
Learn how to protect your crypto wallet with this seed phrase security guide. Discover best practices, common mistakes to avoid.
Author: Arushi Garg
The safest way to store a seed phrase is offline. If your crypto seed phrase never touches the internet, hackers cannot access it remotely. But offline storage does not guarantee security. Your chosen method determines how well you protect your seed phrase from loss, damage, and theft. Some approaches work for getting started, while others provide stronger long-term protection.
In 2026, the risks around seed phrases have changed. Threat actors no longer limit their attacks to obvious phishing emails. Scammers now use physical mail, compromised hardware, and AI-generated impersonation to trick users into revealing their recovery phrases. This guide breaks down the real risks and shows you exactly how to protect yourself using proven seed phrase security best practices. For broader fundamentals, see our companion guide on Crypto Security 101 (ID 2029).
Most crypto users assume hacks are technical. They think of malware or smart contract exploits. In reality, most losses happen for a much simpler reason: someone gets access to a seed phrase. A seed phrase is not just a backup. It is the wallet.
It is a list of 12 or 24 words that generates your private keys. Those private keys control your funds. If someone has the phrase in the correct order, they can recreate your wallet on another device and take full control. They do not need your phone, password, or permission.
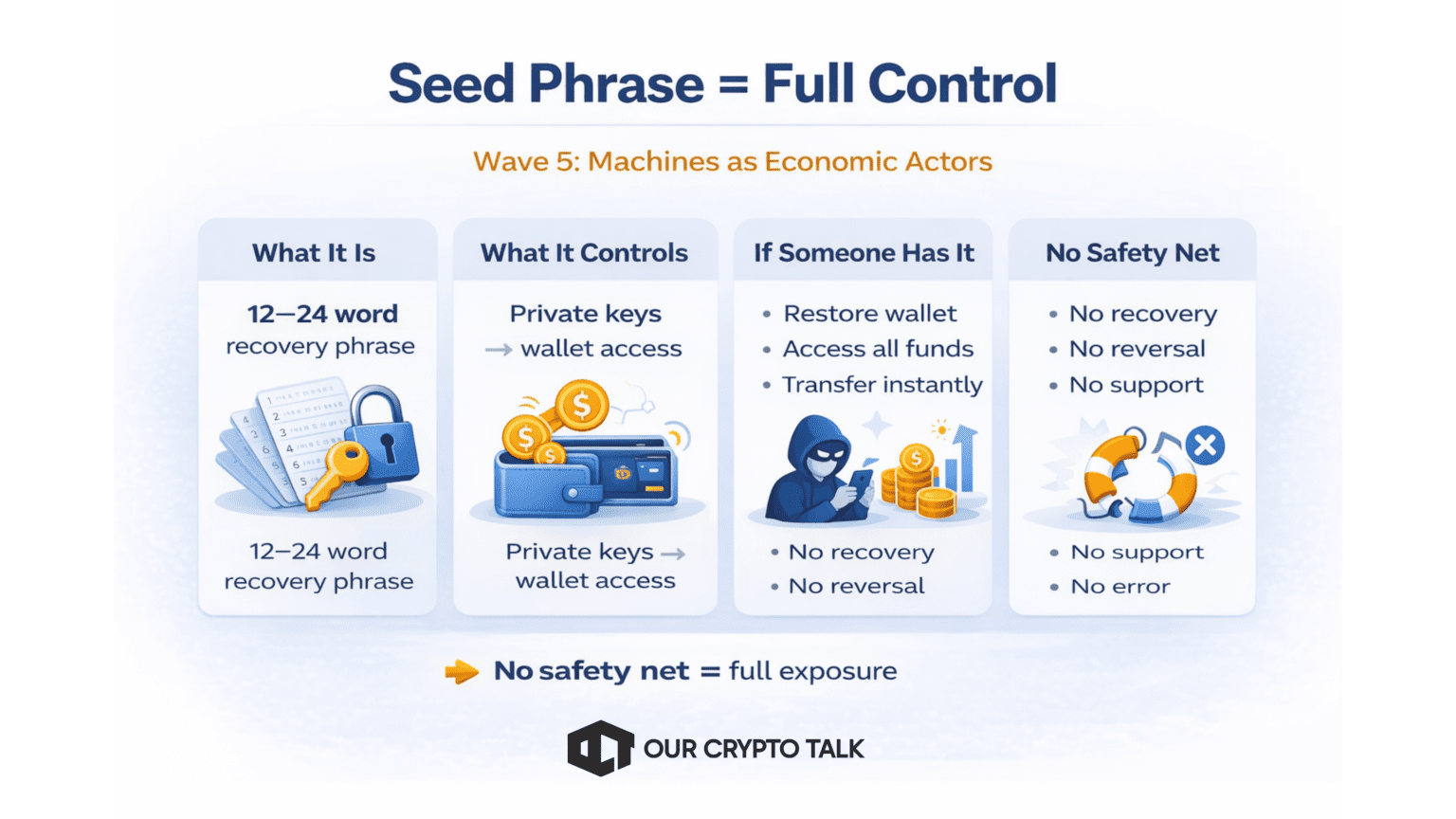
There is no second layer of verification. Control of private keys derived from the seed phrase fully determines crypto ownership.
This creates a completely different risk model compared to traditional finance. There is no recovery system if you lose your seed phrase. There is no fraud protection if someone steals your seed phrase, and no central authority can reverse a transaction or restore access. This creates two primary risks: loss and theft. If you misplace or damage your seed phrase, you permanently lose access to your funds. The blockchain still holds them, but you cannot access them anymore.
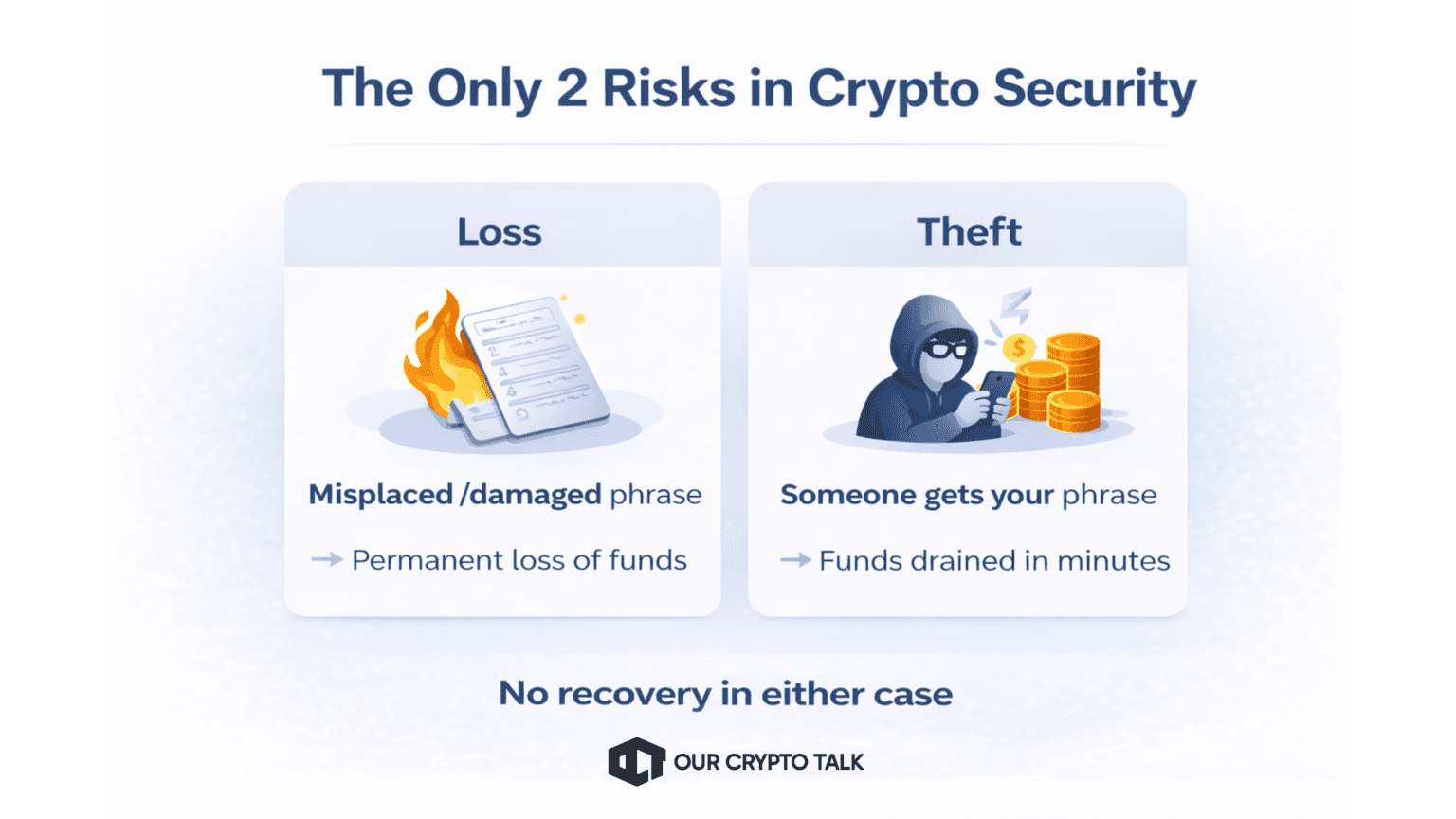
The second is theft. If someone else gets your seed phrase, they can import it into their own wallet and drain your funds within minutes. In earlier years, most attacks relied on simple phishing emails or fake apps. In 2025–2026, the threat landscape has evolved.
Attackers now target users through physical phishing campaigns that arrive as official-looking letters, supply chain vulnerabilities affecting hardware wallets, and AI-generated impersonation of support teams and wallet providers.
These attacks are more convincing and harder to detect because they target user behavior, not just technical weaknesses. Understanding these risks is the first step. Protecting your seed phrase is what keeps your crypto safe.
This is not theoretical. These attacks are already happening, and they are becoming more sophisticated.
In May 2026, users reported receiving official-looking letters posing as Ledger. These letters instructed recipients to “verify” their wallets by scanning a QR code and entering their seed phrase. This incident was covered in Scammers Target Ledger Users with Phishing Letters (ID 7107). The key shift here is the delivery method. This was not an email or a fake website link. It was physical mail sent directly to users.
That makes it far more dangerous.
Physical phishing is especially dangerous because it bypasses spam filters and email security systems entirely. It also feels more credible to users due to printed branding and official-looking language. In many cases, these messages create urgency by warning about security issues or account risks, which pushes users to act quickly without verifying the source.
Many users trust physical documents more than digital messages, and attackers exploit that assumption. Once users scan the QR code, attackers direct them to a phishing page that looks legitimate. When users enter their seed phrase, attackers gain immediate access to the wallet and drain funds within minutes.
This attack shows a clear shift in strategy. Scammers no longer rely only on digital channels. They now adapt to how users think and what they trust.
Attackers still rely on phishing as one of the most effective ways to steal crypto, but their methods have evolved significantly. In the incident covered in Trezor Warns Users of Phishing Scam (ID 8713), attackers created fake emails and websites that closely mimicked official Trezor communication. These were not obvious scams. The branding, layout, and messaging were designed to look almost identical to the real platform.
Users received emails that appeared legitimate, often warning about security issues, urgent updates, or suspicious activity. These messages pushed users to act quickly and click through to fake websites that closely mimicked the official Trezor interface, often using nearly identical domain names.
From there, attackers guided users through steps like “securing” their wallet, “verifying” their account, or “recovering” funds. While the wording varied, every path led to the same outcome: entering the seed phrase. Once entered, attackers imported the wallet and drained funds within minutes, with no way to reverse the transaction.
Modern phishing sites are highly sophisticated. They replicate official interfaces, use HTTPS to appear secure, and include realistic prompts that remove obvious signs of fraud. As a result, even experienced users can struggle to spot the scam, allowing attackers to succeed by convincing users to reveal their seed phrase.
The newest risk is also the hardest to detect. AI has changed how scams are executed. Instead of relying on poorly written messages or obvious tricks, attackers now use advanced tools to create highly convincing interactions that feel real.
Attackers are using AI to:
Attackers are now using AI to generate phishing emails with natural language, create fake support chats that respond in real time, imitate human voices in phone calls, and build automated systems that guide users through fake recovery processes. These tools make scams more convincing and harder to detect.
Threat actors design these attacks to eliminate the warning signs users once depended on. In the past, phishing emails often had clear red flags. Poor spelling, strange formatting, or awkward language made them easier to spot. That is no longer the case. AI-generated content is clean, professional, and context-aware. It can reference real platforms, use correct terminology, and respond convincingly to user questions. The same applies to fake support interactions. A user might believe they are speaking to a legitimate support agent on chat or even over the phone. The conversation feels natural, helpful, and urgent.
At some point, the attacker introduces a request:
Everything leading up to that moment is designed to build trust. There is no obvious scam signal. No broken English. No suspicious formatting. Just a believable interaction that leads the user to reveal their seed phrase. That is what makes AI-assisted social engineering so effective. It does not break security systems. It bypasses them by convincing the user to give access willingly.
Not all crypto risks come from phishing or user mistakes. Hardware wallets themselves can introduce vulnerabilities if there are weaknesses in firmware or manufacturing processes. A recent example is the Tangem firmware-related issue, which raised concerns about supply chain security in hardware wallets. In this case, the issue highlighted how users depend on wallet manufacturers to implement secure firmware and maintain transparency around updates. Even if a device is designed to keep private keys offline, flaws at the firmware level can still create risk if not properly handled.
This incident shows that crypto security is not only about avoiding scams. It also involves choosing trusted wallet providers, understanding how devices are built, and staying updated on security disclosures that may affect your funds.
If your seed phrase is stored digitally, it is exposed. There are no safe exceptions. Many users choose digital storage because it feels convenient and secure. Notes apps are easy to access. Cloud storage feels protected by passwords. Password managers seem designed for sensitive data. But all of these methods introduce risk that is unacceptable for something as critical as a seed phrase.
This includes:
This includes storing seed phrases in notes apps, saving screenshots in your gallery, uploading them to cloud storage services like Google Drive or iCloud, keeping them in email drafts or messages, or even storing them in password managers. All of these methods create a digital copy, which increases exposure to security risks.
Each of these creates a digital copy of your seed phrase. The moment that happens, your security depends on multiple systems you do not fully control.
Many apps automatically sync data across devices. A note saved on your phone may also exist on your laptop, tablet, and cloud account. This creates multiple points of failure. If attackers compromise any of those devices or accounts, they can access your seed phrase. Even if your primary device is secure, a weaker secondary device can become the entry point for an attacker.
Phones and computers stay online almost all the time. This makes them targets for malware.
Malicious software can capture keystrokes as you type, take screenshots in the background, scan files and notes for sensitive data, and even access clipboard history. These attacks often run silently, making them difficult to detect until your funds are already gone.
Cloud storage and email accounts are frequent targets for attackers. Phishing, password leaks, and reused credentials can all lead to account compromise.
If an attacker gains access to your account, they can:
Even if you delete a file, copies may still exist in backups or archives.
Encryption is often misunderstood.
Device encryption protects your data if someone physically steals your phone and tries to access it without unlocking it. It does not protect you from online threats.
Encryption does not stop:
If your seed phrase is stored digitally, encryption alone is not enough.
Yes, someone can steal your crypto if your seed phrase is stored digitally. Any digital copy creates a potential attack surface. If your device is compromised, malware can scan files, capture screenshots, or read stored notes to extract your seed phrase. If your cloud account or email is breached, attackers can search for saved phrases and gain instant access to your wallet.
Once attackers have the seed phrase, they can import it into their own wallet and transfer all funds within minutes. There is no way to reverse this action.
This is why one of the most important seed phrase security best practices is to keep your recovery phrase completely offline at all times.
If it never touches the internet, it cannot be hacked remotely. But offline storage is not automatically secure. The method you choose determines whether your seed phrase is protected from loss, damage, and theft. Some approaches are good enough for getting started. Others are built for long-term protection.
Writing your seed phrase on paper is the simplest and most accessible method. It requires no special tools and can be done immediately when setting up a wallet. For beginners, this is often the first step toward securing funds properly.
Best practices:
Paper works because it keeps your seed phrase completely offline. However, it has clear limitations.
Limitations:
Paper is a good starting point, but it should not be treated as a permanent solution, especially for long-term holders or larger amounts of crypto.
A metal seed phrase backup is designed for durability and long-term protection. Instead of relying on ink and paper, your seed phrase is engraved, stamped, or assembled using metal components. This makes it far more resilient under extreme conditions.
Common options include:
These devices are built to survive scenarios that would destroy paper backups.
They protect against:
The goal is simple. Even if everything else is destroyed, your seed phrase remains intact and readable.
When choosing a metal backup, focus on function rather than branding.
What to look for:
Metal backups require more effort and a small upfront cost, but they provide a level of protection that paper cannot match.
For anyone holding a meaningful amount of crypto or planning to store assets long term, a metal seed phrase backup is the standard.
How you store your seed phrase matters. But where you store it matters just as much. Many users focus on the storage method, such as paper or metal, and ignore location strategy. This creates a hidden risk. Even a perfectly stored seed phrase can be lost or stolen if it exists in only one place.
The goal of a strong location strategy is simple. Remove single points of failure.
Best practices:
You can store your seed phrase in several secure ways, such as a safe at home, a bank safe deposit box, or a trusted secondary location like a family member’s safe.
Each option has tradeoffs. A home safe offers quick access but may be vulnerable to theft. A bank vault provides strong physical security but may limit access in emergencies. The right approach often involves using more than one location.
It also reduces the risk of total failure. Even if one backup is compromised, the others remain intact. However, more locations also mean more responsibility. Each copy must be stored securely and handled carefully. Poor execution can increase exposure instead of reducing it. The objective is not to create complexity. It is to create resilience. A well-planned location strategy ensures that your seed phrase is never dependent on a single place, person, or event.
For many users, secure physical storage is enough. But as the value of your holdings increases, the risk profile changes. At higher levels, the goal is not just protection. It is risk distribution. Two advanced approaches are commonly used to reduce single points of failure: Shamir’s Secret Sharing and multisig wallets.
Shamir’s Secret Sharing is a cryptographic method that splits a seed phrase into multiple parts, called shares. Instead of storing one complete seed phrase, you create several shares that work together.
For example:
This is often referred to as a “2-of-3” setup. The key idea is simple. No single share is useful on its own. If someone finds one share, they cannot access your wallet. If one share is lost, you can still recover your funds using the remaining ones.
Some hardware wallets, including Trezor, support Shamir’s Secret Sharing natively, making it easier to implement without external tools. However, this approach introduces complexity.
This method works best for users who hold significant value in crypto, want redundancy without relying on a single backup, and are comfortable managing multiple secure storage locations. When implemented correctly, SSS provides a strong balance between security and recoverability.
Multisig, or multi-signature wallets, take a different approach. Instead of splitting one seed phrase, multisig uses multiple independent keys. Each key is tied to a separate wallet or device. To approve a transaction, a minimum number of keys must sign it.
For example:
This changes how control works. With a standard wallet, one seed phrase controls everything. With multisig, no single key has full authority.
The main difference between Shamir’s Secret Sharing and multisig wallets lies in their structure. Shamir’s Secret Sharing splits a single secret into multiple parts, whereas multisig wallets generate several independent secrets that must work together to authorize transactions.
Multisig wallets offer several advantages. A single compromised key cannot move funds, providing strong protection against theft or device compromise. They are particularly useful for situations where multiple parties need shared control over the same funds.
At the same time, multisig setups come with tradeoffs. They are more complex to set up and maintain, require careful coordination between keys, and have recovery processes that can be more involved than standard wallets.
Multisig is typically used by high-value individual holders, teams or organizations managing shared funds, and advanced users who want layered security. Beginners may not need multisig, but when implemented correctly, it is one of the most robust security models available, offering both redundancy and strong protection.
If you only act on one part of this guide, make it this.
These are the core seed phrase security best practices you should implement immediately:
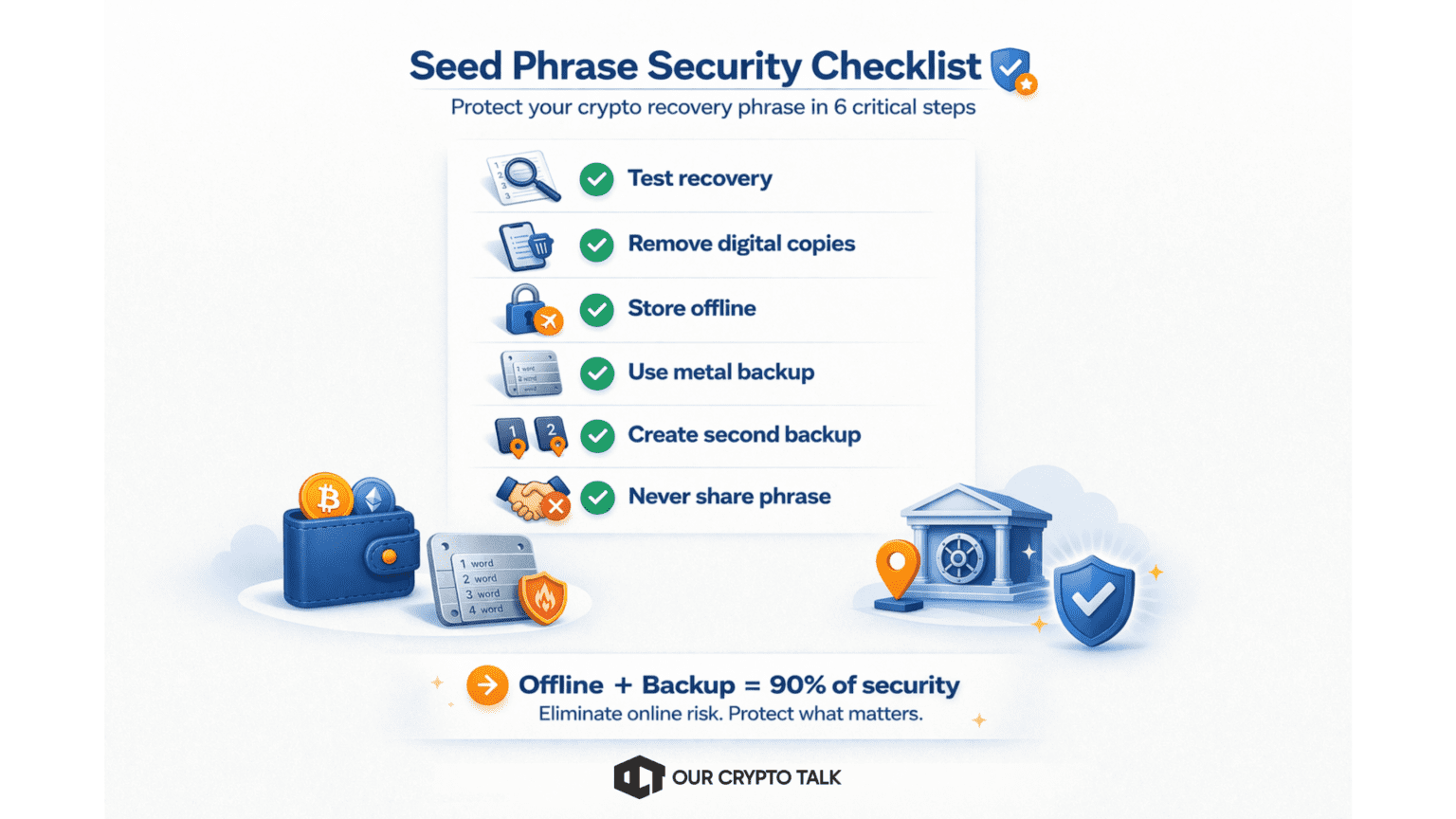
Seed phrase risks are not theoretical. They are real, and they continue to evolve as attackers adapt. But protecting yourself does not require advanced tools or technical expertise. If your seed phrase is offline, securely stored, and properly backed up, you eliminate the majority of risks in crypto. You do not need perfect security. You need consistent and disciplined security and that is something entirely within your control.


Best Web3 Privacy Wallets 2026: Guide to Storing Crypto Privately
How to Actually Lock In on CT (While 90% Stay Broke)
Crypto Privacy in 2026: Tech, Tools & Regulation Guide
Yuma Consensus Explained: The Algorithm Behind Bittensor
Best Web3 Privacy Wallets 2026: Guide to Storing Crypto Privately
How to Actually Lock In on CT (While 90% Stay Broke)
Crypto Privacy in 2026: Tech, Tools & Regulation Guide
Yuma Consensus Explained: The Algorithm Behind Bittensor