
LayerZero DVN vulnerability leaves $4.5B at risk as 47% of OApps still use insecure 1-of-1 setups after the Kelp DAO hack.
Author: Kritika Gupta
Steady attention without excessive speculation.
24th April 2026- The LayerZero DVN vulnerability has emerged as a major systemic risk across the omnichain ecosystem, with more than $4.5 billion in assets still exposed. Recent data from Dune Analytics shows that 47% of active LayerZero OApps continue to rely on 1-of-1 Decentralized Verifier Network configurations. This setup creates a single point of failure, which attackers already exploited in the April 18, 2026 Kelp DAO incident.
High Signal Summary For A Quick Glance
Shawn
@ShawnCT_
@coingecko If teams don't wake up from this "default config" laziness, that $45B is just waiting to become the script for the next DeFi disaster.
07:35 AM·Apr 24, 2026
Cloud
@cloud88609368
@coingecko 47% of OApps still running 1-of-1 DVN in 2026 is actually insane. $4.5B sitting behind a single point of failure isn’t decentralization, it’s a ticking time bomb. Great callout
07:14 AM·Apr 24, 2026
SYNAPZ
@synapz_group
@coingecko This is exactly the kind of fragility people keep ignoring until it blows up. Nearly half of LayerZero OApps running 1-of-1 DVNs means a single point of failure protecting billions. That’s not decentralisation, that’s a bottleneck waiting to be exploited. This is where the https://t.co/4hvSL0yjjB
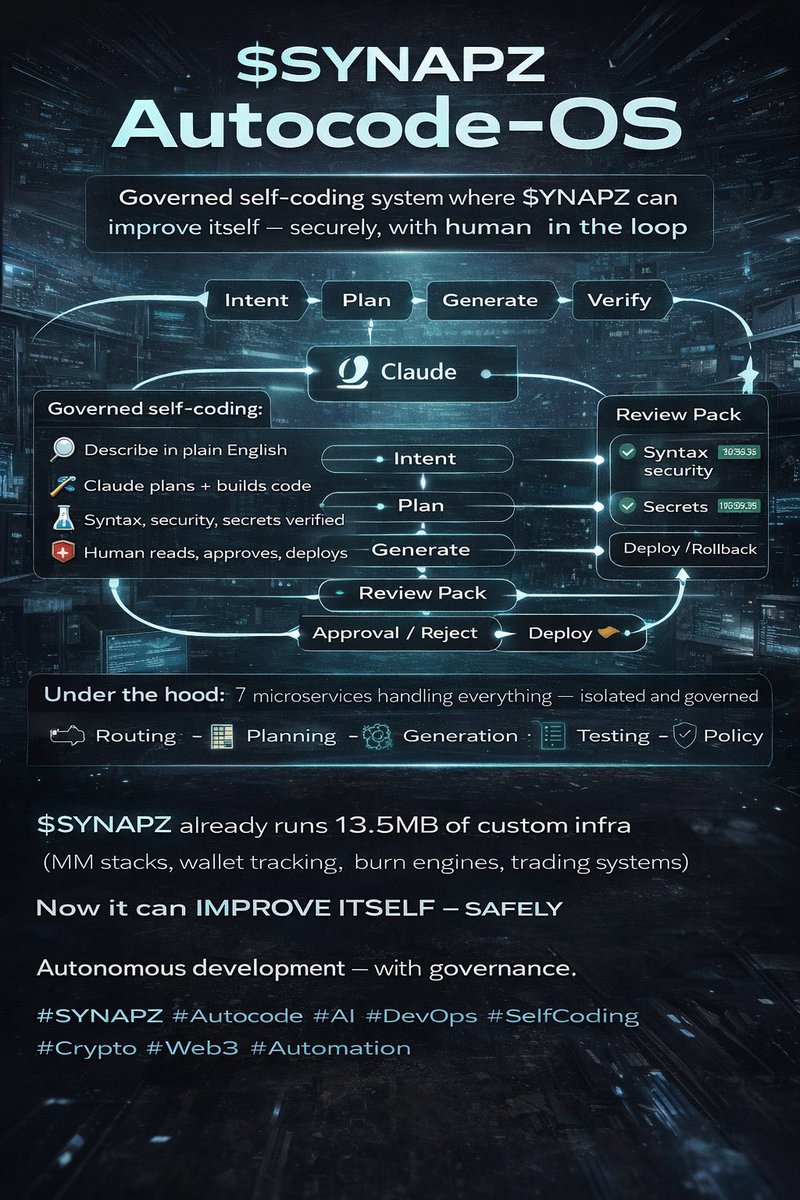
07:09 AM·Apr 24, 2026
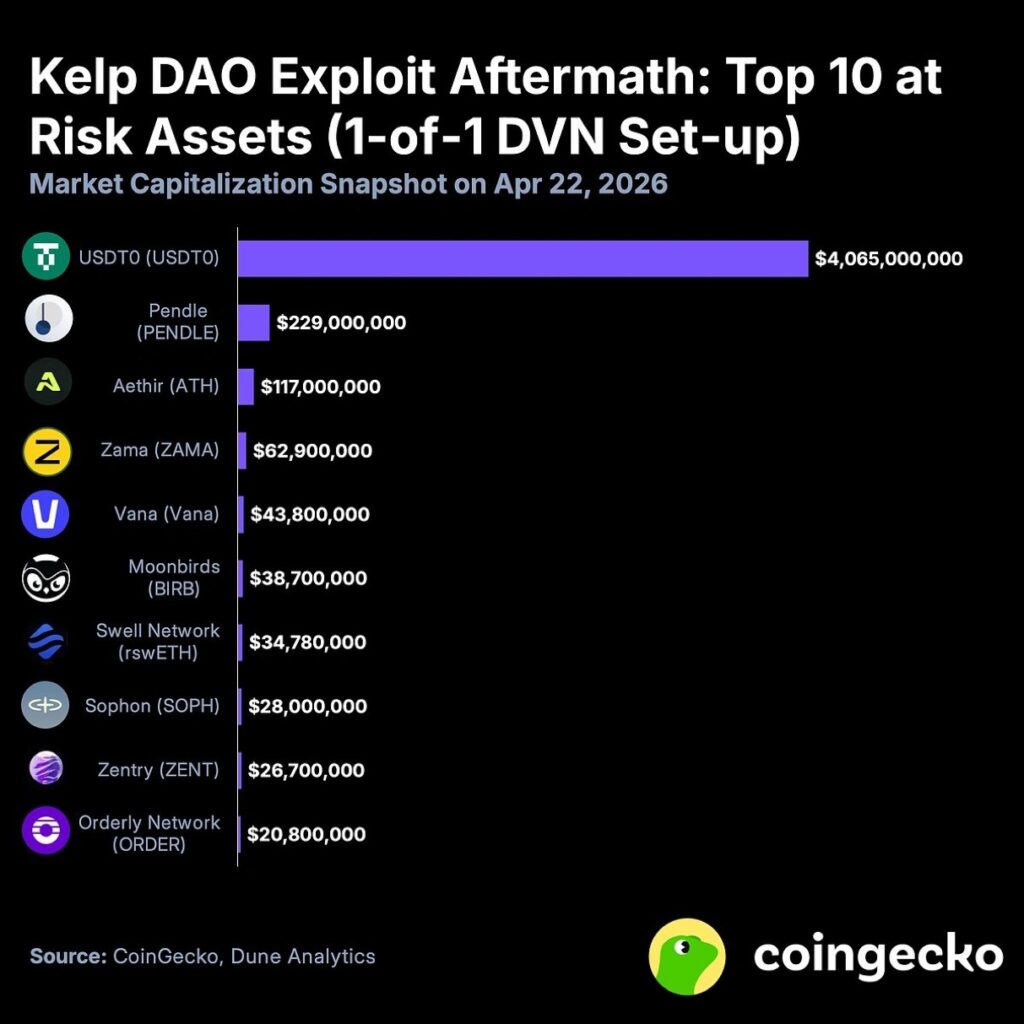
The issue came into focus during the April 18 exploit involving Kelp DAO. Attackers drained approximately 116,500 rsETH, worth around $290 million, from its LayerZero-powered bridge between Unichain and Ethereum. Importantly, the exploit did not target Kelp’s core smart contracts. Instead, it compromised the off-chain infrastructure tied to its 1-of-1 DVN setup.
Attackers manipulated RPC nodes by launching DDoS attacks on primary servers. They then forced failover systems to connect to malicious nodes. This allowed them to inject a forged cross-chain message. Consequently, the destination contract released funds without a corresponding burn on the source chain.
Kelp DAO paused operations within 46 minutes, which prevented additional losses estimated at up to $200 million. However, the damage exposed a critical weakness. Reports widely linked the attack to the Lazarus Group, a North Korea-affiliated hacking organization known for targeting crypto infrastructure.
Soon after, a public dispute emerged between LayerZero Labs and Kelp DAO. LayerZero stated that it had advised using multi-DVN setups. In contrast, Kelp argued that the 1-of-1 configuration matched LayerZero’s default documentation and onboarding guides. Independent researchers confirmed that single-verifier setups appeared in official templates, which strengthened Kelp’s position.
Dune Analytics data highlights that the issue extends beyond a single protocol. Out of 2,665 active LayerZero OApps tracked over the past 90 days, nearly half still use 1-of-1 DVN configurations. Meanwhile, 45% use 2-of-2 setups, and only about 5% rely on stronger configurations such as 3-of-3 or higher.
This distribution confirms that the LayerZero DVN vulnerability is structural rather than isolated. Therefore, the $4.5 billion figure reflects broad ecosystem exposure. If another attacker exploits the same weakness, the impact could scale significantly across multiple protocols.
LayerZero has begun enforcing changes by ending support for 1-of-1 DVN setups. This move effectively forces remaining OApps to migrate toward multi-verifier configurations. Co-founder Bryan Pellegrino has emphasized ongoing efforts to strengthen security across the protocol.
At the same time, Kelp DAO has confirmed that its core restaking contracts remain secure. The team has also called for shared responsibility between infrastructure providers and application developers.
Developers now face clear expectations. They should adopt at least 2-of-2 or stronger DVN thresholds. In addition, they should diversify verifier providers instead of relying on a single operator. Regular audits of off-chain dependencies, including RPC infrastructure, have also become essential.
More broadly, the incident has reignited calls for standardized security baselines in cross-chain messaging. It has also increased pressure for transparency in default configurations.
Our Crypto Talk is committed to unbiased, transparent, and true reporting to the best of our knowledge. This news article aims to provide accurate information in a timely manner. However, we advise the readers to verify facts independently and consult a professional before making any decisions based on the content since our sources could be wrong too. Check our Terms and conditions for more info.

