
TransitFinance hacked for $1.88M in DAI after suspected Tron-side exploit, marking the protocol’s third major security breach since 2022.
Author: Akshat Thakur
13th May 2026 – TransitFinance, a cross-chain DEX aggregator, appears to have been hacked for approximately $1.88 million in DAI.
High Signal Summary For A Quick Glance
ME Group
@MetaEraHK
🚨 TransitFinance Reportedly Hacked for ~$1.88M @PeckShieldAlert said @TransitFinance appears to have been hacked for around $1.88M. The stolen funds are reportedly sitting in a single address in DAI. https://t.co/xMXux7XrnH
#PeckShieldAlert @TransitFinance seems to have been hacked for ~$1.88M The stolen funds are currently sitting in the following address in $DAI: 0x8a634DfA2609358849D7D65FFA270C8A57a8abA5 https://t.co/9RSQkgdfX6
12:53 PM·May 13, 2026
PeckShieldAlert
@PeckShieldAlert
#PeckShieldAlert @TransitFinance seems to have been hacked for ~$1.88M The stolen funds are currently sitting in the following address in $DAI: 0x8a634DfA2609358849D7D65FFA270C8A57a8abA5 https://t.co/9RSQkgdfX6
12:21 PM·May 13, 2026
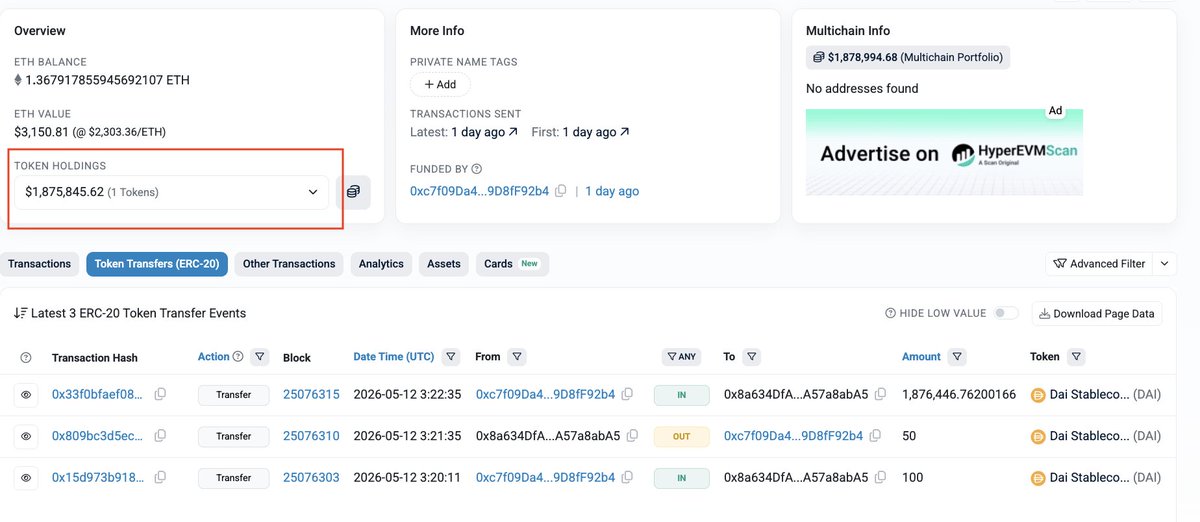
The exploit reportedly originated on the Tron network before the stolen funds were bridged to Ethereum. According to on-chain data, roughly 1,876,496 DAI now sits in a single attacker-controlled address. The funds have not moved since arriving.
PeckShieldAlert flagged the incident on X at 12:21 UTC on May 13, 2026. Earlier that morning, DefimonAlerts identified the attacker address and the on-chain bounty message from the Transit team.
On-chain records show a large DAI transfer into the attacker address on May 12, 2026, at approximately 03:22 UTC. The transfer of 1,876,446.76 DAI came from an intermediary address labeled “TransitFinance Funds Receiver” on Etherscan.
The attack appears to have started on Tron. Multiple security analysts point to address TF9xyLYj8xJ8V7TTLjNB5asVwYz6HV6JoS as the origin. The exact exploit mechanism on the Tron side remains unconfirmed.
The attacker then converted or bridged the proceeds into DAI on Ethereum. The funds landed in a single wallet: 0x8a634DfA2609358849D7D65FFA270C8A57a8abA5. That address also holds about 1.37 ETH, likely used for gas.
As of May 13, 2026, the TransitFinance team has not posted any public statement on X, their blog, or Discord. The only known response is an on-chain message sent directly to the attacker address.
According to security analyst @chrisdior777 (CDSecurity), the message offers a bounty if the attacker returns the funds within 48 hours. The exact terms are visible in the internal transaction data on Etherscan.
This approach mirrors what TransitFinance did after its 2022 hack. In that case, negotiations through on-chain messages and security firm intermediaries helped recover roughly $19 million of the $28.9 million stolen.
This is not the first time TransitFinance has faced a security breach. The protocol, also known as Transit Swap, has a documented history of exploits.
In October 2022, attackers exploited a swap-contract bug and drained approximately $28.9 million. The team worked with PeckShield and SlowMist to negotiate a partial recovery. The hacker eventually returned between $18.9 million and $19 million.
In December 2023, a separate vulnerability involving unvalidated swap-path inputs caused roughly $110,000 in losses across BSC and Ethereum.
Now, in May 2026, the protocol faces its third known exploit. The cumulative pre-recovery losses across all three incidents exceed $30 million. This pattern raises serious questions about the protocol’s audit practices and its ability to secure cross-chain routing logic.
Key milestones in the TransitFinance Exploit History and 2026 Incident
A swap-contract vulnerability allows attackers to drain roughly $21M–$28.9M across Ethereum and BNB Chain.
Security firms help identify the attacker, leading to the return of most stolen funds while TransitFinance pauses operations and begins refunds.
A smaller recovery round adds roughly $246K more to recovered assets as remediation efforts continue.
Attackers exploit TransitFinance again, routing stolen assets through Tron before bridging approximately 1.876M DAI onto Ethereum.
PeckShieldAlert identifies the attacker wallet and estimates losses at roughly $1.88M in DAI, triggering widespread community attention.
The stolen DAI continues sitting inside the attacker-controlled Ethereum address with minimal movement or laundering activity detected.
TransitFinance has not publicly confirmed recovery plans, compensation details, contract pauses, or negotiations with the attacker.
Cross-chain DEX aggregators like TransitFinance operate across multiple blockchains simultaneously. They interact with bridge contracts, token approval systems, and routing algorithms on each chain. That complexity creates a wide attack surface.
Security researcher @TxDesk noted on X that multi-chain exploits represent “the worst case” for affected users. Tracing funds across chains is harder, and recovery options are more limited than single-chain incidents.
The exact vulnerability behind this TransitFinance hack has not been publicly identified. Previous incidents involved approval manipulation and unvalidated inputs. The current exploit may follow a similar pattern, according to analysts familiar with the protocol’s architecture.
Reactions on X reflect a mix of frustration and resignation. Several accounts described the incident as another entry in a growing list of weekly DeFi exploits.
One user wrote: “new hack every damn week.” Others highlighted the irony that the team’s only visible response to affected users is an on-chain message to the attacker.
No major Reddit, Discord, or Telegram discussions have surfaced yet. The incident is less than 24 hours old. Tier-1 outlets like CoinDesk and The Block have not published coverage as of this writing.
The 48-hour bounty window reportedly set by the TransitFinance team creates a near-term deadline. If the attacker does not respond, recovery becomes significantly harder.
For now, the stolen DAI sits untouched. Whether the attacker engages with the bounty offer, launders the funds through a mixer, or simply waits remains unknown.
Users who interacted with TransitFinance on Tron should review their token approvals immediately. Until the root cause is confirmed, revoking approvals for TransitFinance contracts is a reasonable precaution.
Our Crypto Talk is committed to unbiased, transparent, and true reporting to the best of our knowledge. This news article aims to provide accurate information in a timely manner. However, we advise the readers to verify facts independently and consult a professional before making any decisions based on the content since our sources could be wrong too. Check our Terms and conditions for more info.


Humanity Protocol Hack Drains $30M as $H Crashes 90%
Polymarket MicroStrategy Dispute Sparks $500K Loss Claim
Alephium Bridge Exploited for $815K via Forged VAAs
DxSale Liquidity Drain Hits 1,400 BNB Chain Pools for $7.3M
Humanity Protocol Hack Drains $30M as $H Crashes 90%
Polymarket MicroStrategy Dispute Sparks $500K Loss Claim
Alephium Bridge Exploited for $815K via Forged VAAs
DxSale Liquidity Drain Hits 1,400 BNB Chain Pools for $7.3M