
The Dritan Kapllani case explained. ZachXBT exposed the 18-year-old as Co-Conspirator 1 in a federal complaint over $19M in crypto thefts.
Author: Tanishq Bodh
On May 12, 2026, on-chain investigator ZachXBT posted an eight-part thread on X. In it, he publicly named Dritan Kapllani Jr., an 18-year-old US-based threat actor, as the figure behind roughly $19 million in crypto social engineering thefts.
The timing was deliberate. Specifically, ZachXBT held off publishing his evidence until federal prosecutors unsealed a criminal complaint the day before, on May 11. That complaint charged Trenton Johnson with conspiracy tied to a 185 BTC theft. Importantly, the same document names Dritan Kapllani as Co-Conspirator 1, or CC-1.
Dritan Kapllani himself has not been formally charged at the time of writing. However, the on-chain evidence, the Discord recording, and the federal filing now sit in the public record together.
Based on ZachXBT’s investigation, Dritan Kapllani is an 18-year-old US-based individual with reported Albanian heritage. Notably, he is described as part of the hacker community known as “The Com.” Furthermore, he has been previously linked to crews such as ACG and 41/RM Boyz, many of whose members have already been arrested.
According to ZachXBT, Dritan Kapllani flexes extensively on Instagram and Telegram. Specifically, his posts show luxury cars, expensive watches in the Richard Mille range, private jets, club nights, and stacks of cash. The visual style is loud. Importantly, the on-chain trail behind that lifestyle is what ultimately exposed him.
There is also a structural detail worth flagging. Specifically, Dritan Kapllani allegedly operated with what insiders call “plot armor.” For context, law enforcement typically delays prosecuting juveniles. As a result, while associates around him kept getting arrested, he reportedly evaded charges as a minor. That window appears to be closing now that he has turned 18.
On April 23, 2026, Dritan Kapllani allegedly joined a “Band 4 Band” voice channel on Discord. For context, B4B is a bragging competition common in cybercriminal circles. Specifically, threat actors compete to prove who controls more stolen crypto.
During that call, Dritan Kapllani reportedly screen-shared his Exodus wallet. Notably, the wallet held $3.68 million in assets at the moment of the screenshare. According to ZachXBT, the goal was to prove he had more money than another threat actor on the call.
The ETH address tied to that wallet: 0x4487db847db2fc99372a985743a26f46e0b2bba6
Furthermore, ZachXBT published both screenshots and a video clip of the moment. Other usernames present on the call reportedly included “dh sos,” “The Punisher,” and “kenele.” For an opsec failure, this one is hard to beat.
ZachXBT’s thread maps two main wallet clusters tied to Dritan Kapllani, each with its own theft history.
The first cluster connects to a $13 million theft on March 14, 2026. Specifically, the victim lost 185 BTC after a social engineering attack. According to ZachXBT, the funds moved through multiple Bitcoin intermediary addresses, then crossed a bridge to Ethereum. After that, they landed in at least four wallets allegedly controlled by Dritan Kapllani. Notably, the trail terminates at the same 0x4487 address shown during the Discord flex.
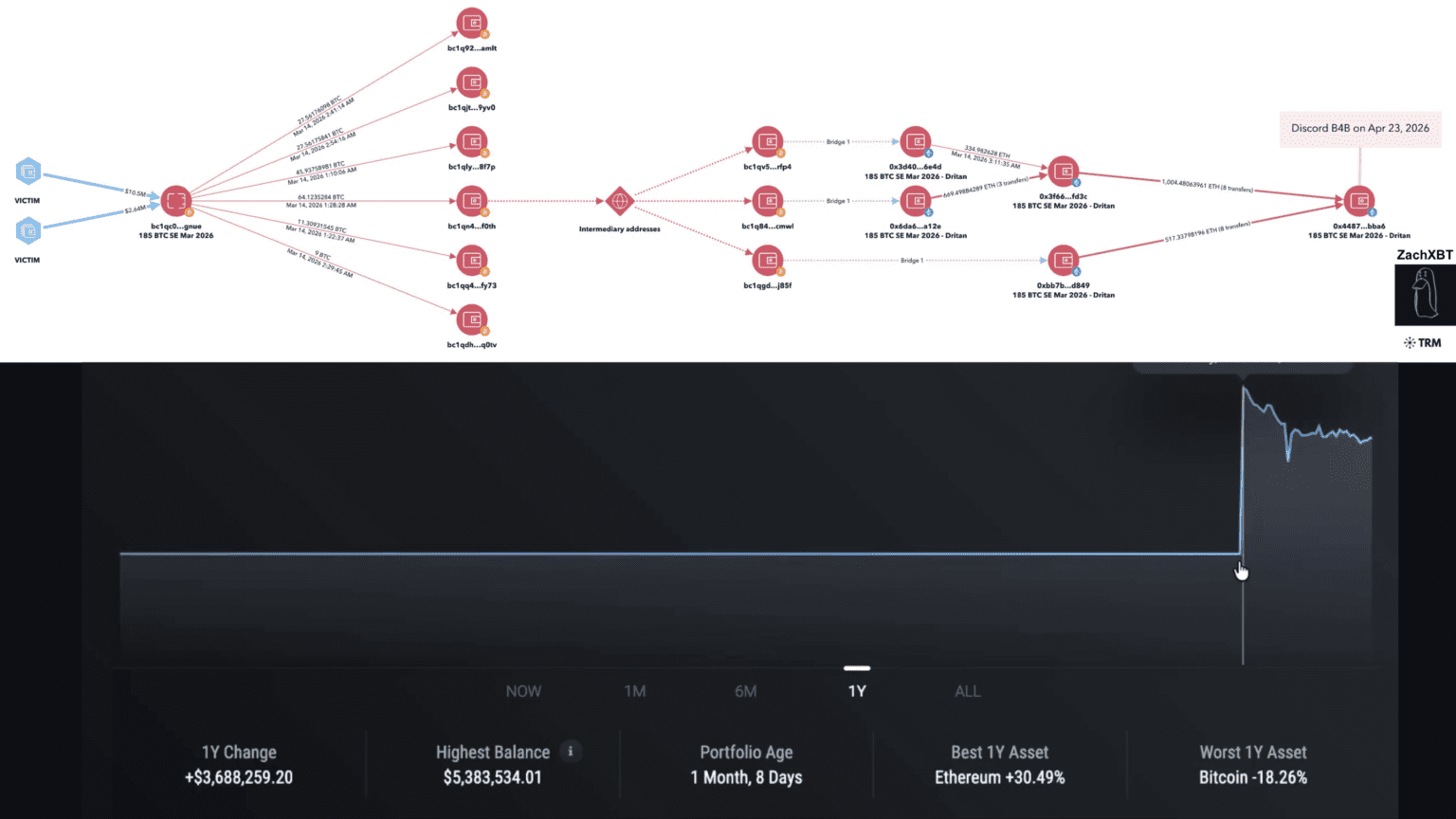
ZachXBT verified the wallet looked accurate. Specifically, funds moved to the same laundering service within minutes of the 185 BTC theft. Furthermore, between the March 14 theft and the April 23 Discord call, roughly $1.6 million had already been spent or laundered.
The second wallet, 0x97da0685dbba50b4cbabb0ca9e8336f4fbe41122, traces back to at least $5.85 million stolen across five separate high-confidence social engineering thefts in 2025. Specifically, the thefts spanned August, September, and October 2025, each tied to a distinct victim.
Importantly, a TRM Labs flow diagram confirms the on-chain link between those 2025 victims and two Dritan Kapllani controlled wallets. As a result, the pattern shows repeated social engineering attacks feeding the same laundering infrastructure over at least seven months.
Combined, the two clusters bring the alleged total to roughly $19 million in social engineering thefts.
On May 11, 2026, prosecutors unsealed a criminal complaint against Trenton Johnson. Notably, Johnson faces up to 40 years in prison for his alleged role in the 185 BTC theft. Court documents reportedly include messages between Johnson and CC-1 during the theft and laundering window.
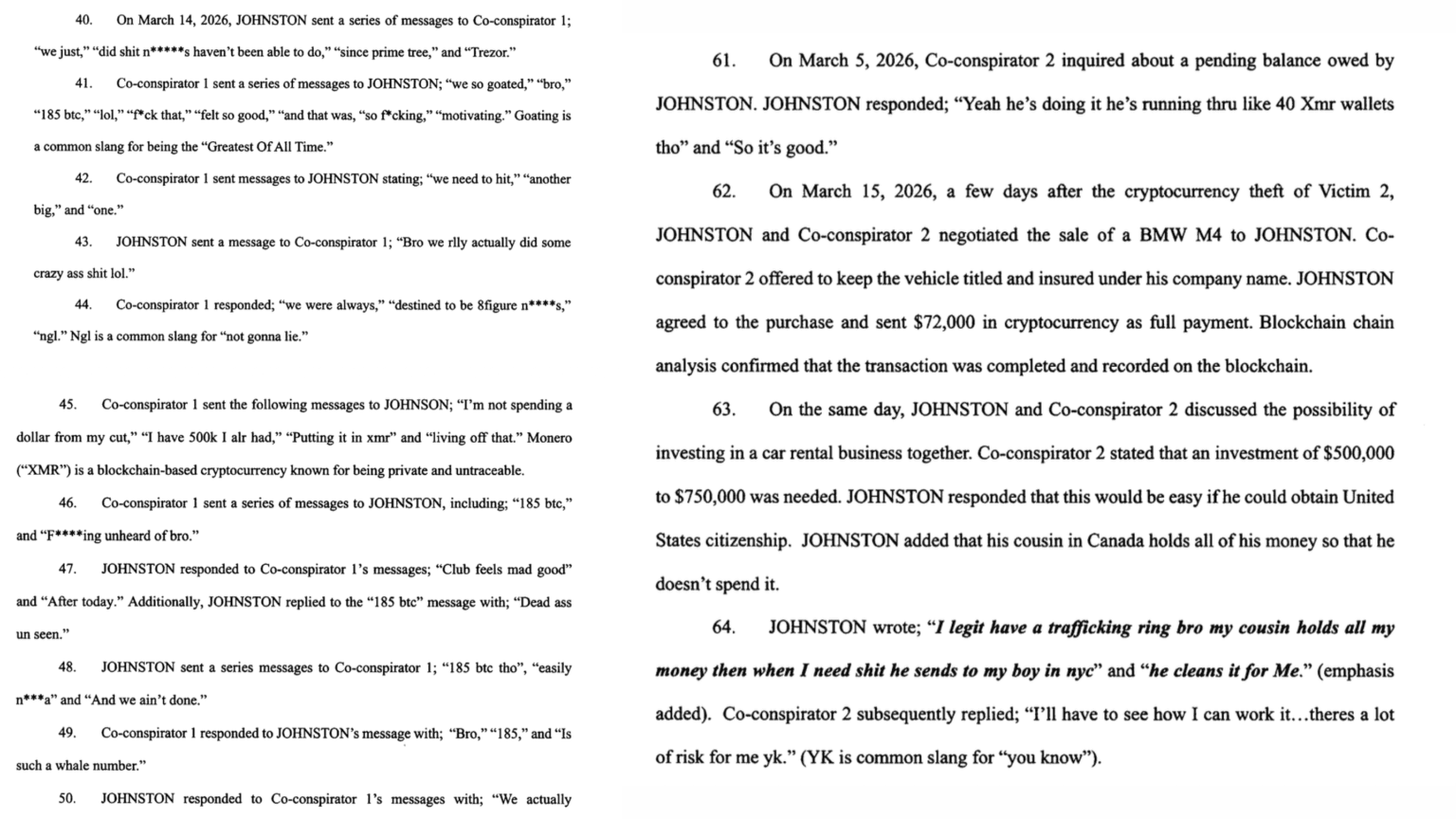
CC-1 is Dritan Kapllani.
Separately, the meme coin KOL operating under the handle @yelotree was also charged. Specifically, he allegedly assisted in money laundering through a Miami rental car business. As a result, he faces up to 30 years.
For now, Dritan Kapllani himself remains uncharged in public filings. However, the CC-1 naming, combined with the on-chain evidence and the Discord recording, makes this a high-profile case to watch over the coming weeks.
The Dritan Kapllani case fits a pattern ZachXBT has documented repeatedly throughout 2025 and 2026. Specifically, social engineering crews target high-net-worth crypto holders through impersonation scams. Then they launder funds through bridges and mixers. Finally, they flex the proceeds on social media until the on-chain trail catches them.
Notably, Dritan Kapllani previously did a B4B with John Daghita, also known as “Lick.” For context, ZachXBT exposed Lick’s $46 million theft from the US government in January 2026. As a result, that exposure led to Lick’s arrest. The pattern repeats.
There are three clean takeaways from this case.
First, social engineering is now the dominant attack vector against crypto holders. Specifically, it does not rely on smart contract exploits or zero-days. Instead, it relies on convincing humans to give up seed phrases. Therefore, the attack surface is your phone, your support tickets, and your trust.
Second, opsec failure compounds. Dritan Kapllani allegedly bragged on Discord, flexed on Instagram, and laundered into traceable addresses. Each step lowered the cost of catching him.
Finally, on-chain transparency works both ways. Specifically, the same public ledger that scammers use to move funds is also the ledger ZachXBT used to map every hop. Eventually, the trail leads home.
A few open questions remain. First, whether federal prosecutors move from the CC-1 naming to formal charges against Dritan Kapllani in the coming weeks. Second, whether more associates in “The Com” get pulled into expanded indictments. Finally, how the broader social engineering crew ecosystem responds, given that flex culture is now a public liability.
For crypto holders, the lesson is simple. Specifically, never share seed phrases. Never trust unsolicited support contacts. Furthermore, always verify hardware wallet communications through official channels. The Dritan Kapllani case is a reminder that the weakest link in crypto security is rarely the chain itself.


Best Web3 Privacy Wallets 2026: Guide to Storing Crypto Privately
How to Actually Lock In on CT (While 90% Stay Broke)
Crypto Privacy in 2026: Tech, Tools & Regulation Guide
Yuma Consensus Explained: The Algorithm Behind Bittensor
Best Web3 Privacy Wallets 2026: Guide to Storing Crypto Privately
How to Actually Lock In on CT (While 90% Stay Broke)
Crypto Privacy in 2026: Tech, Tools & Regulation Guide
Yuma Consensus Explained: The Algorithm Behind Bittensor