ZetaChain confirmed an exploit against its GatewayEVM contract , with the attack targeting only internal team wallets.
Author: Sahil Thakur
28th April 2026 – ZetaChain confirmed an exploit against its GatewayEVM contract , with the attack targeting only internal team wallets.
High Signal Summary For A Quick Glance
Wu Blockchain
@WuBlockchain
ZetaChain Pauses Cross-Chain Transactions After GatewayEVM Contract Attack According to ZetaChain, an attack targeted its GatewayEVM contract, impacting only internal team wallets, with no user funds affected. The attack vector has been contained, and no further losses are https://t.co/MszNHtrLwh
09:48 PM·Apr 27, 2026
DEGEN NEWS
@DegenerateNews
NEW: @ZetaChain WARNS "THERE WAS AN ATTACK AGAINST THE ZETACHAIN GATEWAYEVM CONTRACT TODAY THAT IMPACTED THE INTERNAL ZETACHAIN TEAM WALLETS ONLY. WE'VE ALREADY BLOCKED THE ATTACK VECTOR SO NO MORE FUNDS CAN BE COMPROMISED..." https://t.co/4YnfxbmY8p

08:03 PM·Apr 27, 2026
SolanaFloor
@SolanaFloor
NEW: @ZetaChain has reportedly been exploited, with at least $300K drained so far. https://t.co/KcAaB1iOqD

07:58 PM·Apr 27, 2026
Steady attention without excessive speculation.
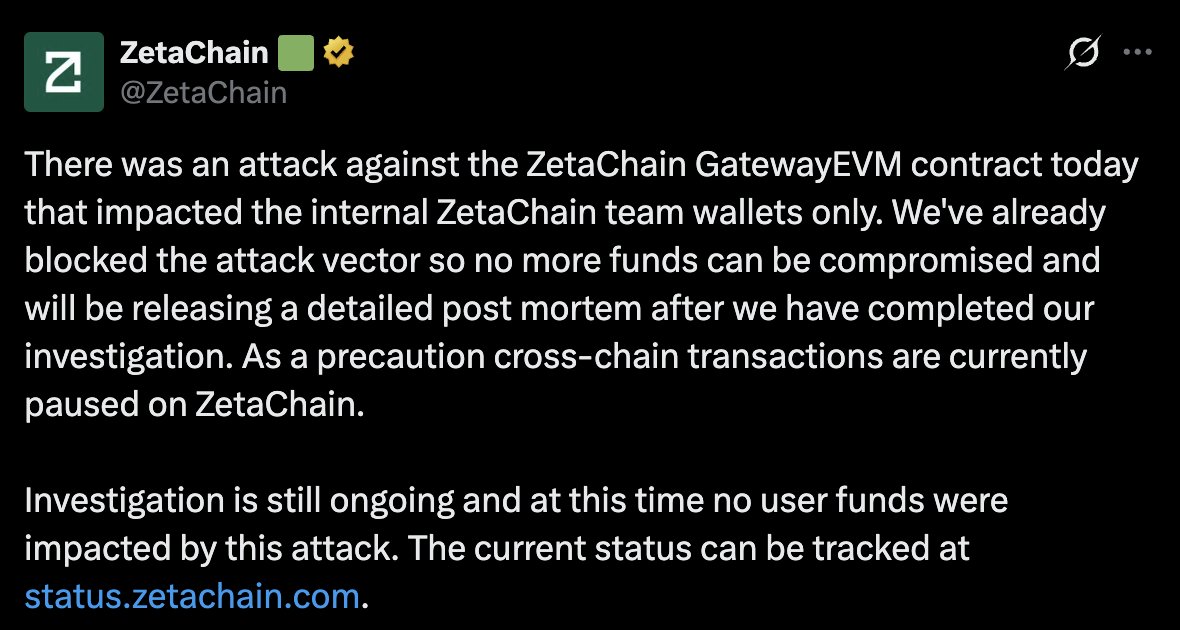
The team posted a public disclosure on X around 19:57 GMT on April 27. According to ZetaChain, the team already blocked the attack vector.
As a precaution, cross-chain transactions on mainnet remain paused while the team develops a patch.
The exploit did not affect user funds or $ZETA token supply, according to ZetaChain’s official statement. The investigation is still ongoing, and a full post-mortem will follow once it concludes.
The GatewayEVM contract is a core component of ZetaChain’s interoperability layer. It handles cross-chain messaging, asset transfers, and interactions between EVM-compatible chains and the network.
Related components like GatewayZEVM::call() allow universal apps to interact across multiple blockchains. These gateway contracts are essential to ZetaChain’s value proposition as an omnichain platform.
Technical details from BeInCrypto point to a vulnerability allowing cross-chain arbitrary external calls. According to those reports, the attacker deployed an exploit contract on ZetaChain that emitted a “Called” event.
That event reportedly triggered ZetaChain’s Threshold Signature Scheme (TSS) to execute malicious transactions on connected chains. The TSS is the mechanism validators use to collectively sign cross-chain transactions.
In effect, the attacker tricked the signing system into executing unauthorized operations. The full technical breakdown should appear in the upcoming post-mortem.
ZetaChain stated that the attack only compromised internal team wallets. Community observers and security analysts, including those tied to Blockaid alerts, estimate the loss at roughly $300,000 (about 139 ETH).
The team has not confirmed a specific loss amount. Reports suggest the attacker moved funds through bridges like Symbiosis and LiFi. One suspected exploiter address referenced in community discussions is 0x00467f5921f1a343b96b9bf71ae7e9054ae72ea4.
ZetaChain blocked the attack vector immediately after detection. The ZetaChain status page tracked the incident as ongoing for more than seven hours, with cross-chain functionality paused on mainnet.
Security firm Blockaid issued an alert on April 27 about the ZetaChain GatewayEVM exploit. The firm advised all users to immediately revoke token approvals for the GatewayEVM contract on every EVM-compatible chain.
This precaution targets anyone who previously interacted with ZetaChain apps or bridges. Revoking approvals removes the contract’s permission to move tokens, which limits exposure to any residual risk.
The $ZETA token dropped about 4.8% in the immediate aftermath. It traded near $0.054 on April 27, with a 24-hour range between $0.053 and $0.059.
According to CoinGecko data, ZetaChain’s market cap sits at approximately $73.3 million. Trading volume reached about $5.8 million over 24 hours. The price impact stayed relatively contained since no user funds were at risk.
This ZetaChain GatewayEVM exploit marks the second cross-chain security incident in April 2026. The KelpDAO bridge exploit earlier this month also targeted interoperability infrastructure.
Cross-chain bridges and messaging layers have historically been among the most targeted DeFi components. High-profile incidents include the Wormhole exploit ($320 million in 2022) and the Ronin Bridge hack ($624 million in 2022).
As the crypto ecosystem becomes increasingly multi-chain, the attack surface for interoperability layers continues to expand. Each new incident adds urgency to the security conversation around cross-chain design.
Cross-chain transactions remain paused on ZetaChain’s mainnet as of April 28. The team is preparing a patch, and a detailed post-mortem will follow once the investigation is complete.
Users can track real-time updates on the ZetaChain status page. Anyone who interacted with the GatewayEVM contract should follow Blockaid’s advice and revoke token approvals.
ZetaChain’s rapid detection and transparent disclosure limited the scope of this incident. The upcoming post-mortem should clarify whether this vulnerability reflects a broader TSS design concern or stays contained to one contract.
This is not financial advice. Always do your own research before making investment decisions.
Our Crypto Talk is committed to unbiased, transparent, and true reporting to the best of our knowledge. This news article aims to provide accurate information in a timely manner. However, we advise the readers to verify facts independently and consult a professional before making any decisions based on the content since our sources could be wrong too. Check our Terms and conditions for more info.


Humanity Protocol Hack Drains $30M as $H Crashes 90%
Polymarket MicroStrategy Dispute Sparks $500K Loss Claim
Alephium Bridge Exploited for $815K via Forged VAAs
DxSale Liquidity Drain Hits 1,400 BNB Chain Pools for $7.3M
Humanity Protocol Hack Drains $30M as $H Crashes 90%
Polymarket MicroStrategy Dispute Sparks $500K Loss Claim
Alephium Bridge Exploited for $815K via Forged VAAs
DxSale Liquidity Drain Hits 1,400 BNB Chain Pools for $7.3M