
The biggest crypto hacks of all time exposed the same flaw: centralized custody. From Bybit's breach to Mt. Gox, here's every major hack.
Author: Kritika Gupta
On February 21, 2025, crypto markets did not simply absorb bad news. They seized up around it with some of the biggest crypto hacks.
What began as a routine internal treasury transfer at Bybit quickly escalated into one of the most consequential crypto hacks the industry had ever witnessed. Within hours, attackers had drained nearly 400,000 ETH. At prevailing market prices, losses approached $1.5 billion. Traders watched the unfolding chaos across exchange dashboards and social feeds. Liquidity tightened across venues. Risk desks recalculated exposure before the full scope of the breach became clear.
Nothing about the breach resembled the old cartoon version of a crypto hack. The machinery of the underlying networks kept running exactly as intended. That, in some ways, made the event more unsettling. The exploit exposed a harder truth about modern crypto markets: the biggest risks often do not sit at the protocol layer. They sit in the institutions, interfaces, workflows, and custody systems built on top of it.
For years, the industry sold a compelling thesis. Crypto would replace trust in people and institutions with trust in code and cryptography. It would reduce single points of failure. It would allow users to hold assets directly, verify ownership transparently, and opt out of fragile intermediaries. That promise was not entirely false. Base-layer systems have shown remarkable resilience. However, the commercial crypto ecosystem that grew around those systems has repeatedly reintroduced the same concentrations of risk that decentralized technology was supposed to remove.
That is the real story told by the history of major crypto hacks. They are not just a parade of technical mishaps. They are a record of structural failure. Each breach arrives with its own jargon, its own postmortem, its own villain, and its own favorite explanation. One year it is weak key management. Another year it is validator concentration. Then it is a bridge design flaw, a governance gap, a cloud dependency, a wallet compromise, or an approval interface issue. Yet when these incidents are placed side by side, the pattern becomes harder to ignore.
On February 21, 2025, the market learned again how quickly confidence can evaporate when a top-tier venue loses control of funds.
Bybit was not some obscure exchange operating at the margins. It was large, liquid, globally recognized, and widely treated as part of the industry’s mature infrastructure. That status mattered because it shaped how traders interpreted the breach. When a small venue gets hacked, users treat it as another reminder to avoid weak operators. When a major venue gets hit at record scale, the message lands differently. It raises the possibility that even the better-capitalized and more operationally sophisticated players still sit on fragile foundations.
Initial reporting suggested attackers had exploited the exchange during what should have been a standard treasury movement. The scale of the theft became clear quickly. Nearly 400,000 ETH had been drained. At prevailing prices, the value reached roughly $1.5 billion. That number made it the largest hack in crypto history, surpassing previous benchmark events that had dominated security discussions for years.
The mechanics of the exploit also mattered. The attackers did not defeat Ethereum. They did not unravel core cryptography. Instead, they targeted the machinery around custody. Reports later tied the operation to the Lazarus Group, the North Korea-linked cybercrime apparatus that has become synonymous with high-value crypto theft.
That distinction is crucial. Crypto often frames security as a question of wallet type, signature threshold, or storage location. Cold wallet versus hot wallet. Single sig versus multisig. Hardware protection versus software convenience. Those categories still matter. Yet Bybit showed, very clearly, that the security of a custody system depends on more than the cryptographic rules at the end of the process.
The following timeline presents the largest confirmed crypto hacks above one hundred million dollars. The list is ordered by dollar impact rather than date because that ranking shows, more clearly than chronology alone, where risk concentration has produced the heaviest losses.
Attackers compromised elements of a multisignature treasury workflow and redirected funds during an internal transfer process. The breach became the largest crypto hack on record and immediately sent shockwaves across the market because Bybit was widely seen as one of the industry’s more sophisticated centralized trading platforms. Much of the stolen value remained unrecovered for an extended period, and the incident forced the entire industry to reexamine assumptions about institutional custody maturity. More importantly, the hack showed that even advanced treasury systems remain vulnerable when attackers can manipulate operational workflows, software dependencies, or approval interfaces rather than attack the underlying blockchain itself. The scale of the theft also made one thing clear: modern exchange security risks increasingly sit in the layers around custody, not just in the wallets themselves.
Attackers compromised validator keys and used that access to authorize massive unauthorized withdrawals. Ronin showed that bridge systems can market decentralization while still concentrating operational authority in a small enough validator set to become a high-value target. Because Ronin served as the bridge infrastructure behind Axie Infinity’s booming ecosystem, the exploit also exposed how quickly user growth and asset concentration can outpace security design. The incident became one of the clearest examples of how cross-chain infrastructure can inherit the language of decentralization while still relying on trust assumptions that look surprisingly narrow in practice. In the aftermath, developers expanded validator participation and strengthened monitoring, but the hack remained a defining warning about the dangers of under-decentralized bridge architecture.
A smart contract exploit allowed attackers to redirect hundreds of millions of dollars across chains. Although most funds were eventually returned, the event exposed the fragility of interoperability infrastructure and the extraordinary stakes attached to cross-chain logic. Poly Network had positioned itself as a major connector between blockchain ecosystems, which made the exploit feel larger than a single protocol incident. It highlighted how bridges and interoperability systems often hold enormous strategic importance while still relying on highly complex code and privileged contract permissions. Even though the hacker later returned much of the stolen crypto, the breach still damaged confidence by proving that a single exploit in cross-chain infrastructure could threaten multiple ecosystems at once. It was one of the first moments when the market fully grasped how dangerous bridge risk could become.
Amid bankruptcy chaos, unauthorized transfers drained hundreds of millions of dollars from associated wallets. The event deepened the collapse of trust surrounding FTX and underscored how governance failure can magnify security failure. By the time these transfers occurred, the exchange had already become the center of one of the most damaging corporate collapses in crypto history. That context mattered because the wallet drain did not land as an isolated hack. It landed as part of a broader picture of disorder, weak internal controls, and a near-total breakdown in organizational trust.
Attackers exploited bridge verification logic and minted synthetic assets without valid collateral backing. Rapid validator coordination froze a significant share of funds, but the incident triggered a broader debate about how much centralized emergency control decentralized systems should tolerate. On one hand, the fast response prevented an even larger realized loss. On the other hand, it showed that the network could coordinate intervention quickly enough to halt damage, which raised uncomfortable questions about where authority truly sat.
Attackers stole more than $500 million worth of NEM from a hot wallet connected to the internet for operational convenience. Users were later reimbursed, but the breach became a landmark case in exchange custody risk and regulatory response. Coincheck showed that even after earlier exchange failures, major platforms still kept enormous balances in exposed environments because liquidity, speed, and user experience continued to shape operational choices. The incident sparked outrage in Japan and pushed regulators toward stricter oversight of exchange licensing, custody standards, and internal controls. It also reinforced a lesson that would reappear in later years: exchanges may improve security incrementally, but the commercial pressure to maintain accessible liquidity often preserves the very attack surface hackers want most. Coincheck became a pivotal case because it proved that the industry had learned from earlier disasters only partially, not completely.
The collapse of Mt. Gox remains one of the biggest crypto hacks. Attackers siphoned funds over years while weak controls and poor accounting concealed the scale of the losses. The exchange eventually failed, reshaping how the industry thought about custody forever. At its peak, Mt. Gox handled the majority of Bitcoin trading volume, which meant the failure of one platform effectively became a systemic event for the whole market. The breach did not just expose bad security. It exposed the danger of allowing one intermediary to become too central to a supposedly decentralized financial ecosystem.
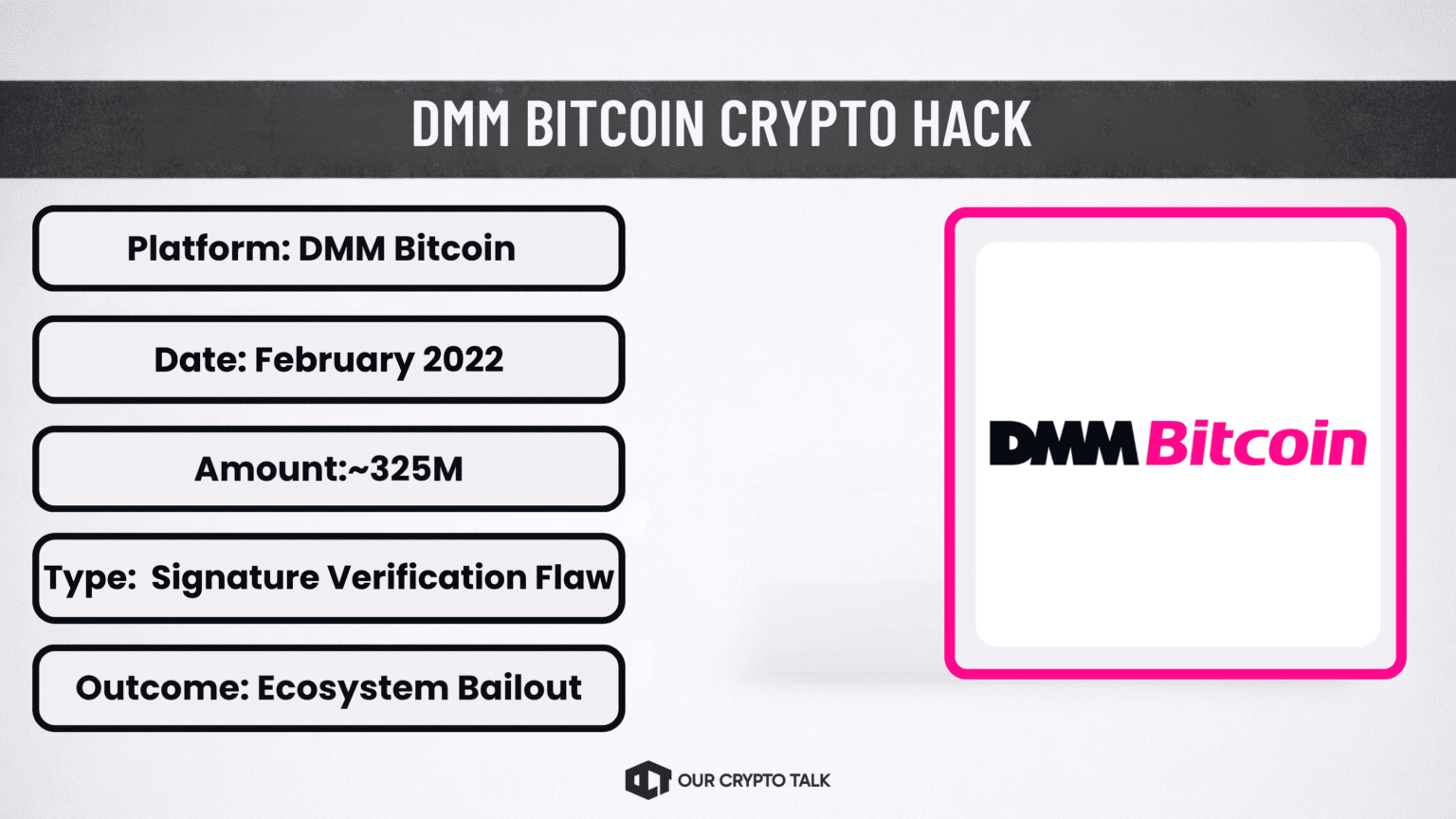
A signature verification flaw enabled attackers to mint wrapped assets without proper backing. The exploit highlighted the risk embedded in trusted messaging and validation layers, while a bailout prevented the incident from becoming even more destabilizing.
A private key compromise led to one of the largest exchange thefts of the year. The hack renewed attention on key management procedures, internal access controls, and the challenge of securing large custodial balances in increasingly hostile threat environments.
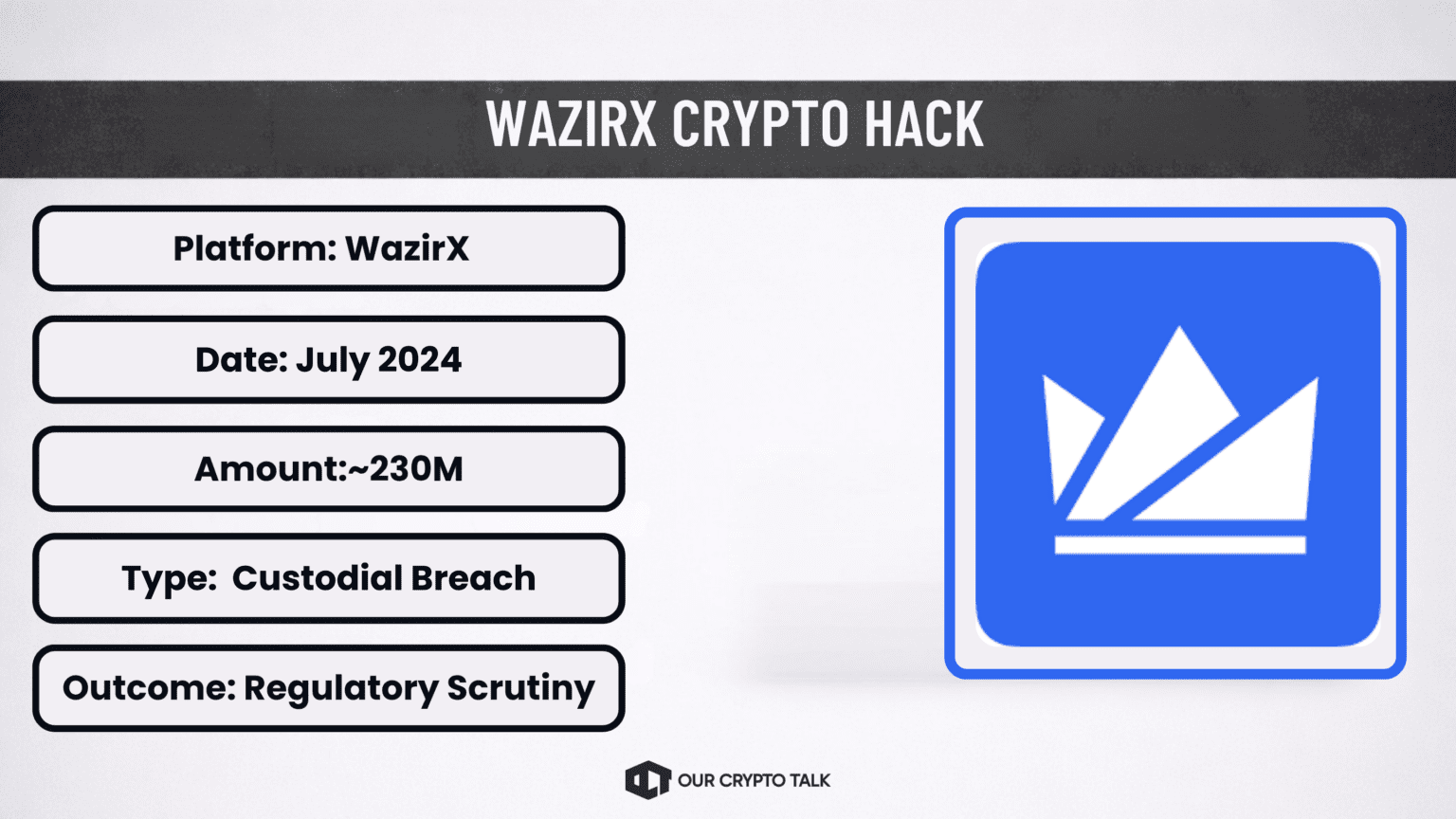
A major custodial breach at one of India’s best-known crypto platforms reignited debates around reserve transparency, operational resilience, and regional exchange supervision. The case also showed how exchange concentration risk remains acute in fast-growing retail markets.
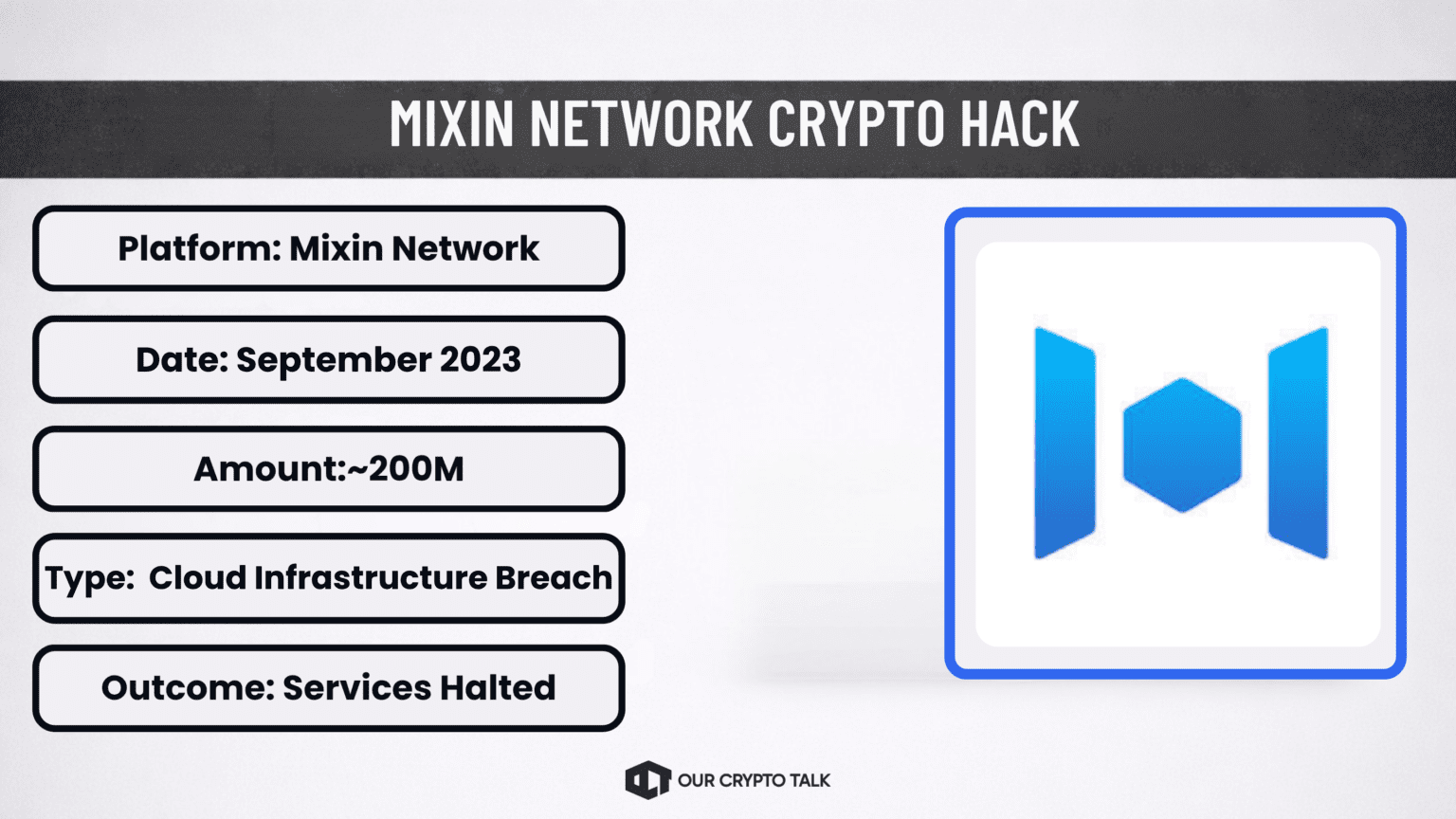
Attackers breached cloud infrastructure used by the network’s custodial services, exposing the danger of hybrid architectures that combine onchain asset models with offchain centralized operational dependencies. That point made the Mixin case especially important. Many crypto systems present themselves as decentralized at the asset or protocol layer while still relying heavily on conventional cloud services, backend coordination, or centralized infrastructure providers for critical operations. Mixin showed how those offchain dependencies can become the weak link.
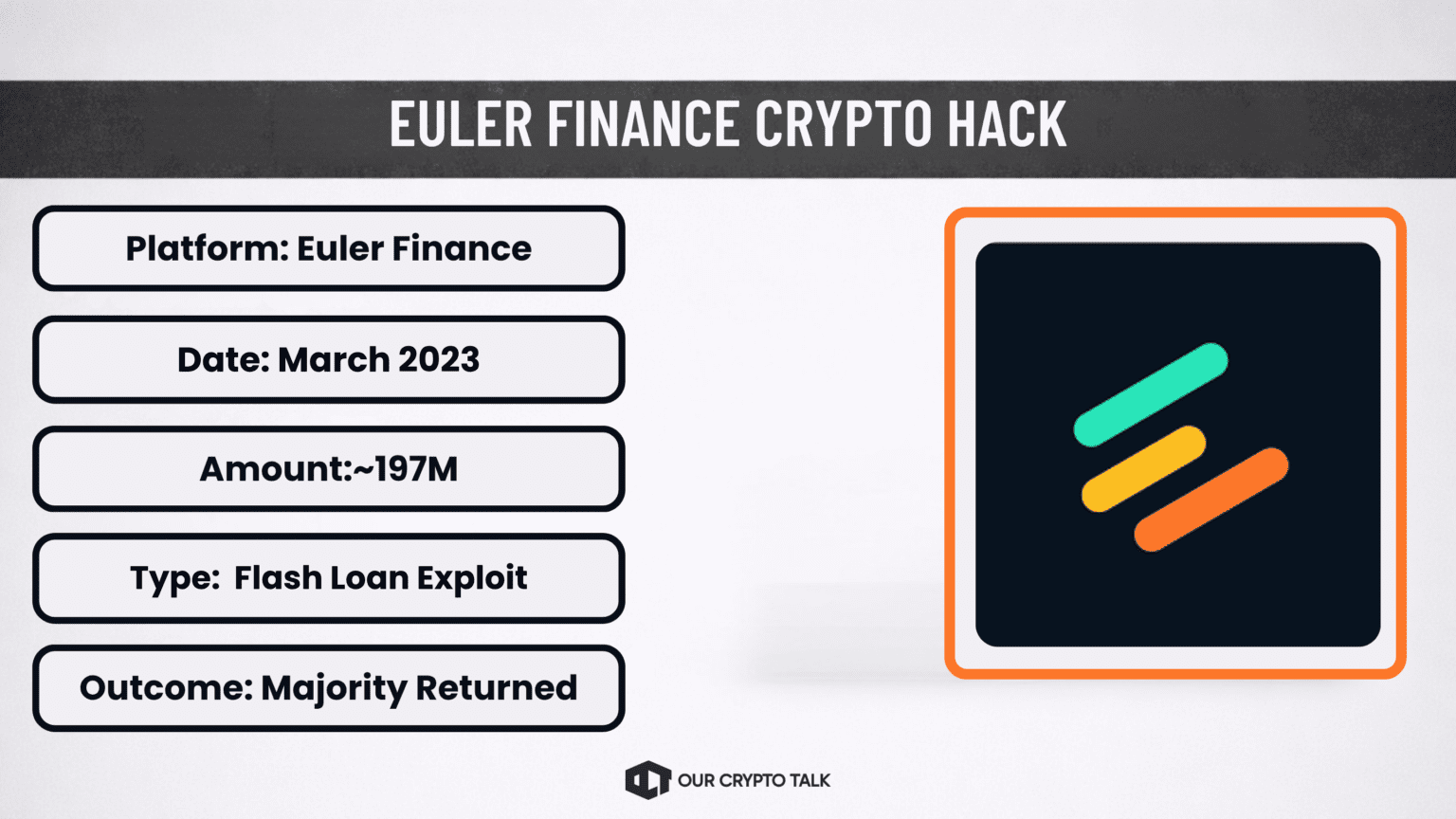
A complex flash-loan exploit targeted lending mechanics and accounting logic in a DeFi protocol. Most funds were eventually returned, but the exploit reminded the market that composability itself can function as an attack surface. Euler stood apart from some of the exchange and bridge hacks because it reflected a more purely DeFi-native category of risk. The protocol did not fail because a custodian lost keys or because a centralized operator mismanaged treasury controls. Instead, the exploit emerged from the interaction of financial logic, liquidity mechanics, and protocol design.
Combined, these incidents exceed six billion dollars in losses. That total is not just a dramatic number. It is evidence. It shows the scale of capital that has repeatedly sat inside systems vulnerable to concentrated points of failure, whether those points were exchange wallets, validator sets, bridge contracts, cloud systems, or treasury workflows.
The Complete Timeline : Every Crypto Hack Over $100M
The crypto industry prefers to talk about crypto hacks as if each one belongs to its own category.
Mt. Gox was an early-stage chaos. Bitfinex was a custody failure. Coincheck was poor wallet hygiene. Ronin was a bridge issue. The wormhole was a verification flaw. FTX was fraud plus opportunistic wallet movement. Bybit was an operational workflow compromise.
Set the jargon aside and the historical line starts to look much simpler. Mt. Gox. Bitfinex. Coincheck. FTX. Bybit. Five different exchanges. Five different moments in the market. Same basic problem: a large amount of user capital sat inside a system that required trusting a relatively narrow set of people, processes, or keys.
That is not an incidental detail. It is the center of the story.
Mt. Gox remains the foundational case. At its peak, it handled the majority of global Bitcoin trading volume. That kind of market share meant one platform had become a de facto systemically important institution inside an ecosystem supposedly designed to avoid exactly that outcome.
The industry repeated the mistake anyway.
Bitfinex arrived later, in a more security-aware era. It used more advanced structures than the earliest exchanges. The response to its 2016 breach helped push multisignature custody into the mainstream. That reform mattered. It also encouraged a familiar and dangerous form of confidence. The market started to believe that the last disaster had finally taught the right lesson in the right way.
Then Coincheck got hit in 2018.
Again, the specifics differed. The platform stored large amounts of NEM in a hot wallet, prioritizing trading and withdrawal convenience. Attackers exploited that choice. The numbers were enormous. Users were reimbursed. Regulators tightened standards.
Then came Bybit.
This is where the pattern became harder to wave away. Bybit did not represent the sloppy frontier era. It did not fit the “those were the early days” excuse. It arrived after years of lessons, reforms, audits, security theater, and operational hardening. Yet the breach still revolved around concentrated treasury control and the manipulability of a system that users ultimately had to trust rather than verify for themselves.
The history of major crypto hacks does not read like a straight line of progress. It reads like a cycle.
A large breach shocks the market. Security teams promise upgrades. Founders talk about lessons learned. Regulators discover urgency. New controls appear. Confidence slowly returns. Then the next breach lands through a different vector and exposes the limits of the previous round of reforms. That rhythm matters because it explains why the industry can honestly claim it has improved and still honestly admit it remains vulnerable. Both things are true.
The first era centered on the crude but foundational problem of custodial trust.
Mt. Gox shattered the assumption that a dominant exchange could securely manage user funds simply because it had become large enough to matter. Its collapse changed the language of the industry. Cold storage became a mainstream expectation rather than an optional best practice. Specialized custody providers began to emerge. Users became more conscious of counterparty risk. The market absorbed a brutal education in what happens when a centralized exchange quietly becomes too important to fail and then fails anyway.
For a while, the lesson seemed to stick. Then the market rediscovered how sticky convenience is.
Bitfinex’s 2016 breach pushed exchanges toward more advanced wallet architectures, especially multisignature custody. That was a genuine step forward. Firms also began discussing insurance mechanisms and internal risk segregation more seriously. The post-Bitfinex period created a sense, particularly among sophisticated traders, that the industry had finally moved beyond the most primitive forms of custodial vulnerability.
Then Coincheck punctured that confidence. The problem was not that nobody knew hot wallets were risky. The problem was that exchanges still needed them. Users wanted fast withdrawals and seamless market access. Platforms wanted liquidity and frictionless operations. Security always had to negotiate with product design and trading reality. Coincheck showed that the old trade-off had not disappeared. It had simply been managed, rationalized, and eventually exposed again.
The next era did not eliminate exchange risk. It professionalized it.
As crypto entered a more institutional phase, large venues and service providers started to resemble conventional financial infrastructure. They talked in the language of compliance, governance, and internal controls, implemented layered approval systems. They hired security experts and worked with custodians, auditors, and legal teams. The optics of maturity improved dramatically.
That progress was not fake. It just was not enough.
The deeper issue is that institutionalization often changes the form of risk rather than removing it. A single vulnerable hot wallet may give way to a more elaborate treasury workflow. A lone administrator may give way to multiple signers. Informal operations may give way to better procedures. However, every new layer can introduce new assumptions, new dependencies, and new places where a compromise can become catastrophic.
The industry often mistakes process complexity for security strength. Sometimes the two align. Sometimes complexity only creates more opaque failure paths.
FTX crystallized the limits of maturity theater. It looked sophisticated from the outside. It marketed itself as a serious institution and built political connections, public credibility, and an aura of inevitability. Yet the collapse revealed how little those signals matter if governance is weak and control over user assets remains opaque. Proof-of-reserves campaigns emerged afterward because the market desperately needed visible reassurance. But those campaigns also showed the narrowness of the response. The industry tried to answer a deep governance crisis with a solvency-signaling tool.
That is typical of the post-hack cycle. The market addresses the most visible layer of the last failure. The next failure arrives through a less visible one.
If early crypto hacks revolved around exchanges, the next wave moved into infrastructure sold as more decentralized.
However, bridge-related crypto hacks exposed concentrated validator authority and verification risks. Ronin and Wormhole losses reached unprecedented levels. Developers expanded validator sets and increased audit frequency. Nevertheless, performance requirements often outweighed strict decentralization.
Ronin showed what happens when a bridge operates with too little validator decentralization relative to the value it secures. Compromise enough keys and the whole system becomes a cash dispenser. Wormhole showed that even when a design looks more distributed, verification assumptions can still create concentrated trust in practice. Poly Network revealed how cross-chain logic can become its own attack surface. Euler, meanwhile, illustrated how purely onchain financial machinery can be manipulated through complexity itself.
The reforms after these incidents were predictable and, in many cases, sensible. More audits. Larger bug bounties. Better monitoring. Expanded validator sets. Withdrawal limits. Emergency pause systems. Formal verification discussions. Economic stress testing.
All of that helped.
None of it changed the fact that the market kept rewarding speed, interoperability, capital efficiency, and user experience, often faster than security models could mature. The result was not negligence so much as structural pressure. If one protocol slows down to harden every edge case, a rival ships faster and captures users. If one bridge decentralizes aggressively and sacrifices convenience, another offers smoother UX and wins volume. Security teams work against not just attackers but incentives.
The most recent era brings the pattern into sharper focus. Crypto now manages larger pools of capital with more sophisticated tooling than ever before. Hardware-backed signing systems, treasury orchestration, external custody integrations, layered permissions, monitoring dashboards, and institutional workflows all reflect real progress.
They also create the conditions for a different kind of breach.
Attackers no longer need to find a naive exchange with poor wallet hygiene. Increasingly, they target the seams between systems. The approval interface. The supply chain dependency. The communication channel. The software component that tells a signer what they are authorizing. Bybit became the defining case of this era because it illustrated how a highly evolved custody stack can still fail if the operational pathway to authorization becomes compromised.
That is why “what changed after each hack” always has the same unsatisfying answer. Some things changed. Important things. Yet the structural tension remained intact.
So after each breach, the industry improves the system it already has rather than asking whether the system itself keeps creating the same outcome.
The timeline of major crypto hacks highlights a persistent theme. Users lose funds when third parties control private keys.
This is the part of the argument that many in the industry resist, often for understandable reasons. Self-custody is not easy for everyone. It is not ideal for every workflow, does not eliminate risk. It can be unforgiving. People lose seed phrases. They fall for phishing attacks, sign malicious transactions. They make operational mistakes with no customer support line waiting to reverse them.All of that is true.
It is also true that the historical record keeps pointing in the same direction: the most devastating, system-wide losses tend to occur when users hand asset control to someone else.That does not make self-custody a moral virtue. It makes it a risk architecture.
When a centralized exchange, bridge treasury, or custodial service gets compromised, the blast radius can engulf hundreds of thousands or millions of users at once. The attacker only needs one successful path into the right pool of capital. When an individual self-custodied wallet is compromised, the loss is usually local. Painful, sometimes ruinous for the owner, but not systemic.
That difference matters.
The phrase “not your keys, not your coins” became famous after Mt. Gox because it captured something more than ideology. It captured concentration risk in a single sentence. If someone else controls the keys, then your claim on the asset depends on their solvency, their integrity, their security practices, their internal controls, and their luck. You may have economic exposure, but you do not have direct control. In calm markets, that distinction can feel abstract. In a crisis, it becomes immediate.
The history of major crypto hacks is not just a history of stolen money. It is a history of broken narratives.
After every major breach, the industry says some version of the same thing. This was serious. Lessons have been learned. Security will improve. Trust will be rebuilt. In fairness, trust often is rebuilt. Systems improve. Controls get stronger. The sector becomes more sophisticated. Yet the next large-scale failure keeps revealing an older truth beneath the newer infrastructure. Crypto has not escaped institutional trust. It has been rebuilt in new forms.
That does not mean the entire project has failed. Blockchains themselves have proven remarkably durable. Consensus systems do not usually implode under pressure. Public ledgers do what they are supposed to do with impressive regularity. The fragility appears elsewhere, in the businesses, bridge models, custody stacks, governance systems, and operational processes layered around those ledgers.
In that sense, crypto’s hacking problem looks less like a flaw in decentralized technology and more like a consequence of how markets organize around it. Capital gathers. Intermediaries emerge. Convenience wins market share. Concentration follows. Attackers notice. Bybit did not invent that pattern. It simply made it impossible to ignore at a new scale.
So the lesson from the last decade is not that crypto is uniquely doomed or uniquely unsafe. Traditional finance has its own disasters, its own frauds, its own operational failures, and its own concentrations of risk. The lesson is narrower and more actionable. Whenever crypto recreates concentrated trust in pursuit of growth, efficiency, or convenience, it recreates the conditions for its largest disasters. That is the pattern. Not every hack. Not every exploit. But the biggest ones, again and again.


Best Web3 Privacy Wallets 2026: Guide to Storing Crypto Privately
How to Actually Lock In on CT (While 90% Stay Broke)
Crypto Privacy in 2026: Tech, Tools & Regulation Guide
Yuma Consensus Explained: The Algorithm Behind Bittensor
Best Web3 Privacy Wallets 2026: Guide to Storing Crypto Privately
How to Actually Lock In on CT (While 90% Stay Broke)
Crypto Privacy in 2026: Tech, Tools & Regulation Guide
Yuma Consensus Explained: The Algorithm Behind Bittensor