Is Sui really a hackchain? Explore Sui hackchain narrative, 2026 DeFi exploits, root causes, and whether Sui is safe for DeFi users.
Author: Chirag Sharma
The term Sui hackchain started trending across crypto discussions in April 2026 after a series of DeFi exploits hit multiple protocols built on the network. Within a short span, several incidents involving different projects created a perception that Sui might be facing deeper structural issues.
This narrative quickly gained traction because timing matters in crypto. When multiple incidents occur close together, they often create a stronger psychological impact than isolated events spread over time. As a result, the label “hackchain” began to circulate widely across forums, social media platforms, and investor discussions.
However, narratives in crypto often move faster than facts. To properly evaluate whether Sui deserves this label, it is necessary to examine the incidents, identify their root causes, compare them with other ecosystems, and assess the actual security architecture of the network.
This article breaks down the full picture and separates signal from noise.
April 2026 was one of the most challenging months for the entire crypto industry, with total losses across chains exceeding $600 million. Against this backdrop, Sui experienced several smaller but highly visible exploits within its DeFi ecosystem.
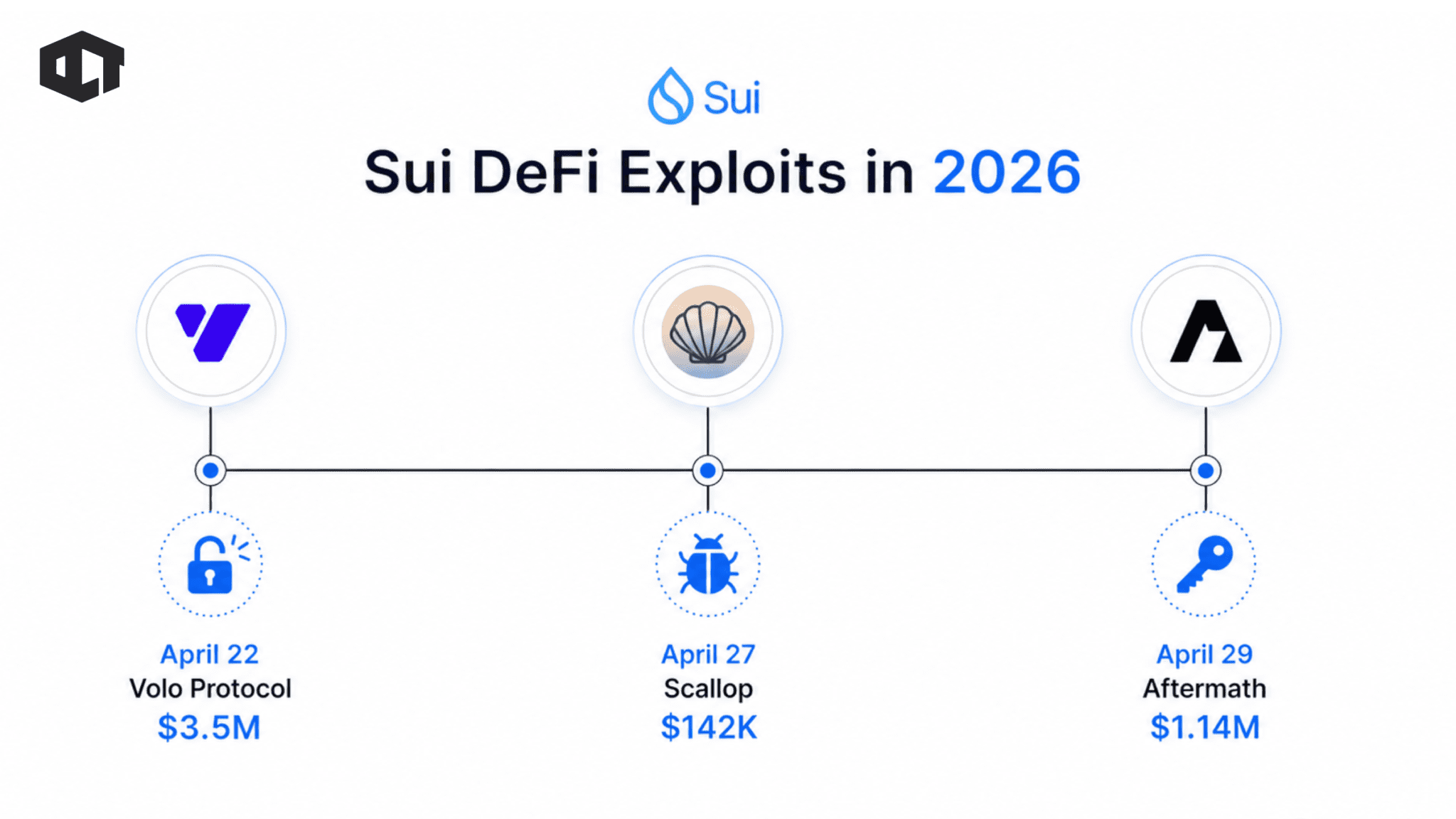
The most notable incidents included:
These incidents occurred within a short time window, amplifying their impact on market perception. While each exploit had different technical causes, they shared one important characteristic: none of them affected the Sui base layer itself.
This distinction is critical.
The Sui blockchain, including its consensus mechanism and execution layer, remained unaffected. All exploits were confined to individual applications built on top of the network. Earlier incidents from late 2025 and early 2026, such as Typus Finance and Nemo Protocol, further contributed to the narrative. Even older cases like Cetus were brought back into discussions, despite occurring under different market conditions. The clustering of these events created the impression of systemic weakness, even though the technical reality was more nuanced.
To understand the Sui hackchain narrative, you need to analyze the root causes of these exploits instead of focusing only on their outcomes. Across all incidents, a clear pattern becomes visible. Developers and teams caused most exploits through human error, poor contract management, or operational failures, rather than any fundamental flaw in the blockchain itself.
The main categories include:
For example, attackers exploited a compromised admin key in the Volo Protocol incident, which remains a well-known risk across all blockchain ecosystems. Similarly, Scallop developers introduced an uninitialized variable in a legacy contract, creating a vulnerability that attackers later exploited. These issues are not unique to Sui. Developers across rapidly growing ecosystems face similar challenges when development speed begins to outpace security practices.
The key takeaway is straightforward. These exploits occurred at the application layer, not the protocol layer. This distinction changes how you should evaluate the situation entirely.
To evaluate whether Sui deserves the “hackchain” label, it must be compared with other major ecosystems during the same period.
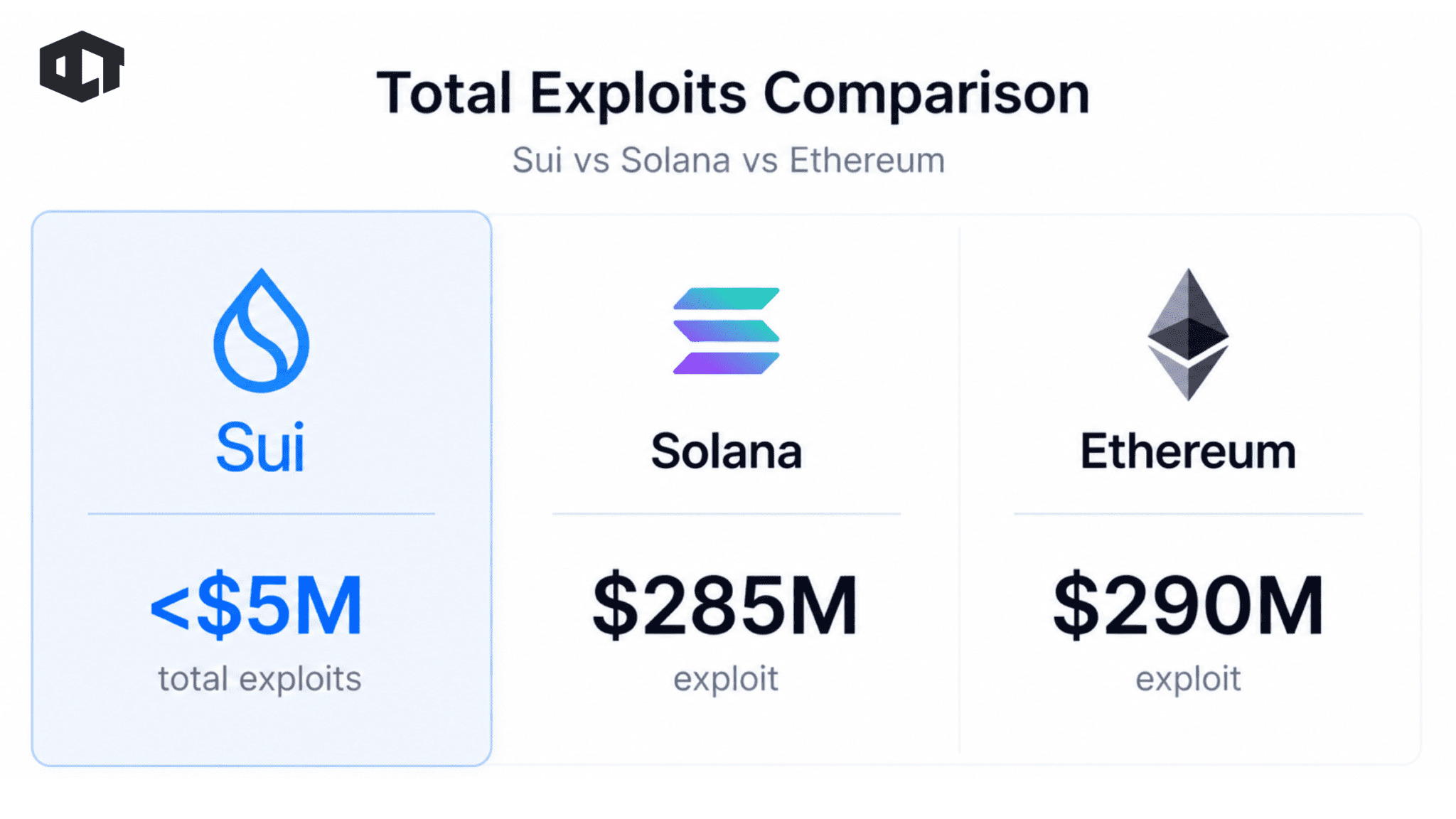
In April 2026 alone:
These numbers dwarf the total losses recorded across Sui’s incidents.
This comparison is important because it provides context. Sui’s total losses during this period remained under $5 million, which is relatively small compared to major exploits on other networks. The perception of higher risk is largely driven by the concentration of incidents rather than their scale.
Additionally, Sui demonstrated faster response times in several cases. Protocols were paused quickly, funds were partially recovered, and affected users were compensated in multiple instances. This level of response suggests a maturing ecosystem rather than a failing one.
One of the strongest arguments against the Sui hackchain narrative lies in its underlying technology. Sui is built using the Move programming language, which introduces several security advantages compared to traditional smart contract environments like Solidity.
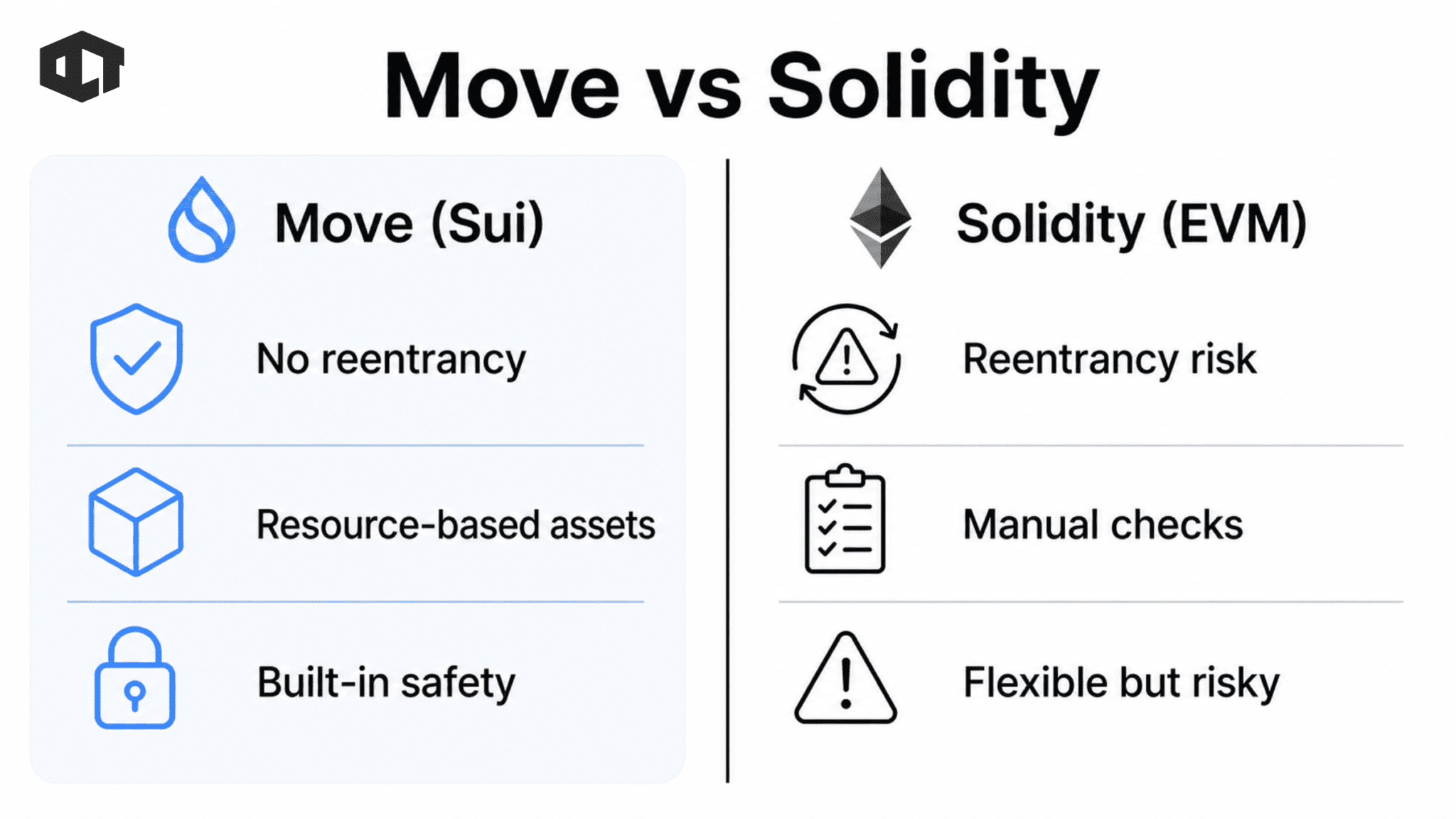
Key features include:
These features address many of the vulnerabilities that have historically plagued Ethereum-based systems. For example, reentrancy attacks, which caused some of the largest losses in crypto history, are not possible in the same way within Move-based systems. Similarly, ownership rules are enforced at the language level, reducing the risk of accidental mismanagement.
However, no programming language can eliminate all risks. Move can prevent certain classes of bugs, but it cannot protect against poor implementation, weak operational security, or flawed economic design. This is where most Sui exploits have originated.
Another important factor in the Sui hackchain narrative is growth.
Sui has experienced rapid expansion in terms of Total Value Locked (TVL), user activity, and developer participation. This growth has made the network more attractive to both builders and attackers. In crypto, capital concentration always attracts attention.
As more liquidity enters an ecosystem, the incentive for exploitation increases. Hackers actively monitor new protocols, looking for edge cases and vulnerabilities that can be exploited quickly. This dynamic is not unique to Sui.
It has been observed in every major ecosystem, including Ethereum during the DeFi boom and Solana during its rapid expansion phase. The difference is timing. Sui is currently in its early growth phase, where security practices are still evolving. This makes it more susceptible to application-level issues, especially as developers experiment with new designs.
The label “Sui hackchain” is catchy, but it oversimplifies a complex situation. The core protocol, including its consensus mechanism and execution model, has remained secure.
At the same time, the frequency of incidents highlights a real challenge. Rapid ecosystem growth has outpaced security maturity in certain areas. Developers are building quickly, and in some cases, security practices have not kept up.
This creates a temporary imbalance. However, this phase is not unusual for emerging ecosystems. Ethereum, Solana, and other major networks went through similar periods where exploits were frequent before security standards improved. The key difference is how the ecosystem responds.
So, is Sui the hackchain? The data suggests otherwise.
Sui is not fundamentally insecure, nor does it suffer from systemic protocol vulnerabilities. The recent exploits were the result of application-level errors, operational mistakes, and rapid growth dynamics.
The term “Sui hackchain” reflects market sentiment rather than technical reality.
The concerns are not misplaced. The incidents highlight the need for stronger security practices, better auditing standards, and improved developer discipline. As the ecosystem continues to grow, these factors will become increasingly important.
The next six to twelve months will be critical.If Sui’s ecosystem matures and implements stronger security measures, the narrative will shift. If not, the perception of risk may persist. For now, the evidence points to a network that is early, not broken.
All the opinions in this article are that of the author and in no way are financial advice. Our Crypto Talk and the author always suggest you do your own research in crypto and to never take anything as financial advice that you read on the internet. Check our Terms and conditions for more info.

