TrustedVolumes, a major market maker and resolver in the 1inch ecosystem, lost approximately $5.87 million in an ongoing Ethereum exploit
Author: Sahil Thakur
7th May 2026 – TrustedVolumes, a major market maker and resolver in the 1inch ecosystem, lost approximately $5.87 million in an ongoing Ethereum exploit detected by on-chain security firm Blockaid.
High Signal Summary For A Quick Glance
Tyler Simpson
@quantumvoidlabs
@blockaid_ @trustedvolumes Can someone turn the rug adapter off on this version of the simulation thanks
🚨 Blockaid's exploit detection system has identified an on-going exploit on TrustedVolumes (1inch market maker / resolver, @trustedvolumes ). Chain: Ethereum Victim contract: TrustedVolumes resolver — 0x9bA0CF1588E1DFA905eC948F7FE5104dD40EDa31 Exploiter:
03:09 AM·May 7, 2026
PeckShieldAlert
@PeckShieldAlert
#PeckShieldAlert @trustedvolumes has been exploited for ~$5.9M, including $3.02M $ETH,$1.37M $WBTC & 1.47M stablecoins, the exploiter has swapped the stolen funds for 2.513K $ETH https://t.co/HZ1LGlZJcC
02:17 AM·May 7, 2026
electronixguru Win
@ElectronixGuru
@blockaid_ @trustedvolumes The szn of exploits
🚨 Blockaid's exploit detection system has identified an on-going exploit on TrustedVolumes (1inch market maker / resolver, @trustedvolumes ). Chain: Ethereum Victim contract: TrustedVolumes resolver — 0x9bA0CF1588E1DFA905eC948F7FE5104dD40EDa31 Exploiter:
01:51 AM·May 7, 2026
Steady attention without excessive speculation.
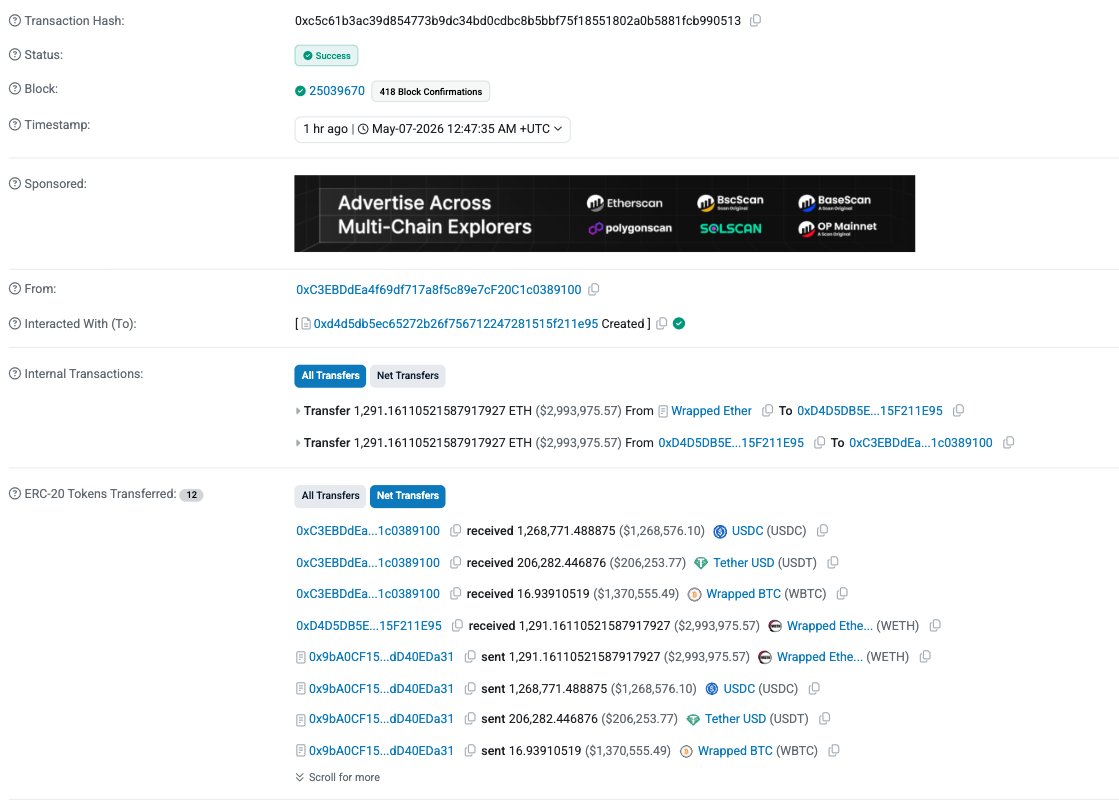
The attacker drained 1,291.16 WETH, 206,282 USDT, 16.939 WBTC, and 1,268,771 USDC from the TrustedVolumes resolver contract. According to Blockaid, the exploiter is the same operator behind the March 2025 1inch Fusion V1 incident. This time, the attacker exploited a completely different vulnerability.
The victim resolver contract at 0x9bA0CF1588E1DFA905eC948F7FE5104dD40EDa31 now shows a near-zero ETH balance after the drain.
The exploit began at approximately 00:47 UTC on May 7, 2026, at block 25,039,670. A single key drain transaction moved all four assets out of the victim resolver. The funds passed through a newly deployed intermediary contract before landing at the exploiter’s address.
Blockaid’s detection system flagged the activity and posted a public alert at 01:26 UTC. That came roughly 40 minutes after the initial drain. Security firms Beosin and PeckShield confirmed the findings shortly after and began tracing the stolen funds.
According to PANews, the total loss stands at approximately $5.9 million. The breakdown: roughly $3 million in WETH, $1.37 million in WBTC, and the rest in USDT and USDC stablecoins.
Key milestones related to the TrustedVolumes / 1inch exploit
The first suspicious transaction, identified as the main exploit transaction 0xc5c61b3ac39d854773b9dc34bd0cdbc8b5bbf75f18551802a0b5881fcb990513, drained the bulk of funds from the TrustedVolumes resolver contract 0x9bA0CF1588E1DFA905eC948F7FE5104dD40EDa31 via its custom RFQ swap proxy 0xeEeEEe53033F7227d488ae83a27Bc9A9D5051756.
Roughly 39 minutes after the key exploit transaction, Blockaid published the original alert identifying the ongoing exploit, the exploiter address 0xC3EBDdEa4f69df717a8f5c89e7cF20C1c0389100, the victim contract, the exploit transaction, and the initial drained amount.
The drained assets were reported as 1,291.16 WETH, 206,282 USDT, 16.939 WBTC, and 1,268,771 USDC. Early reporting indicated the funds were swapped into approximately 2,513 ETH. The figure was described as “extracted so far,” with no additional large drains reported after the key transaction.
No public statements, tweets, or updates from @trustedvolumes or @1inch were found during the early monitoring window, while the incident remained less than three hours old.
Etherscan activity on the victim contract showed no clear pause-function calls or official mitigation transactions in the immediate aftermath of the exploit.
Blockaid stated that more details would follow, but no refund negotiations, bounty offer, or post-mortem timeline had been made public. The same exploiter was reportedly linked to the March 2025 1inch Fusion V1 incident, where most funds were ultimately returned after direct negotiation with TrustedVolumes.
To understand this TrustedVolumes exploit, it helps to know how 1inch resolvers work. 1inch is one of the largest DEX aggregators on Ethereum. It routes trades across multiple liquidity sources to find users the best price.
Resolvers are third-party market makers that fill orders within the 1inch Fusion system. They hold funds in smart contracts and settle trades on behalf of users. In return, resolvers earn fees from the spread between quoted and execution prices.
Because resolvers manage their own infrastructure, each one deploys custom smart contracts. These contracts handle quoting, settling, and transferring funds. That design means a vulnerability in one resolver does not necessarily compromise 1inch itself.
The flaw sits in a TrustedVolumes-controlled custom RFQ (request-for-quote) swap proxy contract at 0xeEeEEe53033F7227d488ae83a27Bc9A9D5051756. This is not a bug in 1inch’s core protocol code.
RFQ systems allow resolvers to offer direct quotes for swaps. Instead of routing through AMM liquidity pools, the resolver provides a fixed price for a given trade size. That process relies on the swap proxy contract to handle fund transfers securely.
The attacker appears to have triggered a flaw in this proxy. The malicious interaction forced the resolver to send its held tokens through a newly deployed contract. Those tokens then arrived at the exploiter’s address.
Blockaid said “more details will follow” in its initial alert. Full root-cause details remain pending.
The exploiter address matches the operator behind the March 2025 1inch Fusion V1 incident. In that earlier attack, the attacker targeted an outdated Fusion V1 Settlement contract. The bug involved calldata corruption and an integer overflow in Yul assembly code.
That exploit drained roughly $5 million from TrustedVolumes and smaller market makers. TrustedVolumes recovered most of those funds after a negotiated bounty, according to The Block.
This time, the vulnerability is entirely different. The flaw lies in TrustedVolumes’ own custom RFQ proxy, not in 1inch’s settlement contracts. The repeat-attacker pattern raises questions. Did the March 2025 bounty negotiation give the attacker deeper insight into TrustedVolumes’ infrastructure?
Multiple sources confirm that the losses are isolated to TrustedVolumes’ resolver contract. This exploit does not directly affect user funds on the 1inch protocol.
1inch protocol-level TVL data on DefiLlama does not separate third-party market-maker losses. So far, no other resolvers appear impacted. The 1INCH token price showed no significant reaction in the hours after the exploit, hovering around $0.097.
As of the latest reports, TrustedVolumes, 1inch Network, and Blockaid have not issued official statements beyond the initial detection tweet. Beosin Alert confirmed it is investigating the exploit and tracing the funds.
Whether anyone can recover or freeze the stolen assets remains unclear. The March 2025 incident ended with a negotiated return. There is no guarantee the same outcome will happen again.
On X, sentiment ranges from alarm to dark humor. Several users highlighted the irony of “Trusted” in TrustedVolumes’ name. Security researchers are actively tracing fund flows and flagging the repeat-attacker connection.
The broader reaction centers on DeFi infrastructure risk. Resolvers hold significant funds but may not face the same audit scrutiny as core protocol contracts. This TrustedVolumes exploit shows that third-party market makers represent a real attack surface in aggregator ecosystems.
The immediate priority is a full post-mortem from TrustedVolumes or Blockaid. The crypto community needs to see the exact code path the attacker exploited. Beosin and other security firms continue to trace the drained funds.
If the attacker follows the March 2025 pattern, a bounty negotiation could follow. For resolver operators, this incident is a stark reminder. Custom smart contracts that handle millions in user-adjacent funds demand the same audit rigor as core protocol code.
For now, all eyes are on TrustedVolumes and 1inch Network for an official response.
Our Crypto Talk is committed to unbiased, transparent, and true reporting to the best of our knowledge. This news article aims to provide accurate information in a timely manner. However, we advise the readers to verify facts independently and consult a professional before making any decisions based on the content since our sources could be wrong too. Check our Terms and conditions for more info.


Alephium Bridge Exploited for $815K via Forged VAAs
DxSale Liquidity Drain Hits 1,400 BNB Chain Pools for $7.3M
James Wynn Accused of $WORLD Rug Pull for 3.2 SOL
StakeDAO Exploit Mints 5.4T vsdCRV on Arbitrum
Alephium Bridge Exploited for $815K via Forged VAAs
DxSale Liquidity Drain Hits 1,400 BNB Chain Pools for $7.3M
James Wynn Accused of $WORLD Rug Pull for 3.2 SOL
StakeDAO Exploit Mints 5.4T vsdCRV on Arbitrum