
Author: Tanishq Bodh
25th April 2026 – DeFi lending protocol Purrlend lost roughly $1.52 million on Saturday. An attacker drained funds across its HyperEVM and MegaETH deployments through an apparent multisig permission exploit.
High Signal Summary For A Quick Glance
The Purrlend team moved quickly to contain the damage. The protocol paused all operations and posted a brief statement on X around 9:10 a.m. UTC.
“We have detected irregular activity on the protocol and are actively investigating,” the official @purrlend account wrote. “The protocol has been paused for the time being.”
Purrlend is a non-custodial lending and borrowing platform built for leveraged yield strategies. It operates on Hyperliquid’s HyperEVM and on MegaETH, a high-performance chain.
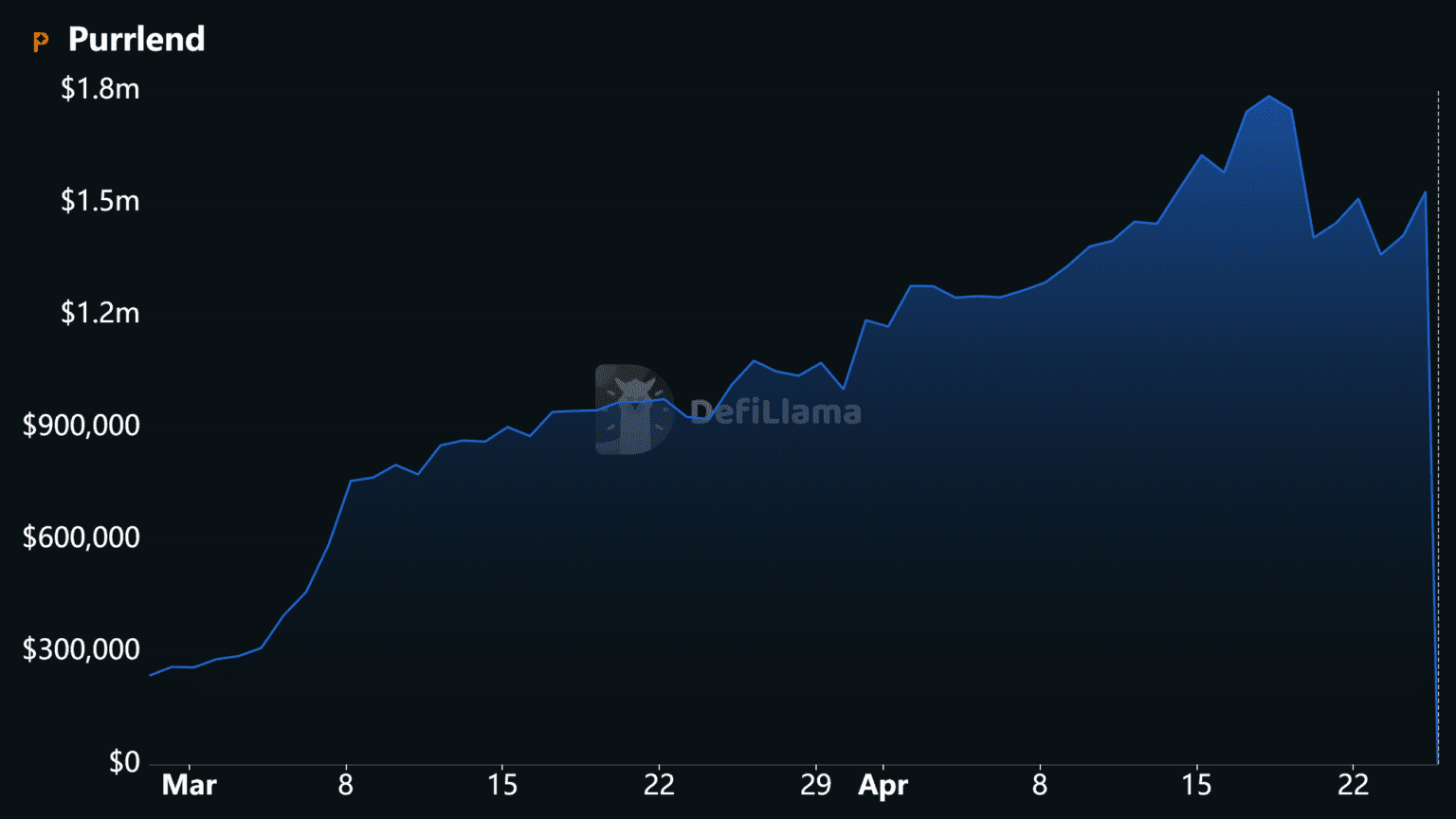
Prior to the incident, its total value locked sat at approximately $1.5 million, according to DefiLlama. That figure has since collapsed to roughly $444,000.
On-chain investigator @kirbyongeo shared a detailed breakdown of the stolen funds. On HyperEVM, the attacker extracted 449,684 USDC, 214,125 USDT0, and 194,745 USDH, along with smaller amounts of wrapped native tokens.
On MegaETH, the haul included 163,169 USDT0, 36.86 WETH, and 75,745 USDm. The total loss across both chains reached $1,522,038.
Both chain explorers show the exploiter wallet addresses publicly. Still, no one has recovered any funds so far.
Unlike many recent DeFi incidents involving smart-contract vulnerabilities, this Purrlend exploit appears to stem from an operational failure. According to community observers, the protocol used a 2-of-3 admin multisig without a timelock.
Roughly eight hours before the drain, the multisig reportedly added the attacker’s address as a “bridge” role. That role apparently inherited elevated permissions from an older Aave-style implementation. As a result, the attacker gained unauthorized access to liquidity-pool assets.
A timelock would have given the community a window to review the suspicious role change. Without one, the transaction executed immediately.
The Purrlend exploit lands in what analysts call the worst month for DeFi security ever recorded. April 2026 losses already exceed $600 million across more than a dozen separate incidents.
The two largest hits came earlier this month. Drift Protocol lost $285 million on April 1 after an attacker compromised admin keys through social engineering. Then on April 19, an attacker drained $292 million from KelpDAO through a bridge validation weakness.
The KelpDAO hack alone triggered $8.45 billion in deposit exits from Aave within 48 hours, according to CoinDesk. As a result, total DeFi TVL dropped by $13.21 billion in that window.
Purrlend’s TVL drop reflects immediate depositor flight. Meanwhile, the pause has frozen remaining assets inside the protocol. No user funds outside the exploited pools appear directly compromised, according to early analysis.
As of late Saturday, the protocol remains offline. Users with open positions on either HyperEVM or MegaETH cannot access deposits, borrows, or withdrawals. The team has not released a post-mortem, recovery plan, or compensation details.
The Purrlend breach highlights a recurring problem in DeFi. A 2-of-3 multisig with no timelock gives attackers a real window to execute malicious transactions before anyone can respond.
Timelocks add a mandatory delay between when a transaction is proposed and when it executes. During that delay, community members and security monitors can flag suspicious activity. In practice, many established DeFi protocols treat timelocks as a baseline security measure.
The rapid succession of exploits this month has intensified scrutiny on admin controls. In particular, newer Layer-1 ecosystems like HyperEVM and MegaETH are still building the security infrastructure that older chains developed through years of battle-testing.
The DeFi community is watching @purrlend for the next official update. A full post-mortem would clarify whether the multisig compromise resulted from an insider or an external attack.
In the meantime, the Purrlend exploit reinforces a clear lesson. Operational security, not just smart-contract audits, determines whether user funds stay safe. For protocols on emerging chains, that lesson is especially urgent.
Our Crypto Talk is committed to unbiased, transparent, and true reporting to the best of our knowledge. This news article aims to provide accurate information in a timely manner. However, we advise the readers to verify facts independently and consult a professional before making any decisions based on the content since our sources could be wrong too. Check our Terms and conditions for more info.


Polymarket MicroStrategy Dispute Sparks $500K Loss Claim
Alephium Bridge Exploited for $815K via Forged VAAs
DxSale Liquidity Drain Hits 1,400 BNB Chain Pools for $7.3M
James Wynn Accused of $WORLD Rug Pull for 3.2 SOL
Polymarket MicroStrategy Dispute Sparks $500K Loss Claim
Alephium Bridge Exploited for $815K via Forged VAAs
DxSale Liquidity Drain Hits 1,400 BNB Chain Pools for $7.3M
James Wynn Accused of $WORLD Rug Pull for 3.2 SOL