
Arbitrum's freezing of nearly $70M worth of ETH has raised a question - how do blockchains actually freeze tokens? In this article, we explain.
Author: Sahil Thakur
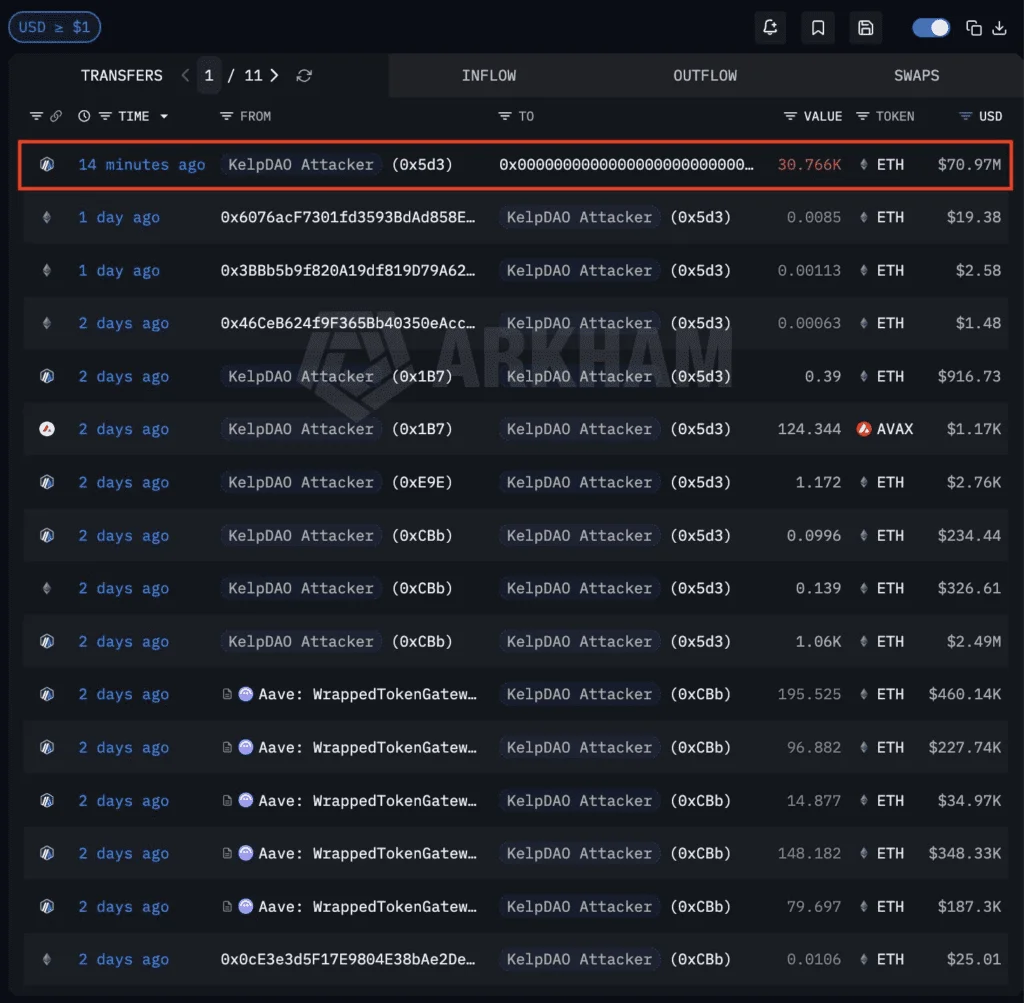
On 21 April 2026 at 11:26 PM ET, Arbitrum’s Security Council moved 30,765.667501709008927568 ETH out of an address linked to the KelpDAO exploiter and into 0x0000000000000000000000000000000000000DA0. Per Arbitrum’s official forum post, the funds stay at that address until governance votes to release them. At prices on the day, the amount is worth roughly $71 million.
The mechanism is what makes this case worth studying. The Council didn’t break any cryptography. It used a path Arbitrum’s governance docs have described all along: temporarily upgrade the Delayed Inbox contract on Ethereum L1, inject a cross-chain message forged to look like it came from the exploiter, move the ETH on L2, and restore the original Inbox. All of that happened inside a single atomic transaction. That’s how blockchains freeze tokens in 2026. Not by cracking keys, but by using privileged control surfaces that already exist in code and governance.
This piece walks through how the Arbitrum action actually worked, what “freezing a token” means across three different operations, the primitives that make freezes possible at the contract, proxy, bridge, and rollup layers, and how the major L1s and L2s rank on the “can this chain touch my assets” question.
Start from the top. On 18 April 2026, KelpDAO’s rsETH setup was exploited for approximately $290 million, per LayerZero’s official incident statement. LayerZero characterised the issue as isolated to KelpDAO’s rsETH configuration. KelpDAO’s own public statement said the team had identified suspicious cross-chain activity and paused rsETH contracts across mainnet and several L2s.
Aave followed within hours. In a public statement, the protocol froze its rsETH markets on V3 and V4 to block new deposits and borrows against compromised collateral. Aave did not publish the exact amount of collateral affected.
Three days later, Arbitrum acted. The official forum post documents the facts cleanly: at 11:26 PM ET on 21 April 2026, the Security Council executed an emergency action that froze 30,765.667501709008927568 ETH held by the address associated with the KelpDAO exploiter on Arbitrum One. The funds were routed to 0x000…0DA0. Any later release requires a subsequent Arbitrum governance action.
Arbitrum’s official X account added one piece of process context the forum post did not. The action was taken “pursuant to information provided by law enforcement about the identity and actions of the exploiter.” Law enforcement was an information source. The decision itself ran through Arbitrum governance.
The on-chain receipts back this up. The L1 transaction that executed the emergency path is 0x079984c5…f645f770. It originated from Arbitrum’s L1 emergency Security Council at 0xF06E95eF…14023F85 and called through to the L1 Upgrade Executor at 0x3ffFbAdA…b2c3CeDd. The Delayed Inbox that was modified sits at 0x4Dbd4fc5…0A60BAB3f. On the L2 side, Arbiscan shows the full 30,765.667501709008927568 ETH landing in 0x000…0DA0. The forum post also links the L2 transaction, but the retrieved parser only surfaced the prefix 0x5618044241…, so the full L2 hash isn’t stated here.
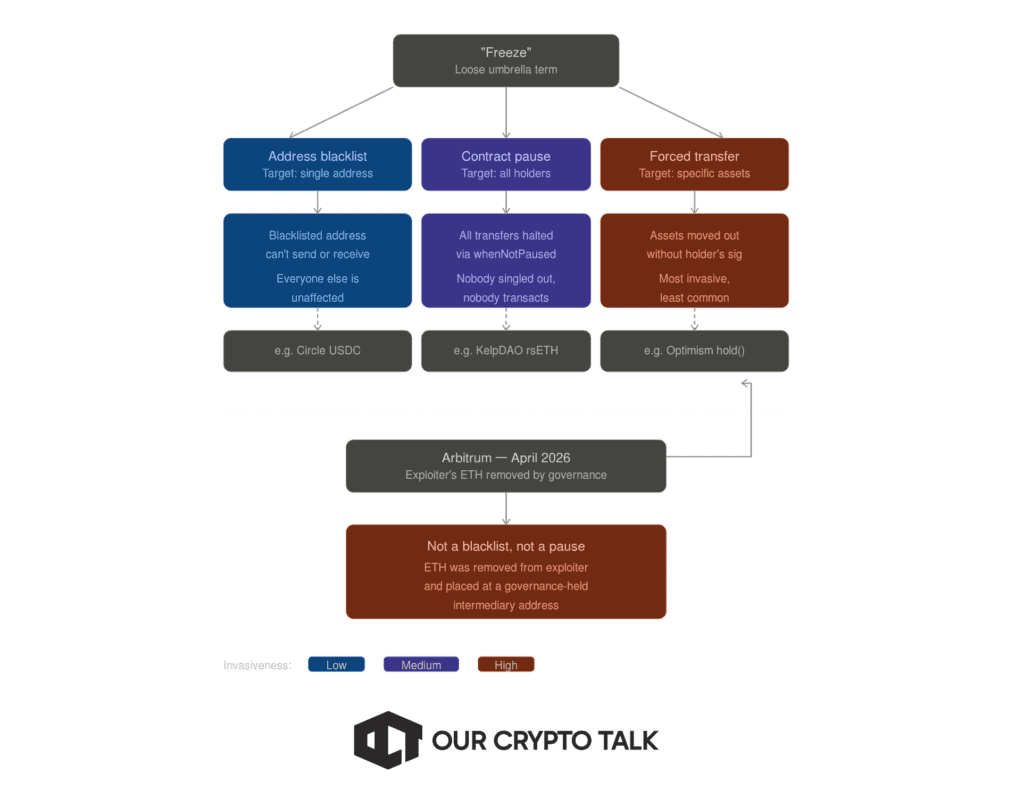
People use “freeze” to mean at least three different operations. The distinction matters because Arbitrum’s April 2026 action is only one of them, and the ethical weight shifts in each case.
The first is an address-level freeze. The token contract has a blacklist, and a privileged role can add an address to it. Once listed, that address can’t send or receive the token. Everyone else keeps transacting normally. Circle’s USDC is the textbook example of a smart contract blacklist operating at the address level.
The second is a contract-wide pause. A privileged role flips a switch, and transfers halt for everyone holding that token or using that market. Nobody is singled out. OpenZeppelin’s Pausable module is the standard way this is built, using a `whenNotPaused` modifier on sensitive functions. KelpDAO did exactly this when it paused rsETH contracts across mainnet and several L2s on 18 April 2026.
The third is a forced transfer. A privileged function can move assets out of an account without the holder’s signature. This is the most invasive of the three and the least common. Optimism’s governance has proposed a `DelayedWETH.hold(…)` primitive along these lines as an incident-response hardening, and Arbitrum’s April 2026 action is the cleanest executed example.
Arbitrum’s case sits squarely in the third bucket. The exploiter’s ETH wasn’t marked non-transferable inside the exploiter’s address. It was removed from the exploiter’s address entirely and placed at an intermediary held by chain governance. That’s a forced transfer executed through a privileged system path. If you take one thing from this section, it’s that “freeze” is a loose word. Blacklist, pause, and forced transfer are three different operations, and naming which one a protocol used is the start of the real conversation.
The base Ethereum token standards don’t force any of this. ERC-20 defines balances, transfers, approvals, and events for fungible tokens. ERC-721 does the same for NFTs. ERC-1155 generalises multiple token types inside one contract. None of those standards, on their own, require a blacklist, a pause switch, or a forced transfer. Those powers appear only when developers choose to add them.
They get added a lot.
OpenZeppelin’s access control documentation says contract permissions may govern, among other things, “who can mint tokens, vote on proposals, freeze transfers.” The Pausable module provides `whenNotPaused` and `whenPaused` modifiers for emergency stops. ERC-721 ships with a standard ERC721Pausable extension in the same library. And OpenZeppelin’s upgradeability docs describe both Transparent and UUPS proxy patterns that let an admin swap a contract’s logic after deployment. That’s the upgradeable proxy admin risk everyone warns about, made concrete.
Put those pieces together and you get the modern token contract. Transfers guarded by access control. Pauseable in emergencies. Upgradeable by a designated admin. Roles assigned to specific addresses or multisigs. Circle’s publicly documented stablecoin contracts are a working example. The repo defines roles for pauser, blacklister, owner, masterMinter, and proxyOwner. The code wraps minting, approvals, transfers, and transferFrom in `whenNotPaused` and `notBlacklisted` guards. Newer versions store blacklist state in balance-related storage while preventing balance updates for listed accounts. In other words, many “frozen tokens” are frozen because the token contract was designed that way from day one.
At the rollup layer, the control surface shifts. The token contract may be immutable, but the bridge, the governance, and the underlying chain aren’t. Arbitrum’s governance architecture specifies that only the Security Council and the L1 timelock can call the L1 Upgrade Executor, which in turn owns the L1 contracts for Arbitrum One and Nova. The same docs describe a chain owner that can upgrade core smart contracts, set parameters, and pause the system. The Council can act quickly through a 9-of-12 multisig in an emergency, or more slowly through a 7-of-12 path that still bypasses a DAO vote for routine upgrades. That’s the machinery that made the April 2026 Delayed Inbox intervention possible without rewriting history.
The pattern repeats elsewhere. L2BEAT‘s current OP Mainnet page says all contracts are upgradable by the SuperchainProxyAdmin, effectively controlled by a 2/2 combination of the Security Council and the Optimism Foundation, with no delay on regular upgrades. The Base page says upgrades must be approved by the Base Coordinator Multisig and the Base Security Council, again with no delay. These aren’t bugs. They’re explicit security-governance choices about how much emergency discretion the system keeps. And they’re what “can blockchain tokens be frozen” really comes down to.
Bridges add one more layer. A so-called bridged token is typically a claim on assets escrowed elsewhere. If the bridge contract is upgradeable, the bridge admin can pause deposits, redirect withdrawal logic, or change settlement rules. That was one of the underlying dynamics in the KelpDAO incident. The exploit was tied to cross-chain message configuration, and the Arbitrum freeze itself operated through the L1 Delayed Inbox, the chain’s primary bridge entry point. If you hold a bridged asset, you hold a contract’s promise to honour a claim. Ask who can change the contract.
This mechanism deserves a step-by-step walkthrough because it shows what a modern rollup freeze actually looks like. Arbitrum’s governance docs lay out the machinery, and L1 transaction 0x079984c5…f645f770 shows that machinery in action.
Step one. The Security Council hit the 9-of-12 emergency threshold and signed an L1 transaction from 0xF06E95eF…14023F85. That transaction called the L1 Upgrade Executor at 0x3ffFbAdA…b2c3CeDd. This path defines the authority structure: only the Council and the L1 timelock can instruct the Upgrade Executor to act.
Step two. The Upgrade Executor changed the Arbitrum Delayed Inbox at 0x4Dbd4fc5…0A60BAB3f to a temporary implementation at 0x980D1F93…673FA6A859. The Delayed Inbox serves as the bridge entry point that carries messages from Ethereum into Arbitrum One. By swapping its implementation on the fly, the Council exercised a privileged power.
Step three. The temporary implementation exposed a function called sendUnsignedTransactionOverride. According to the event data, that function injected a cross-chain message and set its sender field to 0x5d3919F1…90c257Ccc, the exploiter-linked address. The InboxMessageDeliveredFromOrigin event records the forged sender directly. When Arbitrum processed that message on L2, the system treated it, for all practical purposes, as if the exploiter had signed a transfer from that address.
Step four. The L2 side processed the forged message and moved 30,765.667501709008927568 ETH out of the exploiter’s address into 0x000…0DA0, the intermediary wallet that now holds the funds pending governance action. Arbiscan confirms the L2 balance change.
Step five. In the same atomic L1 transaction, the Upgrade Executor switched the Delayed Inbox back to 0x7C058ad1…568470a10. The forged-sender capability existed for only that one transaction and then disappeared.
A few framing points matter here. This action did not roll back the chain. Arbitrum did not rewrite its history. Every state transition followed Arbitrum’s publicly described governance rules. The Council used legal machinery that already existed. What surprised many readers, especially those who assumed otherwise, is that this machinery can forge a cross-chain message on a holder’s behalf. L1s rarely allow that kind of forced-transfer capability, but most rollup governance models now include it.
The second point concerns the word “atomic.” The system completed the upgrade, injection, and restore inside a single Ethereum transaction. That matters because it limits the attack surface of the emergency path itself. An operator with continuing arbitrary access could cause far more damage than a one-shot intervention confined to a single transaction. Arbitrum intentionally designed this path to stay narrow.
Still, narrow does not mean safe by default. The emergency path exists. The 9-of-12 threshold must hold. And the community must trust the Council to use that power for theft recovery rather than, for example, censoring politically inconvenient addresses.
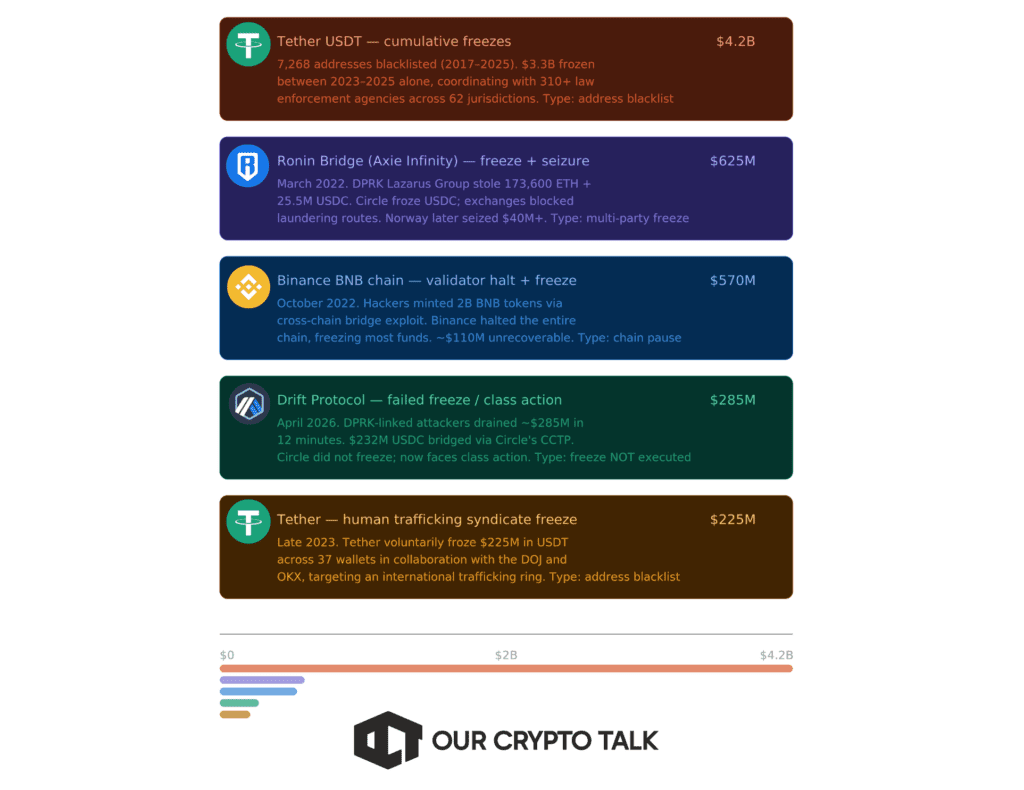
Largest Freezes In History
Arbitrum’s governance docs spell out the institutional structure. The DAO is the long-run sovereign. The Security Council is the short-run emergency actor. The Foundation is the legal wrapper and the current sequencer operator.
On the threshold rules, two numbers matter. The Council can act with 9-of-12 signers in a critical emergency. It can act with 7-of-12 signers on a slower path for routine upgrades that bypasses a DAO vote. Non-emergency changes flow through a DAO timelock that gives users several days to react. That timelock is exactly what the emergency path skips.
Membership is public. The 12 Security Council members span roughly ten organisational affiliations. They include people with ties to Offchain Labs and former Arbitrum technical leadership, Gauntlet, Conduit, Immunefi, an independent investigator, Giveth, the combined Maker / L2BEAT / TokenFlow orbit, Blockaid, the Ethereum Foundation, Certora, and OpenZeppelin. It isn’t a single-company multisig. The docs also say geographic and timezone diversity is a design goal, though the exact geographic distribution of members isn’t published.
The Arbitrum Foundation is a Cayman-registered foundation company. Its mandate includes stewarding the ecosystem, interfacing with traditional legal frameworks (including sanctions-related compliance and KYC-related implementation), and holding agreements with outside service providers. It also currently operates the sequencers for Arbitrum One and Nova, while validation on Arbitrum One became permissionless under BoLD. So the control plane spreads across four actors: token-holders who elect Council members and vote on governance, the Council that signs, the Foundation that coordinates and runs sequencing, and law enforcement or other third parties that can supply information.
On the specifics of 21 April 2026, the forum post says contributors prepared the transaction payload. The Council then verified the payload, signed, and executed. The exact subset of Council members who signed isn’t publicly enumerated in the retrieved materials. The threshold guarantees at least 9 of 12 approved. Anyone asking “who exactly pulled the trigger” doesn’t yet have a public answer below that aggregate.
That opacity is worth naming. Transparency of who signed what isn’t the same as transparency of what was signed. Arbitrum’s public docs are clear on the second. They’re less clear on the first.
No single metric works across Bitcoin and a rollup. Consensus decentralisation dominates the question for L1s. Governance and upgrade authority dominate it for rollups, because a rollup can inherit settlement from Ethereum and still keep highly centralised ordering and upgrade paths. A sensible composite uses four dimensions: consensus capture threshold, operator concentration, privileged upgrade or freeze authority, and user exit protections during upgrades. The ranking below is a composite governance-and-control read, not a pure consensus read, limited to chains where this research run has high-confidence retrieved evidence.
The real question isn’t whether freezes are possible. That’s settled. The question is when they’re legitimate and what price the system pays each time one is used.
The case in favour is direct. Emergency powers can stop cascading damage, preserve value for victims, and block second-order contagion. The 18 to 21 April 2026 sequence is the textbook example. KelpDAO paused rsETH contracts. Aave froze rsETH markets on V3 and V4. Arbitrum isolated exploit proceeds still reachable on its chain. Each action reduced the blast radius of a $290 million exploit. In a system that already accepts legal wrappers, sanctions compliance, and DAO-elected security councils, declining to use those powers during a live exploit can itself look negligent.
The case against is structural. Every successful freeze weakens the claim that control is purely key-based and politically neutral. Once an issuer or a chain can move or immobilise assets without the holder’s signature, ownership becomes contingent on the control plane behaving as advertised. That’s defensible for fraud recovery. It also creates governance-capture risk, rule-by-exception risk, and moral hazard. If the market believes sufficiently large losses will always trigger a discretionary rescue, it will under-price bridge, custodian, and governance risk in the first place.
The economics aren’t neutral either. Freezes redistribute losses. They may help direct victims or reduce protocol bad debt. They can also impose hidden costs on innocent counterparties: delayed withdrawals, pricing distortions, liquidity impairment, increased legal complexity, and a persistent “control premium” or “control discount” on affected assets and chains. The KelpDAO episode wasn’t only about one exploit. It exposed how bridge design, collateral eligibility, and the practical centralisation of DeFi emergency response actually work when they’re tested.
The framework that holds up under scrutiny is narrower than “freezes good” or “freezes bad.” It’s: is the freeze ex ante disclosed, narrow in scope, observable in execution, and auditable after the fact? Arbitrum’s April 2026 action scores reasonably well on all four. The mechanism was public in the governance docs. The scope was one exploiter-linked address. The execution is visible on-chain. The forum post documents the action. The one area where it scores less well is signer transparency, since the exact subset of Council members who approved the transaction isn’t public.
Three audiences, three takeaways.
For users, treat “can this asset or chain be frozen” as a due-diligence checklist, not an ideological position. Who can pause? Can blacklist? Who can upgrade? Is there a proxy admin? Is there a multisig? What’s the threshold? Is there a timelock? An exit window? Is the asset native or bridged? If the answer to any of those is unclear, you’re holding hidden governance risk. For bridged assets specifically, remember that you hold a contract’s promise, not the underlying asset. Ask who can change the contract.
For developers, the good practice isn’t “remove all emergency powers.” It’s minimise, separate, disclose, and delay. Separate pause powers from confiscation powers. Put routine upgrades behind long timelocks. Publish signer identities and thresholds. Rehearse incident playbooks. Avoid brittle single-verifier or single-operator assumptions where the economic blast radius is systemic. If an emergency path exists, make it narrow, bounded, observable, and auditable. The April 2026 Arbitrum action is a usable template on structure: one atomic L1 transaction, a specific and documented upgrade path, a single scoped purpose, immediate restoration of the original implementation.
For policymakers, the task is to preserve space for theft recovery and sanctions compliance without normalising arbitrary confiscation. The most defensible framework demands clear ex ante disclosure, transparent authority, public logging, narrow emergency scope, and post-action review. Without those conditions, “decentralised” becomes marketing rather than architecture. The KelpDAO-Aave-Arbitrum sequence works as a case study in both directions. Every intervention in it was publicly documented. Every one of them also used authority the protocols had reserved for themselves up front.
Blockchains are able to freeze tokens because many modern crypto systems aren’t just blockchains. They’re governance stacks. The April 2026 Arbitrum response didn’t break Arbitrum. It used Arbitrum exactly as governed. The open question isn’t whether freezes are possible. It’s who can invoke them, under what evidence, with what notice, and with what recourse.


Best Web3 Privacy Wallets 2026: Guide to Storing Crypto Privately
How to Actually Lock In on CT (While 90% Stay Broke)
Crypto Privacy in 2026: Tech, Tools & Regulation Guide
Yuma Consensus Explained: The Algorithm Behind Bittensor
Best Web3 Privacy Wallets 2026: Guide to Storing Crypto Privately
How to Actually Lock In on CT (While 90% Stay Broke)
Crypto Privacy in 2026: Tech, Tools & Regulation Guide
Yuma Consensus Explained: The Algorithm Behind Bittensor