Midnight Review
Midnight Review: A privacy-first Layer-1 enabling selective disclosure, zero-knowledge apps, and compliance-ready infrastructure.
Author: Akshat Thakur
Introduction
Midnight is a privacy-first blockchain purpose-built to enable confidential smart contracts and selective data disclosure for real-world applications. This Midnight Review examines how the protocol is designed to reconcile decentralization with regulatory, enterprise, and user privacy requirements by embedding zero-knowledge cryptography directly into its execution model. Rather than exposing all transaction data by default, Midnight enables applications to operate with privacy as a foundational property.
The network is built to serve developers, application operators, and enterprises that require confidentiality guarantees while still benefiting from decentralization. Midnight introduces a zero-knowledge based architecture that shields sensitive data and metadata, while still enabling verifiable computation and on-chain settlement. This approach allows organizations to build applications without collecting excessive user data or exposing proprietary business intelligence.
As detailed throughout this Midnight Review, the protocol is positioned to support regulated finance, identity systems, and enterprise workflows that require both verifiability and confidentiality. By designing privacy into the base layer instead of adding it as an overlay, Midnight aims to expand blockchain adoption beyond environments where full transparency is acceptable.
Problem Statement
- Public Blockchains Expose Sensitive Business and User Data by Default: Most blockchains make transaction details, balances, and application state publicly visible. This design makes them unsuitable for real-world use cases such as regulated finance, identity systems, healthcare workflows, or enterprise coordination, where confidentiality is legally and commercially required.
- Lack of Selective Disclosure Limits Regulatory Adoption: Existing privacy solutions often rely on full obfuscation or off-chain trust assumptions. Regulators, auditors, and counterparties are unable to verify compliance without breaking privacy, creating friction between decentralization and real-world regulatory frameworks.
- Smart Contracts Cannot Safely Handle Confidential Inputs: Traditional smart contract environments are not designed to process private data. Developers must avoid sensitive inputs or rely on external systems, which weakens security guarantees and limits the complexity of applications that can be built.
- Governance and Incentives Leak Participation Data: Voting, staking, and incentive mechanisms typically reveal user behavior and holdings. This discourages participation from institutions and individuals who require confidentiality in decision-making and capital allocation.
- Privacy Tooling Increases Complexity for Developers and Users: Privacy layers added on top of public chains introduce complex workflows, fragmented tooling, and poor user experience. This raises development costs and slows adoption, especially outside crypto-native audiences.
Solutions Provided by Midnight
- Zero-Knowledge–Based Confidential Execution Environment: Midnight integrates zero-knowledge proofs at the protocol level, allowing smart contracts to process sensitive inputs while proving correctness on-chain. This enables applications to use private data without exposing it to validators or the public.
- Native Selective Disclosure for Compliance and Auditability: Midnight allows users to selectively reveal specific information to authorized parties such as regulators or auditors. This preserves privacy by default while supporting verification when legally or operationally required.
- Private Smart Contracts With On-Chain Verification: Midnight enables contracts to operate on encrypted state while generating proofs that validators can verify deterministically. This ensures confidentiality without sacrificing consensus integrity or trustless execution.
- Confidential Governance and Incentive Mechanisms: Voting, rewards, and participation data can remain private while still being provably correct. This design supports institutional-grade governance models without exposing strategic or financial information.
- Developer-Friendly Privacy Abstractions: Midnight abstracts cryptographic complexity behind protocol-level primitives. Developers can build compliant, privacy-preserving applications without designing custom cryptographic systems or managing fragmented privacy tooling.
Problem–Solution Overview
Midnight Review: Technology and Architecture
Technology & Architecture
Privacy-Preserving Smart Contracts
Zero-Knowledge Proof System
Interoperability & Partner Chains
Midnight Review: Tokenomics
- Type: Native Token, Governance Token, Unshielded Asset.
- Parent Network: Midnight Network (Layer 1, Cardano Partner Chain).
- Native Standards: Midnight Native Token, Cardano Native Asset (CNA)
- Component Relationship: NIGHT (Generator, Token) -> produces -> DUST (Resource).
- Consensus Role: Sybil resistance mechanism, Validator Reward.
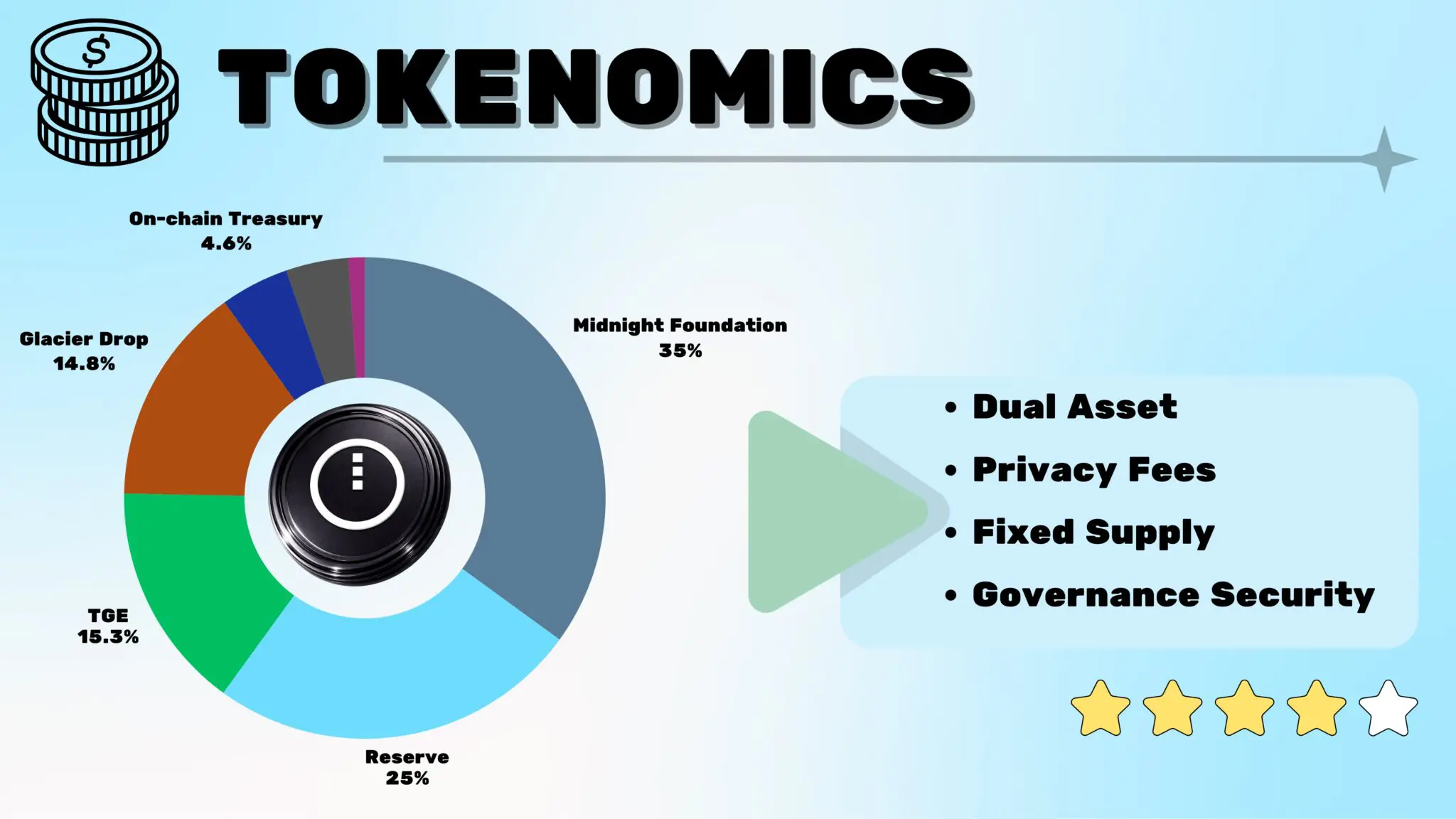
Midnight introduces a dual-asset model designed to balance security, usability, and regulatory considerations.
NIGHT is an unshielded token with a fixed supply and deflationary policy. It is used for network governance, consensus participation, and block production rewards. Initially, NIGHT exists as a Cardano native asset, leveraging Cardano’s infrastructure during early network phases.
DUST is a shielded, non-transferable capacity resource used to power transactions on the Midnight network. It functions as transaction fuel while protecting metadata and preventing transaction correlation. DUST decays over time and is replenished proportionally through NIGHT holdings, enabling predictable and stable fee dynamics.
This separation allows Midnight to maintain fee predictability, regulatory compatibility, and privacy-preserving transaction execution.
Distribution Metrics
- Total Supply: 24,000,000,000 (24 Billion).
- Glacier Drop (Phase 1): 3.5 Billion claimed; 170k addresses.
- Scavenger Mine (Phase 2): 1 Billion claimed; 8M addresses.
- Collection & Lost-and-Found (Phase 3): Claims ongoing, exchange-facilitated distributions
- Thawing Period: 450 Days (Quarterly).
Market Performance
📊 Market Performance
Team
Midnight is supported by a development and research team focused on cryptography, privacy engineering, and enterprise-grade blockchain infrastructure. While the project benefits from the broader Cardano ecosystem and Input Output research lineage, the Midnight team is not fully doxxed, which is common for privacy-focused protocols operating in early stages.
Midnight Review Analysis
Comparative Overview
Compared to general-purpose public blockchains, Midnight offers native data and metadata protection. Relative to privacy coins with limited programmability, Midnight supports full application logic with selective disclosure. Against other ZK platforms, Midnight prioritizes developer accessibility and compliance-ready design.
Strengths
- Programmable data protection with selective disclosure
- Developer-friendly TypeScript-based tooling
- Predictable fee model through dual-token design
- Strong interoperability roadmap
Challenges
- Complexity of privacy-focused application design
- Early-stage ecosystem maturity
- Gradual rollout of advanced consensus features
Midnight vs Privacy-Focused Layer-1 & ZK Platforms
| Project | Core Focus | Privacy Model | Execution Architecture | Programmability | Token Utility | Notes |
|---|---|---|---|---|---|---|
Midnight | Programmable privacy for decentralized applications as a partner chain to Cardano. | Rational privacy with selective disclosure using zk-SNARKs and dual public/private states. | Off-chain computation with on-chain zk-SNARK verification using recursive proofs. | Full smart contract support via Compact (TypeScript-based). | Governance, utility (generate DUST for private transactions), fees, and staking. | Fourth-generation privacy blockchain with a dual-token model using DUST for confidential transactions; mainnet launched Dec 2025; enables compliant DeFi and data protection; built by IOG. |
Aleo | Privacy-first general-purpose Layer-1 with emphasis on compliant payments. | Default private using encrypted records and zero-knowledge proofs; selective disclosure via view keys. | Off-chain execution with on-chain verification using zk-SNARKs (SnarkVM, SnarkOS). | Full smart contracts via the Leo programming language. | Fees, program execution costs, prover and validator rewards, staking. | Layer-1 built around programmable private computation; mainnet live since 2023; partnerships for private stablecoins such as USDCx. |

Zcash | Private payments focused on confidential transfers. | Optional shielded transactions. | Fully on-chain execution with zk-SNARK validation. | None (no smart contract support). | Transaction fees and miner rewards. | Best-in-class private transfers; not suitable for general-purpose apps; Proof-of-Work consensus. |
Ethereum | General-purpose smart contracts supporting DeFi, NFTs, RWAs, and stablecoins. | Public by default; privacy typically achieved through L2s, mixers, or application-level cryptography. | Fully on-chain execution with rollup-based scaling. | Full programmability using Solidity and Vyper. | Gas fees, staking, and validator rewards. | Dominant ecosystem and liquidity hub; privacy is not native and requires additional layers or cryptographic tooling. |
Aztec | Privacy-preserving smart contracts and applications built as an Ethereum Layer-2. | Default private rollup with end-to-end encrypted transactions. | Off-chain execution with on-chain rollup proof verification. | Full programmability using Noir for zk circuits. | Layer-2 fees plus AZTEC token for staking, governance, and delegation. | Strong privacy UX but dependent on Ethereum; token sale completed in 2025 with TGE expected in 2026; bridges for cross-chain privacy planned. |
Mina Protocol | Succinct verification platform enabling lightweight, secure decentralized applications. | Programmable privacy via zkApps; data stays local while proofs are verified on-chain. | Recursive zk proofs keep chain size small; primary computation happens off-chain. | Full programmability via zkApps in a TypeScript-based language (Turing-complete). | Fees and staking rewards. | Excellent for lightweight verification and private stateful apps; fixed ~22KB chain size; testnet updates continued through 2025. |
Secret Network | Confidential smart contracts for privacy-preserving applications. | Encrypted contract state secured via trusted execution environments (TEEs). | On-chain execution inside trusted hardware. | Full programmability via CosmWasm. | Fees, staking, and governance participation. | Relies on TEEs rather than pure cryptography; expanded into AI infrastructure in 2025. |
Midnight Review Conclusion
This Midnight Review presents a protocol that approaches blockchain design from a fundamentally different angle than performance-first or DeFi-centric networks. Midnight is not optimized for raw throughput or speculative activity, but for enabling regulated, real-world interactions where data privacy, selective disclosure, and compliance are non-negotiable. By embedding zero-knowledge proofs directly into its execution and governance model, Midnight creates a foundation where sensitive information can be used, verified, and audited without being exposed on a public ledger.
What makes Midnight particularly notable is its alignment with existing economic and legal realities. Rather than framing privacy as an adversarial feature, the protocol treats it as a cooperative one designed to work alongside regulators, enterprises, and institutions that require transparency under defined conditions. This design choice positions Midnight as a bridge between decentralized systems and real-world adoption, especially in domains such as identity, finance, healthcare, and enterprise data coordination.
As this Midnight Review concludes, the project’s long-term success will depend less on market cycles and more on execution: developer adoption, clarity of incentives, and the maturity of its privacy-preserving tooling. If Midnight can continue translating its cryptographic foundations into usable applications and trusted infrastructure, it stands to become a critical layer for compliant, privacy-first Web3 systems rather than just another experimental blockchain.

TL;DR
- Privacy-preserving Layer-1 for protected data applications.
- Zero-knowledge proofs enable selective disclosure.
- TypeScript-based smart contract development.
- Dual-token model separates fuel and governance.
- Compliance-ready enterprise use cases are the focus.
- Interoperable design anchored to the Cardano ecosystem.
In this article
IntroductionProblem StatementSolutions Provided by MidnightProblem–Solution OverviewMidnight Review: TokenomicsMarket PerformanceTeamMidnight Review AnalysisMidnight vs Privacy-Focused Layer-1 & ZK PlatformsMidnight Review Conclusion