

Vercel breach exposes npm and GitHub tokens via OAuth attack. Developers urged to rotate keys and secure environment variables immediately.
Author: Kritika Gupta
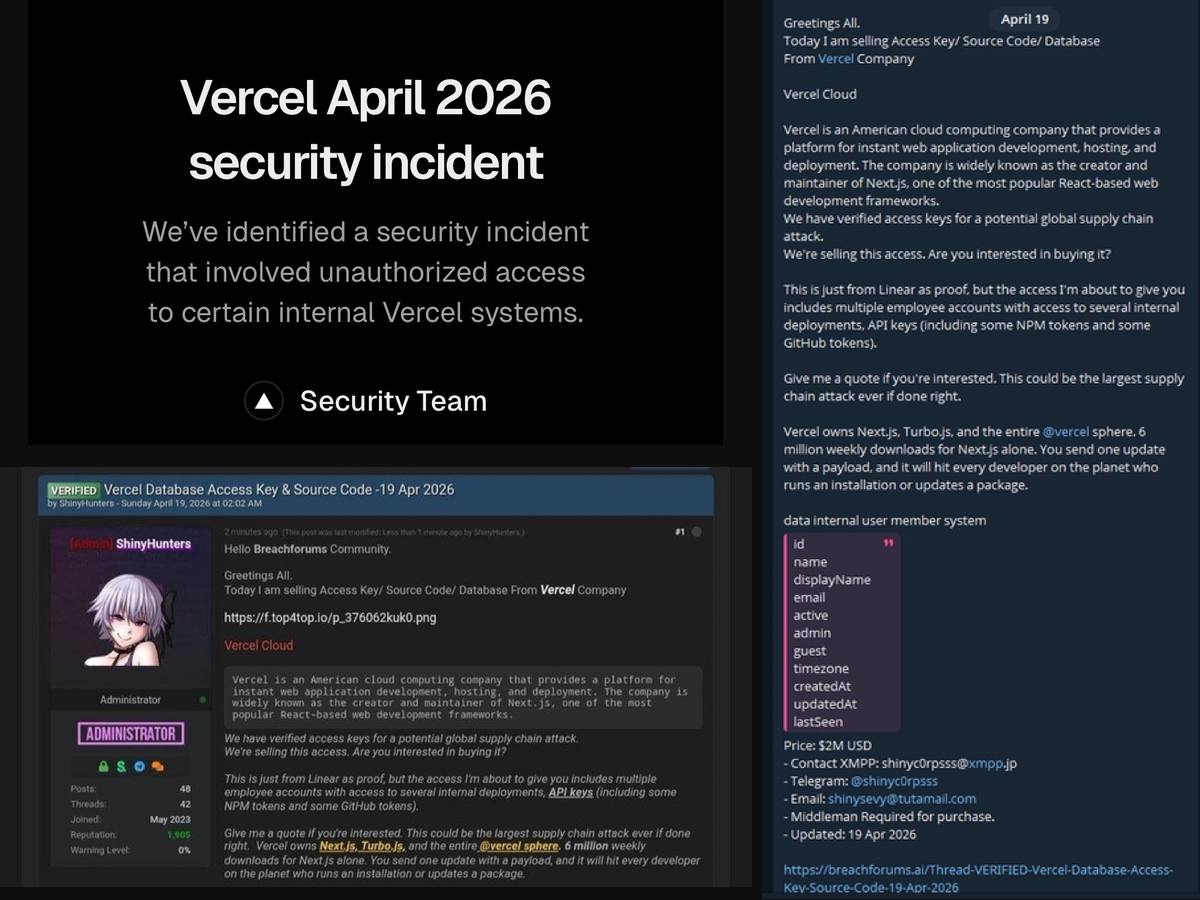
20th April 2026- Vercel confirmed on April 19, 2026, that unauthorized actors accessed parts of its internal systems in what is now widely referred to as the Vercel breach. The company stated that the incident affected only a limited subset of customers and did not disrupt its core deployment platform. However, a seller using the ShinyHunters identity posted on BreachForums, claiming to sell stolen assets for $2 million. These assets reportedly include NPM tokens, GitHub tokens, internal database data, source code, and employee records.
High Signal Summary For A Quick Glance
jussy
@jussy_world
🚨 Another hack just happened @vercel - platform many apps and crypto frontends rely on just got breached 👇 > Internal tools like GitHub + Linear reportedly compromised > Customer data, source code, databases & API keys allegedly accessed > Threat actor now listing/selling https://t.co/4ju7aqRu9S
05:54 PM·Apr 19, 2026
BuBBliK
@k1rallik
VERCEL GOT HACKED ShinyHunters - the group behind the Ticketmaster breach - is selling Vercel's internal database for $2M on BreachForums here's why every developer should care: - they have NPM tokens and GitHub tokens - Vercel owns Next.js - 6 million weekly downloads - one https://t.co/gzhvtHnMRg https://t.co/tAWYZiTSwA

We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems, impacting a limited subset of customers. Please see our security bulletin: https://t.co/0S939n3qHC
03:22 PM·Apr 19, 2026
shirish
@shiri_shh
VERCEL just got breached. They’re selling internal DB + employee accounts + GitHub/NPM tokens for $2M on BreachForums. looks like someone got early access to Claude Mythos 💀 https://t.co/6bJ7Sx9O5M https://t.co/BVCDvoSHfs

We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems, impacting a limited subset of customers. Please see our security bulletin: https://t.co/0S939n3qHC
03:12 PM·Apr 19, 2026
Steady attention without excessive speculation.
The breach originated through a third-party tool called Context.ai. Attackers compromised a Google Workspace OAuth application linked to this tool, which one Vercel employee had authorized. As a result, the attackers gained access to that employee’s account and then moved laterally into Vercel’s internal environment. They were able to enumerate some environment variables that were not marked as sensitive.
Vercel clarified that protected secrets were not accessed. In addition, the attackers did not directly target the core platform. Nevertheless, the incident highlights a growing attack vector through SaaS integrations. The company is now working with Mandiant, law enforcement, and Context.ai to investigate the incident. Early signals suggest that the same OAuth compromise may have impacted hundreds of organizations.
Meanwhile, the ShinyHunters identity has appeared in several major breaches. These include the 2024 Ticketmaster incident involving Snowflake and a recent breach tied to Rockstar Games analytics systems. Therefore, this event fits a broader pattern of supply chain intrusions.
This breach introduces serious supply chain risk, particularly for developers working with modern JavaScript stacks. NPM and GitHub tokens can allow attackers to push malicious updates or access private repositories.
If attackers gain control of a widely used package, they can distribute malicious code across thousands of downstream applications. Therefore, even limited credential exposure can scale into ecosystem-wide impact.
In addition, non-sensitive environment variables may still provide indirect access. These variables can reveal API endpoints, service configurations, or partial credentials that attackers can chain together. Because Vercel powers millions of deployments, especially through Next.js, the blast radius could extend far beyond directly affected accounts. As a result, the incident raises concerns similar to past software supply chain attacks seen across Web2 and increasingly in Web3 infrastructure.
For crypto developers, the risk is even more pronounced. Many DeFi frontends, dashboards, and tooling layers rely on Vercel-hosted environments. Therefore, compromised tokens could expose RPC endpoints, backend APIs, or signing infrastructure if not properly segmented.
Vercel responded quickly by publishing a security bulletin and notifying affected users. The company also shared indicators of compromise and confirmed that services remain fully operational.
CEO Guillermo Rauch publicly acknowledged the Context.ai attack vector, reinforcing transparency around the incident. Developers should act immediately. First, rotate all environment variables, including those previously considered low-risk. Second, revoke and regenerate any associated GitHub and NPM tokens.
Next, audit Google Workspace OAuth permissions. Specifically, check for the Context.ai app ID and revoke access if it appears. In addition, review deployment logs for suspicious activity and tighten access controls across CI/CD pipelines.
Our Crypto Talk is committed to unbiased, transparent, and true reporting to the best of our knowledge. This news article aims to provide accurate information in a timely manner. However, we advise the readers to verify facts independently and consult a professional before making any decisions based on the content since our sources could be wrong too. Check our Terms and conditions for more info.


ZachXBT Exposes US Threat Actor Tied to $19M in Crypto Thefts
ZachXBT Accuses Bitget of Enabling Scams, Names Shawn Liu
Roaring Kitty X Account Hacked to Launch $RKC Token
Huma Finance Hit by $101K Legacy Contract Exploit
ZachXBT Exposes US Threat Actor Tied to $19M in Crypto Thefts
ZachXBT Accuses Bitget of Enabling Scams, Names Shawn Liu
Roaring Kitty X Account Hacked to Launch $RKC Token
Huma Finance Hit by $101K Legacy Contract Exploit