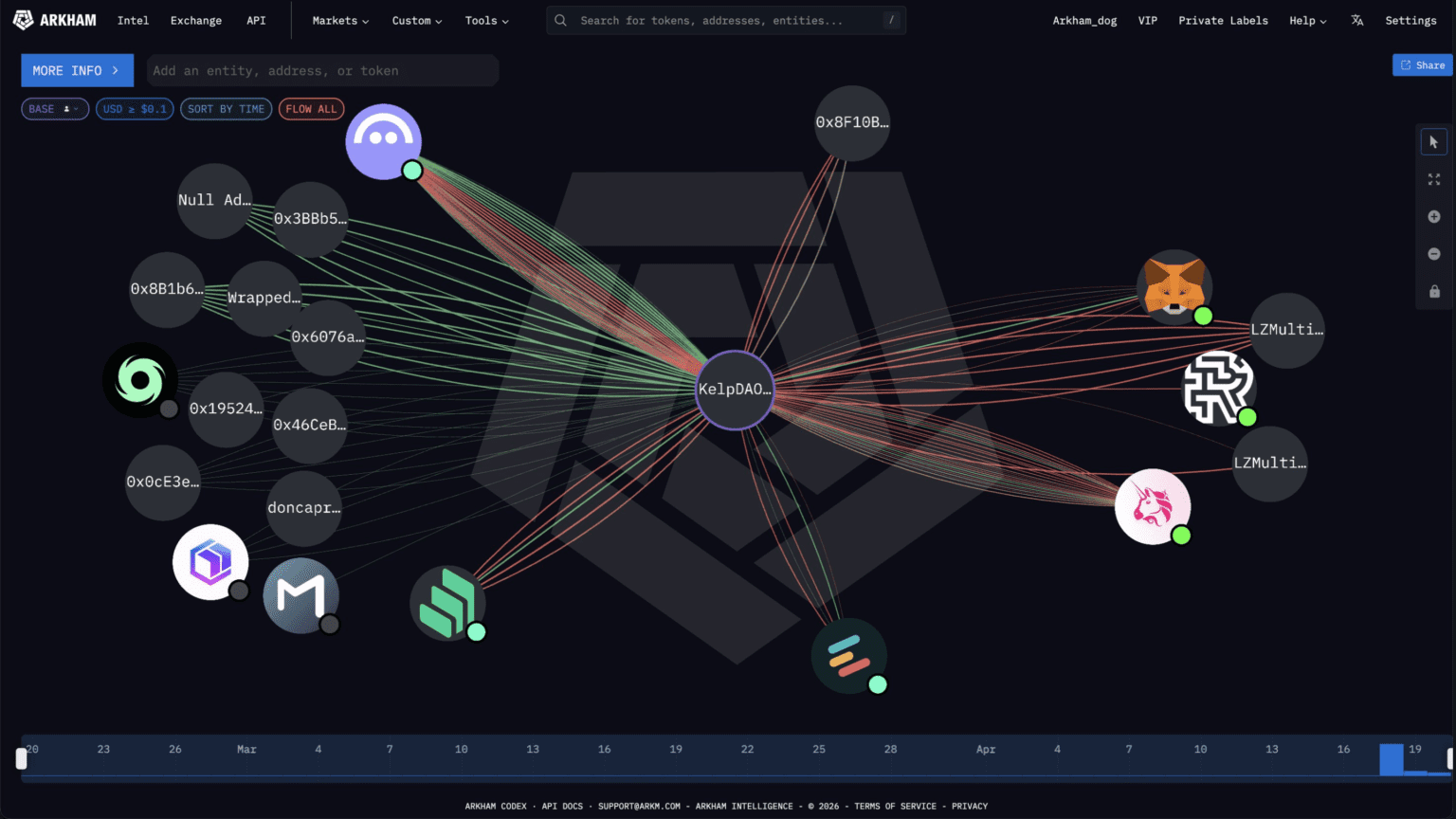
On April 18, 2026, an attacker sent one crafted message to a bridge contract and walked away with 116,500 rsETH. No ETH was locked anywhere. No deposit ever happened. The bridge just released the tokens like the paperwork was in order. Forty-six minutes later, KelpDAO’s emergency multisig hit pause. By then, the stolen rsETH had already been recycled into Aave, posted as collateral, and used to borrow real wrapped ether out the door. By Sunday morning, DeFi had lost $13.21 billion in total value locked. Aave had dropped from $26.4 billion to $18.6 billion in a single weekend. The KelpDAO LayerZero exploit is now the largest DeFi hack of 2026, and LayerZero says North Korea’s Lazarus Group is behind it.
Here is what actually happened, who is blaming whom, and why this one was different.
KelpDAO is a liquid restaking protocol built on top of EigenLayer. Users deposit ETH (or liquid staking tokens like stETH and cbETH), Kelp routes that capital through EigenLayer to earn restaking yield, and the user receives rsETH as a tradeable receipt token.
rsETH is designed to represent a 1:1 claim on underlying restaked ETH. Because of that peg assumption, lending protocols like Aave, SparkLend, Fluid, Compound and Euler accepted rsETH as ETH-correlated collateral. It behaved like ETH, was priced like ETH and got treated like ETH.
rsETH lives on more than 20 chains. Ethereum mainnet, Arbitrum, Base, Linea, Blast, Mantle, Scroll, Optimism, Mode, and others. Moving rsETH between these chains is handled by LayerZero’s OFT (Omnichain Fungible Token) standard. The Ethereum mainnet contract holds the reserve that backs every wrapped rsETH on every L2.
That reserve is what got drained in the KelpDAO LayerZero exploit.
The attack unfolded over roughly an hour on a Saturday evening in UTC.
How the KelpDAO LayerZero exploit unfolded
Funding routed through Tornado Cash roughly 10 hours before the attack. Pre-planned, not opportunistic.
116,500 rsETH released from the Ethereum OFT adapter. Adapter balance drops from 116,723 to 223 rsETH in one block. No ETH locked anywhere.
Fanned across 7 branch wallets. 89,567 rsETH posted as collateral on Aave V3/V4 across Ethereum and Arbitrum. ~82,650 WETH and 821 wstETH borrowed.
Emergency multisig freezes core contracts. 46 minutes after the drain.
Attacker tries two more 40,000 rsETH drains worth roughly $100 million. Both revert into the pause.
Protocol Guardian freezes rsETH and wrsETH across all V3 deployments. LTV set to zero across 11 markets.
Here is the part that makes the KelpDAO LayerZero exploit different from the usual DeFi exploit.
There was no reentrancy. No price oracle manipulation or unchecked function and no governance attack. LayerZero’s smart contracts worked exactly as designed. KelpDAO’s core restaking contracts were never touched.
The attackers went one layer below the smart contracts. They went after the infrastructure that LayerZero’s verifier uses to read the blockchain.
1. Target the RPC layer. LayerZero uses something called a Decentralized Verifier Network (DVN) to check whether a cross-chain message corresponds to a real event on the source chain. The DVN reads the source chain through RPC nodes (servers that let software query blockchain data). LayerZero’s verifier was configured to query a mix of internal and external RPC nodes for redundancy.
2. Compromise two nodes. Attackers gained access to two separate RPC nodes running op-geth, on independent clusters. They swapped the binaries running on those nodes with malicious versions. Here is the clever part: those poisoned binaries lied selectively. They reported fraudulent transaction data only when queried by LayerZero’s DVN, and returned accurate data to everyone else. Even LayerZero’s monitoring infrastructure queried those same RPCs from different IP addresses and saw nothing wrong.
3. DDoS the rest. Compromising two nodes was not enough. LayerZero’s verifier would still have fallen back to uncompromised RPCs. So the attackers launched a distributed denial-of-service attack on the legitimate RPCs, overwhelming them with junk traffic. The verifier failed over to the only nodes still responding: the poisoned ones.
4. Send the forged message. With the DVN now reading corrupt data, the attacker submitted a cross-chain packet claiming an rsETH burn had happened on another chain. The DVN verified it. LayerZero’s EndpointV2 contract delivered it. Kelp’s OFT adapter on Ethereum released 116,500 rsETH to the attacker. No token was ever burned anywhere. The reserve just moved.
5. Cover the tracks. After the attack, the malicious binaries self-destructed. Logs were deleted. The poisoned nodes went dark.
This is not a bug. The KelpDAO LayerZero exploit was a supply-chain style infrastructure attack executed with what LayerZero calls “highly sophisticated state-sponsored” tradecraft.
Here is why the attack actually worked: KelpDAO’s bridge was configured with a single DVN. One verifier. LayerZero Labs. That means LayerZero Labs alone was responsible for checking the authenticity of every cross-chain message moving rsETH.
Under a properly hardened multi-DVN configuration, a cross-chain message would need consensus from several independent verifiers. Poisoning the data feed of one verifier would not be enough. The forged message would fail at the consensus check.
This is where the blame game around the KelpDAO LayerZero exploit starts.
First, LayerZero’s integration checklist explicitly recommends multi-DVN redundancy. In addition, direct communications with KelpDAO had raised the point. However, KelpDAO chose 1/1 anyway. As a result, LayerZero co-founder Bryan Pellegrino stated the protocol functioned as designed. Moreover, there has been zero contagion to any other application using multi-DVN. Consequently, LayerZero says it will not sign messages for any app still running 1-of-1. Furthermore, the protocol is forcing a broad migration.
On the other hand, KelpDAO argues the 1/1 setup is LayerZero’s own default. For example, the V2 OApp Quickstart guide ships this configuration. Similarly, the sample layerzero.config.ts file wires every pathway with one required DVN and zero optional DVNs. In addition, standard GitHub deployment templates follow the same pattern. According to sources close to Kelp, roughly 40% of protocols currently running on LayerZero use the same 1/1 configuration. Besides this, the communication channel with LayerZero has been open since July 2024. Nevertheless, there was no specific recommendation to change the rsETH DVN config, even during L2 expansions.
To sum up, neither side is technically wrong. On the one hand, the protocol allows 1/1. On the other hand, the docs warn against it in some places and ship it as default in others. In conclusion, that ambiguity is now the most important design question in cross-chain messaging.
The attacker did not try to sell the stolen rsETH. That would have crashed the price and tipped everyone off.
Instead, they did something far more destructive. They deposited 89,567 of the 116,500 stolen rsETH into Aave V3 and V4 markets on Ethereum and Arbitrum, posted it as collateral, and borrowed real wrapped ether against it. The borrow positions were tuned with health factors between 1.01 and 1.03 to extract the maximum possible ETH.
Total real assets borrowed: approximately 82,650 WETH and 821 wstETH. Around $190 million in real, withdrawable liquidity walked out of Aave.
When the market realized the collateral was unbacked, those positions became unliquidatable. Liquidators have no incentive to close them because the collateral is worthless in isolation. That leaves the bad debt sitting on Aave’s books.
Aave’s bad debt range depends on how KelpDAO allocates the loss.
Scenario 1 (loss socialized uniformly across all rsETH holders): 15.12% depeg, $123.7M in bad debt for Aave, mostly on Ethereum Core.
Scenario 2 (loss isolated to L2 rsETH only): 73.54% haircut on L2 collateral, $230.1M in bad debt, concentrated on Mantle and Arbitrum.
Aave’s Umbrella insurance fund, its automated bad-debt backstop launched in June 2025, holds around $50 million. Aave’s DAO treasury holds roughly $181 million as of April 20. The gap is where the next few weeks of Aave governance will happen.
Then came the secondary damage. When WETH suppliers realized Aave might socialize losses, they rushed to withdraw. By Sunday morning, $5.4 billion of ETH and WETH had left Aave. The WETH pool hit 100% utilization, freezing remaining suppliers. USDT and USDC pools also hit 100% utilization, stranding roughly $5.1 billion in stablecoins. Aave’s TVL fell from $26.4 billion to $18.6 billion, losing its spot as the largest DeFi protocol.
Total DeFi TVL dropped from $99.5 billion to $86.3 billion. A $13.21 billion hit across 48 hours, all triggered by the KelpDAO LayerZero exploit.
Two days after the KelpDAO LayerZero exploit, the Arbitrum Security Council did something rare on a major L2. Specifically, it executed an emergency multisig action to freeze attacker funds.
On April 20 at 23:26 ET, the council moved 30,766 ETH, worth roughly $71 million, out of an address tied to the exploiter and into an intermediary frozen wallet. In addition, the council stated it identified a “technical approach” to relocate the ETH without altering chain state or impacting any other user or application on Arbitrum One. Furthermore, the move was coordinated with law enforcement input, and no details about the exploiter’s identity have been publicly disclosed.
However, the frozen ETH is not recovered yet. In fact, it sits in an intermediary wallet and can only be moved through a formal Arbitrum governance vote. Going forward, coordination between KelpDAO, LayerZero, affected protocols, and law enforcement will decide how restitution is structured from here.
At roughly $71 million frozen out of ~$290 million stolen, this action recovers about 24% of the total loss. Meanwhile, the rest, including an estimated 75,700 ETH (~$178 million) sitting on Ethereum mainnet, remains out of reach.
On the other hand, the community response has been split. For example, many praised the speed and coordination, calling it proof that DeFi security infrastructure can respond to a crisis in real time. However, others flagged the precedent: a multisig with emergency powers freezing user funds on a Layer 2 challenges the decentralization story Arbitrum tells about itself. In other words, the same capability used for clear-cut cases like a $290M theft can, in theory, be applied in less clear-cut ones.
To sum up, that debate will not resolve quickly. Nevertheless, the mechanism is now on the record.
While Arbitrum-side funds were frozen through governance intervention, the Ethereum-side position is a different problem entirely.
The attacker’s Ethereum hub wallet holds roughly 75,700 ETH (~$178 million). But those balances are not liquid. They sit as collateral backing the WETH borrowed from Aave using unbacked rsETH. The attacker’s net equity in those positions is effectively zero.
The assets are frozen by the attacker’s own trade. Moving the ETH out requires repaying the debt. Repaying the debt requires the bad-debt rsETH collateral to be worth something. And the longer those positions stay open, the more interest accrues against them.
This is why Tron founder Justin Sun went on X to publicly plead with the hacker to negotiate a return, writing that the loss of this magnitude is “not worth it to sacrifice both Aave and KelpDAO.” White-hat bounty offers and law enforcement coordination are ongoing. LayerZero is working with Seal911, Aave’s team, and multiple agencies to trace funds.
No mainnet recovery has been publicly confirmed yet.
LayerZero’s post-mortem attributes the KelpDAO LayerZero exploit with “preliminary confidence” to North Korea’s Lazarus Group, specifically its TraderTraitor subunit. The indicators point to the same playbook: Tornado Cash funding, binary swaps on infrastructure, self-destructing payloads, selective deception to avoid monitoring tripwires.
This is the second major Lazarus-linked DeFi exploit in 18 days. On April 1, Drift Protocol was drained of $285 million through a different vector, social engineering of governance signers with pre-signed hidden authorizations. Different method. Same actor. Same window.
Combined Lazarus DeFi haul for April 2026: over $575 million.
The shift is important. Lazarus historically preferred exchange hacks and bridge smart contract exploits. What happened at Drift and in the KelpDAO LayerZero exploit represents a tactical evolution: targeting governance processes at one protocol, and infrastructure supply chains at another. Both outside the smart contract layer. Both hitting the trust boundaries that DeFi protocols depend on without always hardening.
Three things are live and moving:
Loss allocation at KelpDAO. The team has not yet announced how the 112,204 unbacked rsETH will be absorbed. The choice, socialize across all holders or isolate to L2s, decides the bad debt outcome for Aave, Compound, Mantle, Arbitrum, and every other network holding wrapped rsETH.
LayerZero’s forced migration. LayerZero says it will stop signing messages for any app still running a 1/1 DVN setup. If ~40% of LayerZero-integrated protocols really are on 1/1, that is a broad reshuffle of the entire OApp ecosystem over the coming weeks.
Aave’s governance waterfall. If bad debt lands around $196M and Umbrella covers $50M, the rest goes through a predefined sequence: aWETH Umbrella stakers slashed first, WETH suppliers take a pro-rata haircut next, stkAAVE holders absorb more if governance activates a deeper slash, and the DAO treasury could fund a repayment proposal last.
For users: “ETH-like” is not “risk-equivalent to ETH.” A liquid restaking token can trade at peg for months and still carry bridge, minting, and validator risk that price action will never expose until it breaks.
For protocols: Default configurations are not safe configurations. If your bridge relies on a single verifier, that verifier is your entire security model. The question “what happens if this one thing goes wrong” has to be asked before it goes wrong.
For the L2 ecosystem: Cross-chain tokens built on the assumption of a permanent reserve backing are only as safe as the slowest, weakest, most misconfigured bridge endpoint in the network.
For everyone: Lazarus Group now has a playbook for hitting DeFi through infrastructure instead of code. The weakest link in a cross-chain system is rarely the smart contract. It is the machine telling the smart contract what is true.
The KelpDAO LayerZero exploit cost Kelp its reserve. It cost Aave its top spot. It cost DeFi $13 billion in a weekend.
One RPC endpoint. One DDoS. One verifier. That is all it took.
Quick answers on the KelpDAO LayerZero exploit
An infrastructure attack, not a smart contract bug. Attackers poisoned two RPC nodes and DDoS’d the rest, tricking LayerZero’s single verifier into approving a forged cross-chain message.
~$290M stolen. ~$71M (24%) frozen by the Arbitrum Security Council. Roughly $178M still sits on Ethereum mainnet, locked as attacker collateral on Aave.
LayerZero attributes it with preliminary confidence to North Korea’s Lazarus Group, TraderTraitor subunit. Same group linked to the $285M Drift Protocol hack 17 days earlier.
No. Aave’s contracts worked fine. The attacker used stolen rsETH as collateral to borrow ~$190M in real ETH, leaving Aave with $123M-$230M in bad debt.
Mainnet rsETH is still backed. L2 rsETH (Arbitrum, Base, Mantle, Linea, etc.) is uncertain until KelpDAO announces how losses will be allocated.


First public acknowledgement on X, 2 hours 35 minutes after the drain.
Aave freezes WETH on Core, Prime, Arbitrum, Base, Mantle, Linea. SparkLend, Fluid, Compound, Morpho follow. $13.21 billion wiped from DeFi TVL.
Attributes attack to Lazarus Group’s TraderTraitor subunit. Blames KelpDAO’s 1/1 DVN setup. KelpDAO disputes the framing hours later.
Emergency multisig action moves 30,766 ETH tied to the exploiter into a frozen intermediary wallet. Roughly 24% of stolen funds recovered.
Inside Re: The Insurance RWA Project With $465M in TVL
Best Web3 Privacy Wallets 2026: Guide to Storing Crypto Privately
How to Actually Lock In on CT (While 90% Stay Broke)
Crypto Privacy in 2026: Tech, Tools & Regulation Guide
Inside Re: The Insurance RWA Project With $465M in TVL
Best Web3 Privacy Wallets 2026: Guide to Storing Crypto Privately
How to Actually Lock In on CT (While 90% Stay Broke)
Crypto Privacy in 2026: Tech, Tools & Regulation Guide