Zama Review
Zama Review: A confidentiality layer using FHE to enable encrypted smart contracts and private data on public blockchains.
Author: Akshat Thakur
Introduction
Public blockchains have a problem the industry still underestimates. Everything is visible by default. That design made sense in the early days. Transparency helped prove that systems were working as intended. But once real-world use cases enter the picture, the model starts to break. Financial activity, identity data, and business operations are not meant to be exposed to everyone.
This is one of the biggest reasons institutions have not fully moved onchain. It is not about ideology. It is about practicality. No serious financial system runs on fully public data, and expecting blockchains to work that way at scale is unrealistic. Most attempts to solve this problem fall into two camps. Either you move to private chains and lose interoperability, or you add partial privacy features that do not fully solve the issue. Neither approach has unlocked real adoption.
Zama takes a more direct path. Instead of compromising between transparency and privacy, it tries to remove the tradeoff entirely. The protocol allows smart contracts to compute on encrypted data while still remaining verifiable. That sounds like a small change, but it is not. If it works at scale, it changes what blockchains can actually be used for.
This Zama review looks at how that system works, why Fully Homomorphic Encryption is central to the design, and whether this approach can realistically move blockchain from experimental infrastructure to something institutions can actually use.
Problem Statement
- Lack of Confidentiality in Public Blockchains: Public blockchains are designed for transparency, where every transaction and state change is visible to all participants. While this ensures verifiability, it creates a major limitation sensitive data such as balances, identities, and financial activity cannot remain private. This makes blockchains unsuitable for many real-world use cases like finance, identity, and enterprise operations.
- Trade-Off Between Privacy and Verifiability: Existing systems struggle to balance privacy with trustlessness. Keeping data private often requires sacrificing verifiability or relying on trusted parties, while fully transparent systems expose all user data. This creates a fundamental contradiction where blockchains cannot simultaneously guarantee correctness and confidentiality at scale.
- Limitations of Existing Confidentiality Technologies: Current approaches like MPC, ZK proofs, and TEEs each solve parts of the privacy problem but introduce trade-offs. MPC can be communication-heavy, ZK can be complex and costly, and TEEs rely on hardware trust assumptions. No single solution provides a complete, scalable, and developer-friendly framework for confidential computation onchain.
- Complexity of Building Confidential Applications: Developing privacy-preserving applications today requires specialized cryptographic knowledge, custom tooling, and unfamiliar programming environments. This significantly increases development complexity and limits adoption, preventing most developers from building confidential smart contracts at scale.
Solutions Provided by Zama
- End-to-End Confidential Smart Contracts: Zama introduces a confidentiality layer that enables smart contracts to operate on encrypted data. Using Fully Homomorphic Encryption (FHE), all inputs, states, and computations remain encrypted throughout execution, ensuring that sensitive data is never exposed even to node operators while still maintaining public verifiability.
- Combining Privacy with Verifiability: The protocol resolves the privacy-verifiability trade-off by allowing computations on encrypted data that can still be independently verified. Anyone can validate that operations were executed correctly without accessing the underlying data, enabling trustless systems without sacrificing confidentiality.
- Hybrid Cryptographic Architecture: Zama combines FHE, MPC, and Zero-Knowledge proofs into a unified system where each component handles a specific role. FHE enables encrypted computation, MPC secures key management and decryption, and ZK ensures correctness of inputs. This modular approach avoids the limitations of relying on a single privacy technology while improving scalability and security.
- Developer-Friendly Confidential Infrastructure: Through the FHEVM library, Zama allows developers to build confidential applications using familiar languages like Solidity without needing deep cryptographic expertise. Developers can define access control rules directly within smart contracts, making confidentiality programmable and significantly lowering the barrier to building privacy-preserving applications.
Problem–Solution Overview
Technology & Architecture
Technology & Architecture
Confidential Computation Stack
Multi-Technology Security Model
Layered Architecture Design
Market Performance
📊 Market Performance
Tokenomics
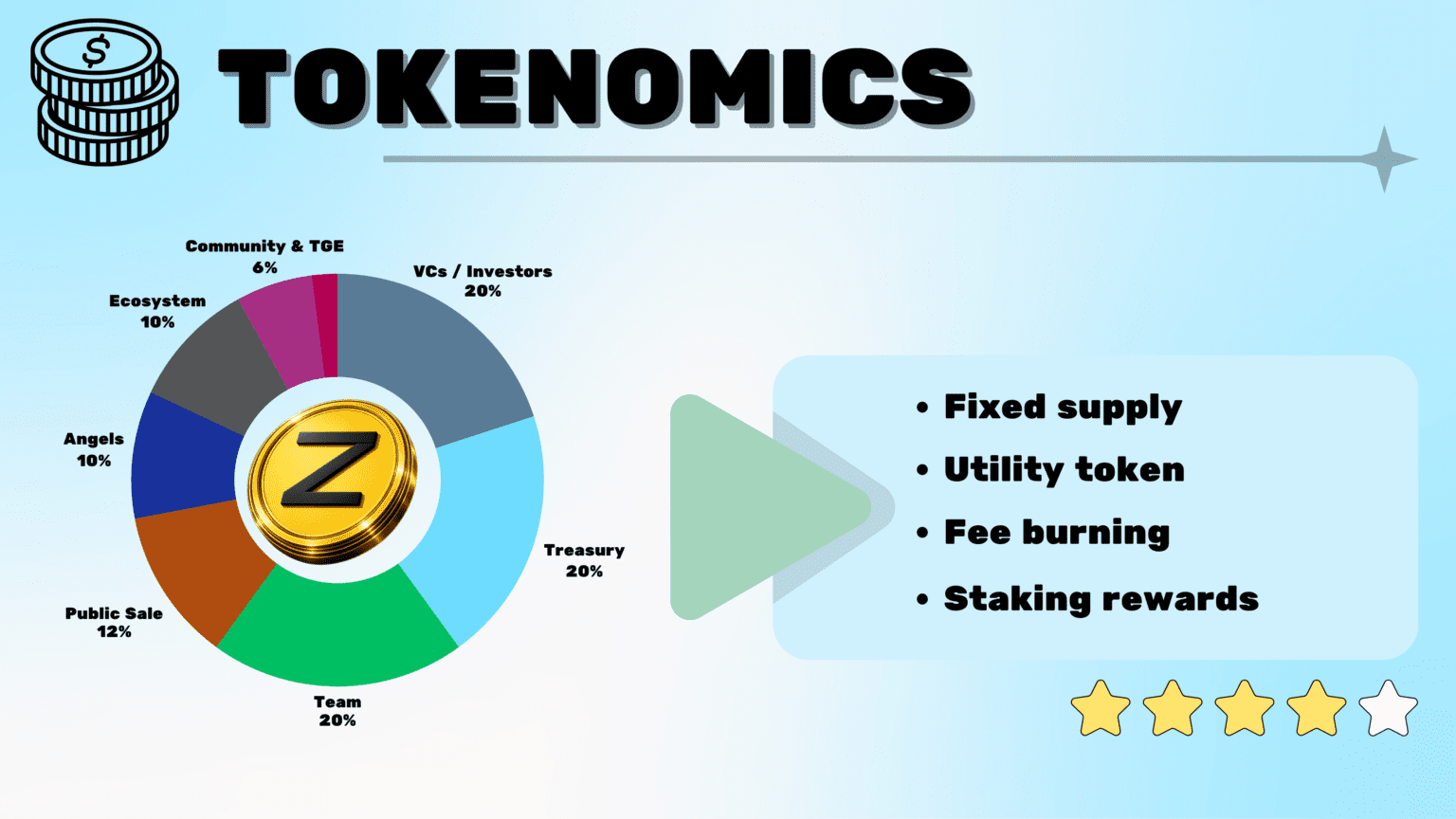
Zama introduces the ZAMA token as the utility and economic coordination asset of the Zama ecosystem. The protocol operates on a Fully Homomorphic Encryption (FHE)-powered confidential blockchain environment, enabling privacy-preserving smart contracts, computations, and applications while aligning incentives with long-term protocol growth, network security, and confidential DeFi/RWA expansion.
Token Overview
- Symbol: ZAMA
- Total Supply: 11,000,000,000 ZAMA (initial fixed supply; subject to burn-and-mint mechanics for operator rewards)
- Standard: ERC-20 (Ethereum-compatible)
- Decimals: 18
The ZAMA token functions as the utility, fee payment, staking, and reward asset of the Zama protocol. It enables payment of confidentiality fees (100% burned), staking for network operators (FHE and KMS nodes), rewards via minted inflation, and long-term ecosystem participation.
Token Allocation
- Public Sale (Sealed-Bid Dutch Auction + Community Sale): 12% (Fully unlocked at TGE on February 2, 2026).
- Community & TGE Campaigns: 6% (Primarily unlocked at TGE for early user incentives).
- Growth & Ecosystem: 10% (Reserved for partnerships, development, and adoption programs).
- Angels & Early Contributors: 10% (Vesting with 1-year cliff + linear release).
- VCs / Investors: 20% (Vesting with 1-year cliff + 2–3 year linear release).
- Treasury: 20% (Allocated for protocol sustainability and strategic initiatives, with staged unlocks).
- Team: 20% (4-year linear vesting with 1-year cliff).
- Liquidity: 2% (Allocated for exchange liquidity and market making).
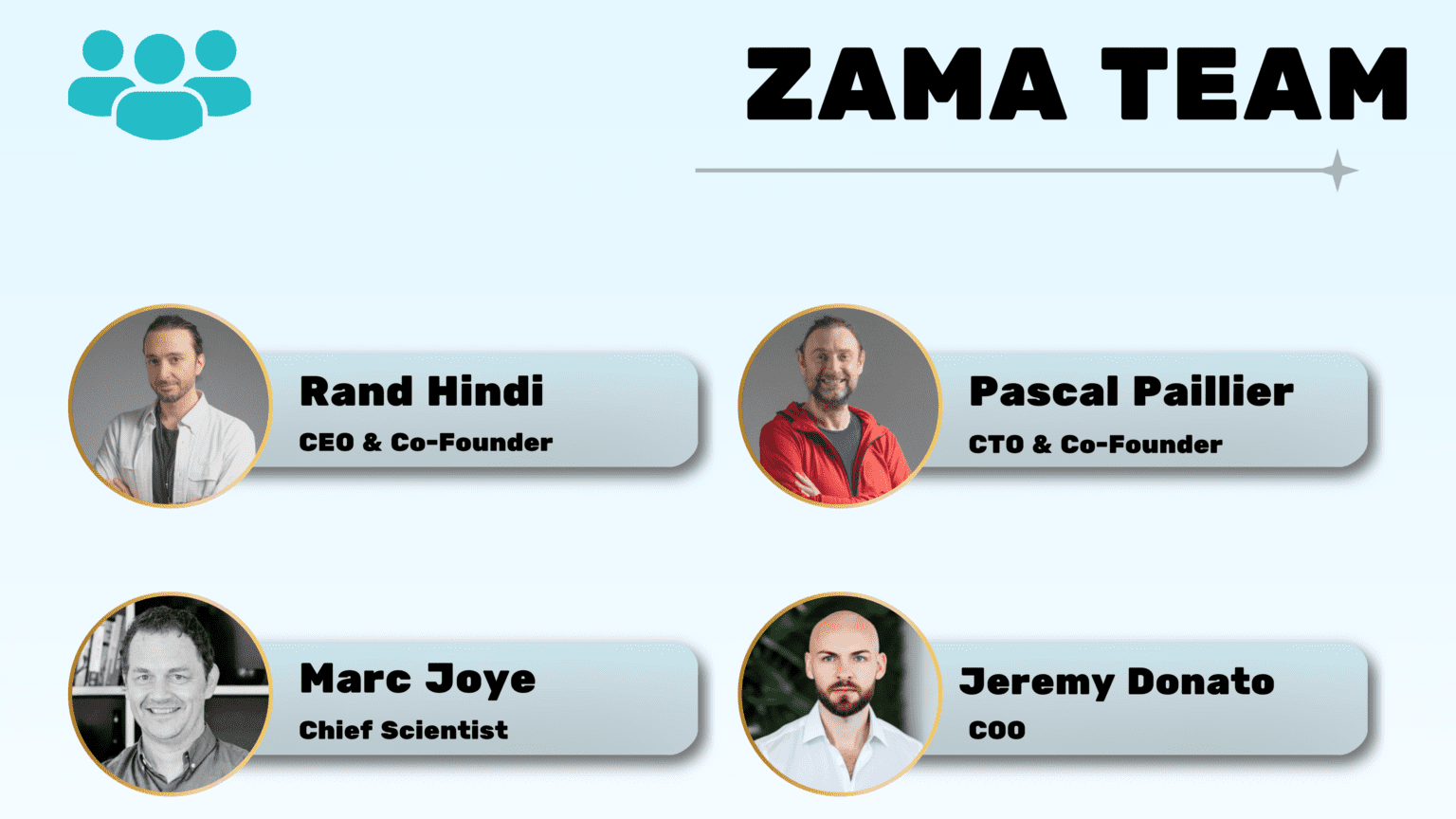
Team & Background
Zama is a research-driven company focused on cryptography and FHE. The team includes well-known researchers and has raised significant funding from major crypto investors.
It was founded in 2020 by:
- Dr Rand Hindi: CEO
- Dr Pascal Paillier: CTO
- Prof Nigel Smart: Chief Academic Officer
- Dr Marc Joye: Chief Scientist
Project Analysis
Zama is one of the few projects tackling a problem that actually matters for real-world adoption. Most crypto projects focus on improving speed or reducing costs. Zama focuses on something more fundamental, making blockchains usable for sensitive data.
Strengths
- Strong focus on a real adoption bottleneck, confidentiality
- Advanced use of FHE with significant performance improvements
- Flexible design with programmable privacy
- Cross-chain approach avoids ecosystem fragmentation
- Strong research team and technical credibility
Challenges
- FHE is still complex and difficult to scale
- Adoption depends heavily on developer understanding
- Competes with simpler privacy solutions
- Performance improvements are critical to long-term success
Zama vs Confidential Computing & Privacy Protocols
| Project | Core Focus | Execution Architecture | Programmability | Token Utility | Notes |
|---|---|---|---|---|---|
|
| FHE-based confidentiality layer for any blockchain | FHEVM with decentralized operators and coprocessors integrating into existing L1 and L2 chains | Full (fhEVM encrypted smart contracts) | Fees burned, staking via DPoS, governance, rewards minted | Mainnet launched Dec 2025; ZAMA token launched Feb 2026 as ERC-20; burn-and-mint model; enables confidential DeFi and AI across Ethereum, Solana, and BSC |
|
| Privacy-first programmable Layer-1 blockchain | Off-chain execution with on-chain zk-SNARK verification | Full (Leo language) | Fees, staking, prover rewards | Default private execution model; mainnet live since 2023; selective disclosure enabled via view keys |
|
| Private smart contract Layer-2 on Ethereum | Off-chain execution with on-chain rollup verification | Full (Noir language) | Layer-2 fees, staking and governance via AZTEC | End-to-end private execution environment; strong UX; dependent on Ethereum for settlement and security |
|
| Confidential smart contract platform | On-chain execution using trusted execution environments | Full (CosmWasm) | Fees, staking, governance | Relies on TEE-based privacy rather than pure cryptography; added AI infrastructure; live mainnet |
|
| Decentralized confidential computing network | Hybrid MPC, homomorphic encryption, and zero-knowledge architecture | Full (Python and JavaScript SDKs) | Fees, staking, governance | Enables blind computation for data and AI; not a traditional blockchain; strong enterprise positioning |
|
| Fully homomorphic encryption Layer-2 for confidential applications | FHE-based rollup deployed on Ethereum | Full (EVM-compatible) | Fees, staking (INCO) | Pure FHE execution environment; similar design philosophy to Zama but operates as standalone Layer-2 |
|
| Private DeFi and liquidity infrastructure on Cosmos | Shielded transactions with zero-knowledge proofs | Full (CosmWasm) | Fees, staking (UM) | Private DEX and liquidity layer; mainnet live; integrated with Cosmos IBC for cross-chain privacy |
Conclusion
Zama is trying to solve a problem that most of the industry has avoided for years. Public blockchains are transparent by design, but real-world systems are not. That mismatch is one of the main reasons adoption has been slower than expected.
The protocol’s approach is clear. Keep verifiability, but remove the requirement to expose data. Fully Homomorphic Encryption makes that possible in theory, and Zama is one of the few teams pushing it toward practical use.
If this model works, the implications are significant. Financial systems could move onchain without exposing sensitive data. Identity systems could become composable without sacrificing privacy. Entire applications that currently rely on centralized infrastructure could operate in a decentralized environment.
But the gap between theory and adoption is still real. FHE is powerful, but it comes with complexity and performance challenges. Developers need to understand new primitives, and the system needs to prove it can scale under real demand.
That is where Zama stands today. The direction makes sense, and the technology is credible. The open question is whether the ecosystem is ready to build on top of it.
TL;DR
- Confidential computing layer designed for public blockchains.
- Built using Fully Homomorphic Encryption for encrypted computation.
- Enables smart contracts with programmable privacy and secure execution.
- Cross-chain architecture rather than a standalone Layer 1 or Layer 2.
- Combines FHE, MPC, and zero-knowledge proofs for verification.
- Focused on finance, identity, and governance use cases.
In this article
IntroductionProblem StatementSolutions Provided by ZamaProblem–Solution OverviewTechnology & ArchitectureMarket PerformanceTokenomicsTeam & BackgroundProject AnalysisConclusion